Features
Access to Canadian records of Nazi war criminals
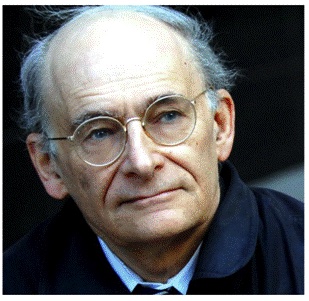
Introduction: Following upon the huge embarrassment caused not only to the Canadian Government, but to Canada as a whole, by the decision to invite a former member of a Ukrainian Waffen SS unit into the House of Commons where he was applauded as a “war hero,” we asked David Matas, renowned lawyer and expert on the issue of Nazi war criminals who were allowed into Canada following World War II, to write a piece providing an analysis how Canada has failed so badly, not only to prevent Nazis and individuals who cooperated with the Nazi regime, to enter Canada, but also to continually refuse to identify who those individuals were. Following is David Matas’s piece:
Getting access to Canadian Nazi war criminal records has to date been nearly impossible. Efforts to obtain access to relevant files and documents have been constantly frustrated and gone nowhere. The record is this.
On January 12, 2022, B’nai Brith Canada put in a request to Library and Archives Canada for Part II of the Report of the Commission of Inquiry on War Criminals. Part I was public in 1986 when the Commission reported. Part II was confidential.
Part II contained, according to Part I, 822 opinions on individual cases. The Commission recommended that the Government give “urgent attention” to investigating 20 files of alleged Nazi war criminals who might still be living in Canada. The report also recommended further investigation of 218 other possible Nazi war criminals living in Canada.
What happened to the 20 cases which were recommended for urgent attention and the further 218 which were recommended for further investigation? We have no idea. We know that there some cases which went to Court and we have the Court records of those cases. But which of these were part of the 20 or 218, if any, were not disclosed.
As of today, Library and Archives Canada, one year and ten months later, has not responded to the request for Part II, other than to acknowledge receipt and assign the request a file number. B’nai Brith Canada complained on December 5, 2022 to the Office of the Information Commissioner asking the Commissioner to issue an order setting a deadline for Library and Archives Canada to provide B’nai Brith with a copy of the Part II Report. That complaint, as of today, has not been decided.
Also on January 12, 2022, B’nai Brith Canada put in a request to Library and Archives Canada for records relating to investigations of alleged Nazi war criminals of the War Crimes Unit of the Department of Justice and the RCMP. Canada’s Program on Crimes Against Humanity and War Crimes Eighth Annual Report 2004-2005 stated that, since beginning this work, the Department of Justice had opened and examined over 1,800 files. Who are these people? What was the result of the investigations in these cases?
With that request too, Library and Archives Canada has not responded, other than to acknowledge receipt and assign the request a file number. B’nai Brith Canada complained as well on December 5, 2022 to the Office of the Information Commissioner asking the Commissioner to issue an order setting a deadline for Library and Archives Canada to provide B’nai Brith with copies of the war crimes records. That complaint, as of today, has, like the other complaint, not been decided.
B’nai Brith Canada on March 6, 2023 asked for an unredacted copy of Library and Archives Canada the September, 1986 report prepared by Alti Rodal titled “Nazi War Criminals in Canada: The Historical and Policy Setting from the 1940s to the Present” prepared for the
Commission of Inquiry on War Criminals. Justice Jules Deschênes who headed the Commission of Inquiry on War Criminals recommended release of the report in its entirety. He wrote: “This substantial study no doubt constitutes an outstanding contribution to the knowledge of this particular question and deserves wide distribution.”
Library and Archives Canada provided B’nai Brith Canada on July 5th 2023 a redacted copy of the report, albeit with fewer redactions than there were at the time of the original release of the report. B’nai Brith Canada complained to the Office of the Information Commissioner within 30 days of the refusal to release the unredacted report. That complaint remains undecided.
The 2000 International Holocaust Remembrance Alliance Stockholm Declaration commits the signatories to “take all necessary steps to facilitate the opening of archives in order to ensure that all documents bearing on the Holocaust are available to researchers.” Canada joined the Alliance in 2009.
The International Holocaust Remembrance Alliance Monitoring Access to Archives Project recommended in 2017 that governmental archival institutions “release Holocaust related records, irrespective of any personal identifying information or national security classifications”.
The US Nazi War Crimes Disclosure Act of 1998 created an interagency war criminals records working group to locate, identify, inventory for declassification and make public all classified Nazi war criminal records. The records subject to the Act include records of the assets of persecuted persons. The Act kept existing exemptions to disclosure in general laws, but required that they be strictly defined, with a presumption against the exemptions.
In addition to general requirements of strict definition and presumption against the exemptions, some of the exemptions were themselves redefined to limit their scope. The exemption from disclosure in favour of privacy is redrafted to become an exemption where there would be “a clearly unwarranted invasion of personal privacy”. The exemption in favour of national security interests is redrafted to become an exemption where disclosure “would clearly and demonstrably damage the national security interests of the United States”. The exemptions in favour foreign relations and diplomatic activities is redrafted to become an exemption where disclosure “would clearly and demonstrably damage” foreign relations or diplomatic activities. The exemption in favour of emergency preparedness plans is redrafted to become an exemption for information that “would seriously and demonstrably impair” those plans.
The records which were disclosed as a result of US Nazi War Crimes Disclosure Act give us an insight into why the documents were withheld. One set of documents showed that the US Government had a lot more detailed knowledge of the Holocaust while it was happening. Keeping this information confidential and not acting on it at the time, whether or not it fits arguably within any of the exemptions, does make the US government of the time look bad. There is presumably similar information in currently withheld documentation of other governments.
A second set of documents initially withheld and then disclosed through the US legislation was documents showing that the Government was providing haven for those complicit in Nazi war crimes because of their potential to assist the US in the Cold War. Again this sort of information now withheld may well be found in other archives.
A third set of documents initially withheld and then disclosed because of the legislation were documents which showed the initial unwillingness to bring Nazi war criminals to justice, and the argumentation both for and against within the government. This argumentation we know has been replicated elsewhere.
A fourth set of documents not yet fully available relates to the effectiveness and operational difficulties of Nazi war crimes prosecution efforts once those efforts got going. In Canada, there was a split between the investigation and prosecution efforts, with investigations allocated to the national police, the Royal Canadian Mounted Police and prosecution allocated to the Department of Justice. This fragmentation caused a sequence of operational difficulties about which we now have only partial knowledge.
There was also in Canada internal feuding within the Nazi war crimes Justice department unit, arguments whether the unit was too slow and cautious or overly energetic in the pursuit of their efforts. The documents we have now provide only a glimpse of this feuding.
A sixth set of documents not now completely disclosed is efforts of Nazi war crimes prosecution units that were established to obtain access to relevant documents in the Soviet Union and Eastern Europe. We know that there was a good deal of difficulty in getting that access and that eventually international agreements were negotiated that allowed foreign war crimes units direct access to those archives rather than working through local archivists. Again, this is a story which could be fully told only with release of all relevant documents.
A seventh difficulty is the inclination of archivists, government officials and Parliamentarians to address the difficulties in access to documentation all at once. Yet, attempting to do everything before one does anything is a recipe for doing nothing. Each request is particular, not least in the archival access issues it presents. An effort to resolve all these myriad issues in one fell swoop goes nowhere.
We can see in several countries self-exoneration and blame shifting as a form of Holocaust distortion. Everywhere the Nazis went they relied on local collaboration to identify, locate, detain and murder the Jewish population. What we see now in several countries is an effort to pretend that the locals were innocent, that the only perpetrators were the invading Nazis.
This whitewashing is not confined to the countries invaded. It is an attitude held within the populations which have emigrated from the invaded countries. This attitude had generated opposition to the effort to bring Nazi war criminals to justice and now generates opposition to disclosure of archives about those efforts.
Canadian privacy law allows for the lapse of the right to privacy twenty years after death. However, in the case of Nazi war criminal files, since the names of those, other than those whose cases have gone to court, are not known, neither is their dates of death. While the dates of death are not known to outsiders, they are either known or knowable to archivists.
The situation justifies these recommendations:
1) Obstacles to access to Nazi war criminal records stem from legislation which is general in nature. There needs to be legislation which is specific to Holocaust records and which provides an exception to these general requirements. The legislation needs to encompass Holocaust related archives concerning both perpetrators and victims.
2) National archives need to establish and maintain separate Holocaust records within their general collections.
3) Insofar as there is discretion in current legislation to allow for exceptions to prohibitions to access, that discretion should be exercised in favour of access to Holocaust related records, including Nazi war crimes records.
4) Parliament can obtain documents from Governments which the public can not obtain. Parliament should exercise that power to obtain Holocaust related records.
5) The public interest in access to Nazi war criminal files should prevail over the right to be forgotten.
6) There needs to be active review of Nazi war criminal files both to make publicly available the files where the dates of death are known and the fixed periods after dates of death in privacy legislation have passed, and to determine whether any of those to whom the files relate are still alive or, if dead, the dates of death, where the deaths or dates of death are not known.
Canada, as a member of the International Holocaust Remembrance Alliance, is committed to Holocaust remembrance. To remember the Holocaust, we must remember the victims. We must also not forget their murderers. While the murderers are alive, that means bringing them to justice. Once they are gone, it means providing public access to the record of their atrocities.
During the Holocaust, the murderers were in Europe. After the Holocaust, the murderers scattered around the world to escape justice. Thousands came to Canada. Howard Margolian, a historian with the War Crimes Unit with the Department of Justice, in his book Unauthorized Entry, estimated that 2,000 Nazi war criminals and collaborators entered Canada after World War II.
It is understandable that files about individuals who are still alive are not made accessible to the public unless there is legal action. But once the individual has died, there is no reason why the file could not be made public, no matter what the state of the evidence about the individual. Not doing so amounts to covering up the haven Canada has given to those complicit in Nazi war crimes with a blanket of secrecy.
Philosopher George Santayana wrote: “Those who cannot remember the past are condemned to repeat it.” Yet, we can not remember a past which remains hidden from us. To remember the past we must know the past. Only through public access to Holocaust archives can we learn lessons from those archives.
Learning lessons from the Holocaust is a legacy we can create for the victims, creating meaning from the senseless death of innocents. To learn those lessons, we need access to the archives which can convey them.
The effort at understanding, of learning the lessons from the Holocaust must never stop. For that history to be written, the files of those against whom there is compelling evidence of complicity in Nazi war crimes and who are now dead must be made public.
We have a duty to the victims, not just to remember that they died, but why they died, how they died. The picture of memory we paint must be real and complete. That picture must include the murderers.
Because we will soon be at a stage where the memory of the Holocaust conveyed by survivors will no longer be with us, access to Holocaust archives looms in importance for keeping the memory of the Holocaust alive. Access to Holocaust archives should be a matter of priority to Governments, Parliaments and archival collections.
David Matas is a Winnipeg lawyer and senior honorary counsel to B’nai Brith Canada
Features
Monitored phone calls and fear of arrest: What life looks like for Iran’s Jews now

This story was originally published in the Forward. Click here to get the Forward’s free email newsletters delivered to your inbox.
Amid the war in Iran, one Iranian Jewish woman who lives in the United States, but whose family remains in Iran, has been wracked with fear. Before the ceasefire, she spoke with her parents once a week for exactly one minute — both because of the exorbitant cost, about $50 per minute, and because of the fear of surveillance.
During one call a few days into the war, she said, something felt off.
“I could see that something is so wrong. It’s as if someone was there,” the woman, who moved to the U.S. in 2008, said in an interview with the Forward. “It seemed like my mom was actually reading from a note.”
She later learned that the Islamic Revolutionary Guard Corps had come to her parents’ home, questioning why they frequently called an American number. They instructed her parents to download Bale, an Iranian messaging app widely believed to be monitored by authorities, before making any further calls.
“It’s a spy app, and everyone knows that,” the woman said with a wry laugh. Her parents refused. Instead, they were told to call their daughter and read from a script while IRGC members watched.
“Basically, they said to prove that you are with us and not with Israel, read this when you call her,” the woman said. “After that day, they didn’t call for a long time.”
Eventually, she learned that her parents had fled to a safer part of the country to escape bombardment.
Her family are among the estimated 10,000 Jews who still live in Iran, in the largest Jewish community in the Middle East outside of Israel. Once numbering around 120,000, the community has dwindled significantly since the 1979 Islamic Revolution, when life for religious minorities fundamentally changed. Today, Jews who remain in Iran must carefully navigate life under the regime, publicly expressing loyalty to avoid being falsely accused of Zionist espionage.
Amid Iran’s war with the U.S. and Israel, that pressure has intensified.
With an ongoing internet blackout, communication is limited and closely monitored. To understand what life is like for Iranian Jews today, I spoke with several people in the U.S. who remain in sporadic contact with family members inside Iran. Everyone interviewed requested that they not be identified, fearing repercussions for either themselves or their families.
A synagogue vigil for the Supreme Leader
On April 16, Tehran’s Yusef Abad synagogue held a memorial for Ayatollah Ali Khamenei, who was killed on the first day of the war. The event was attended and reported on by several state-affiliated media channels, filming as participants from Iran’s Jewish community shared their appreciation for the deceased Supreme Leader.
Inside and around the synagogue, posters featuring photos of Khamenei were displayed alongside Farsi slogans like “Unity of Iran’s faiths against aggression — condemnation of the attack on the Tehran synagogue by the child-killing Zionist regime and criminal America” and “The Jewish faith is separate from Zionism.”
Regime media pointed to the vigil as evidence of Jewish support for Iran’s theocratic government. But experts say that interpretation misses the reality.
Beni Sabti, an Iranian-born analyst at Tel Aviv’s Institute for National Security Studies, said displays like the synagogue vigil are often a matter of survival. Jews who remain in Iran are frequently compelled to demonstrate loyalty to the regime — and opposition to Israel — in order to avoid suspicion of having ties to Israel. Allegations of such ties have often led to imprisonment and executions following the Islamic Revolution in 1979.
To protect the community, Jewish leaders — especially rabbis — often participate in pro-regime events, including memorials for senior regime figures. In some cases, Iranian rabbis have even sat alongside members of Hamas and Hezbollah to pay their respects to senior IRGC commanders responsible for funding and training terror groups across the Middle East.
The regime exerts significant pressure to stage these displays, Sabti said, “because it’s good for them to show the world, ‘You see, we don’t oppress anyone.’”
Beyond public displays, much of Iran’s economy is tied to the state — what officials often describe as a “resistance economy.” In that system, some say, expressions of loyalty can become intertwined with economic survival.
The woman who left Iran in 2008 said one of her relatives was once pressured to confiscate land from dozens of people and transfer it to the government in order to keep his job — a loyalty test she says was especially harsh because of his Jewish identity. “In the job interview, they told him, you have a Jewish background, so you have to first prove how far you will go,” she explained.
Since the 12-Day War between Israel and Iran in June 2025, the situation has grown even more tense. More than 30 Jewish Iranians were reportedly detained during that conflict because of alleged contact with Israel. While some Jewish community members were arrested during the wave of anti-regime protests that occurred at the beginning of the year, Sabti said he has not heard of a similar wave of arrests during the current war.
Still, the fear remains.
Synagogues as shelter
Some Iranian Jews have managed to stay in touch with relatives via landline phones, although calls are expensive and likely monitored. Most avoid discussing politics, using their limited time simply to confirm they are alive.
“After the 12-Day War, people really didn’t talk on the phone,” said the woman who moved to the U.S. in 2008. “We do talk, it’s not like they literally cannot, it’s just like they realized that the scrutiny was so high that no one has meaningful conversations.”
Even so, fragments of sentiment emerge.
One 25-year-old Iranian Jew from Los Angeles said his Jewish cousins in Iran cried tears of joy when they heard of the Ayatollah’s death.
He said his great uncle and cousin told him over the phone, “I don’t care, whatever the cost. If you can eliminate Khamenei, if you can eliminate Mojtaba, his son, if you can eliminate any threat… do it.” He added, “Most Persian Jews in Iran are happy, is what I hear.”
Amid the current ceasefire, a 64-year-old Iranian Jewish woman from LA said her Jewish friends in Iran have expressed relief. “They are happy that the situation is calm, but on the other hand, nobody is happy. They all want it to get finished,” she said, adding that they hope for “regime change.”
For Nora, an Iranian Jew living in New York, the war has come at a time of crisis for her family in Iran. She says her aunt has been focused on caring for her son, who is suffering from bone marrow cancer. Because the family keeps kosher, her aunt has had to leave the house — even during bombardments — to ensure he has food and other necessities.
Around three weeks into the war, her house in Tehran was destroyed after a nearby police station was struck. She briefly moved into a local synagogue; now, she lives with another Jewish family who opened their home to her. Her son remains too sick to leave the hospital.
A synagogue destroyed
Nora’s aunt is not the only Iranian Jew to find shelter in a synagogue. Sabti heard from another Jewish family inside Iran that Jewish communities have been using synagogues as bomb shelters throughout the war. He recalled doing the same during his youth at the time of the Iran-Iraq war that began in 1980.
Beyond using the space for physical safety, synagogues have also become a place for Jews to be together during the difficult time. “They come just to gather there, passing the time, meeting and having a little bit better time together,” he said.
For members of the Rafi’ Nia synagogue, a 150-year-old religious institution in Tehran, this sense of comfort has disappeared. On April 6, the community gathered there for Passover services. The next morning, they learned the building had been destroyed by an Israeli strike.
The Israel Defense Forces said that the target of the strike was not the synagogue, but rather a top commander from Khatam al-Anbiya, Iran’s military emergency command. But Iranian media suggested that the IDF had intentionally targeted the building. The head of the synagogue made a statement condemning the attacks and wishing the Iranian regime success in the war.
The woman who immigrated in 2008 had visited the Rafi’ Nia synagogue during Passover around 10 years ago. She described it as a beautiful old building. Seeing images of its destruction brought back painful memories of her family’s past.
She and her family were forcibly converted to Islam around 70 years ago, she said, with one uncle publicly hanged after he refused to convert. Her family continued practicing Judaism in secret — celebrating Shabbat behind locked doors and in her grandmother’s basement, always afraid.
She believes her family became a target for conversion after the synagogue in their area was destroyed, leaving them without formal affiliation to a recognized religious institution. On two occasions, she said, the IRGC raided their home during Jewish holidays, searching for evidence of religious practice. When they found a menorah, her father was detained. “When my dad came back, he was a ghost.” She fears that members of the destroyed synagogue could now face a similar vulnerability.
In Iran, certain religious minorities, including Jews, are constitutionally recognized. But she says that their protection is closely tied to existing institutions.
“When we talk about the lack of protection, it has a very nuanced meaning. In Iran, this doesn’t mean that the synagogues cannot exist, but it means that the existing synagogues are the only legal protection that Jews do have,” she said. “Good luck with rebuilding that place. Good luck with asking for a new synagogue.”
Sabti said the regime has already used the synagogue’s destruction as propaganda, publicly condemning the attack while reinforcing the state narrative of religious inclusion. “The head of the Islamic clerics condemned Israel and paid condolences to the Jews,” he said. “Everyone pays condolences and says, ‘Oh, sorry, we are in this together’ … but everyone knows that the other one also is lying.”
An American Jewish detainee
For one Iranian American Jew, the war has made a dire situation worse.
Kamran Hekmati, a 70-year-old Iranian American from Great Neck, New York, traveled to Iran in June 2025 and was detained during the 12-Day War. According to advocates, his alleged crime was traveling to Israel 13 years earlier for his grandson’s bar mitzvah.
Kieran Ramsey of the Global Reach advocacy group, who represents Hekmati’s family, said in an interview that Kamran being the Iranian regime’s only Jewish American prisoner puts him in a particularly precarious position. “There can be risk of retribution or reprisals against him at any moment,” Ramsey said, “from prison guards or other prisoners…his identity certainly puts him at higher risk.”
On March 16, almost three weeks into the war, Secretary of State Marco Rubio designated Hekmati as wrongfully detained, a status that allows the federal government to deploy all possible levers — diplomatic, legal, and economic — to secure his release. Ramsey says that change in designation is helpful, but only goes so far.
His organization is now pushing for the release of all American prisoners in Iran to be an integral part of the U.S.-Iran negotiations to end the war.
“Our hope is that Kamran Hekmati and the other Americans that are being held are put to the front of the list in terms of issues to decide, and not as a deal sweetener,” he said adding, “We know the U.S. negotiators have a list of American names. We know Kamran is at the top of that list…. We also know there are some very rational actors inside the regime, and we are trying to convince them that you have a no-cost way to open doors. Use Kamran as that no-cost way.”
The last time the woman who emigrated in 2008 visited Iran was two years ago. Even then, she worried that photos taken of her in the U.S. wearing a Jewish star necklace might draw the regime’s suspicion.
Now, she believes whatever space existed for quiet concessions from the Iranian government to Jews may disappear. The regime’s efforts to retain a firm grip on the Iranian people following January’s massive anti-regime protest wave and the war pose new risks.
“Just because of everything that has happened… I’m sure that any type of like ‘OK, let this go,’ ‘Let this person go,’ will end,” she said.
“Now I know that I could not go back,” she added. “I really feel if the Islamic Republic stays — and they probably have a good chance of staying — I feel like I lost Iran.”
This story was originally published on the Forward.
Features
‘Don’t give up on us now’: Israel peace summit convenes thousands to aim for elusive progress

By Rachel Fink April 30, 2026
This story was originally published in the Forward. Click here to get the Forward’s free email newsletters delivered to your inbox.
TEL AVIV, ISRAEL — On Thursday’s bright, sun-drenched morning during a rare pause in the multi-front war Israel has been locked into for nearly three years, in between the protests, funerals and steady drumbeat of violence and trauma, something decidedly more hopeful was taking place.
In one of the city’s largest conference centers, thousands gathered for the third annual People’s Peace Summit under the banner “It must be. It can be. It will be.” The event was organized by the It’s Time coalition, a partnership of more than 80 grassroots peacebuilding and shared society organizations.
Young activists in T-shirts representing their various causes stood alongside older attendees, some in kippot, others in hijabs. Diplomats in business attire moved through the crowd, as did the handful of Israeli politicians still publicly associated with the peace camp – familiar faces in a political landscape where their ranks have thinned considerably. Outside the main arena, Hebrew mingled with Arabic and English as participants strolled through art installations and an organizational fair showcasing the work of It’s Time’s partners.
While previous events took place at the height of war — while hostages remained in captivity and Gaza endured devastating destruction — this year’s summit unfolded during a fragile lull in fighting, the tenuous ceasefires with Hamas, Hezbollah, and the Islamic Revolutionary Guard Corps allowing, however briefly, for conversations to move beyond issues of immediate survival. Speakers tackled settler violence in the West Bank, looming elections, the immense challenge of rebuilding Gaza and the broader question of how to move Israel and Palestine beyond its default state of perpetual conflict. Inside the packed sessions, the tone was equal parts practical, sober and hopeful.
After a quick coffee break, the thousands of participants came together for an evening of stirring speeches and raucous musical performances. When Israeli pop icon Dana International took the stage with a familiar anthem of peace, the crowd rose to its feet, wrapping their arms around one another and belting out the words.
Despite the joyous atmosphere, the event — and the coalition behind it — is not immune from criticism. Some critiques appear to have been internalized: this year’s programming leaned more heavily into policy, strategy and the hard realities of war than previous gatherings. Other issues remain unresolved. Palestinian participation, while present, was still markedly limited, which organizers attribute largely to government-imposed restrictions on movement rather than a lack of interest. Still, the question of whether a civil society movement like this can translate hope and optimism into concrete political change remains to be seen.
That tension between aspiration and reality extends well beyond Israel. In the United States, support for Israel, particularly among younger American Jews, is waning. A 2024 Pew survey found that fewer than half of American Jews under 30 say they feel “very attached” to Israel, while a JFNA poll released in February 2026, found that just 37% of all American Jews identify as Zionists. Both numbers represent a sharp decline from older generations.
For Shira Ben Sasson, Israel director of the New Israel Fund, it is precisely the peace camp which could hold the answer to this growing disillusionment. If the state itself no longer reflects the values that once anchored many American Jews’ connection to Israel, she suggests, perhaps their more natural partner is the small but determined coalition of Israelis working to change it.
“I appreciate how difficult it is to be a Jew who cares about Israel right now,” she told the Forward as the conference, which New Israel Fund helped support and coordinate, got underway. “People are struggling with what they are seeing — the way Israel is conducting itself. Its policies. They are watching the value set that once connected them so strongly to the Jewish state disappear.”
Her response is one of both reassurance and redirection.
“Thank you for continuing to care,” she said. “But remember — the Israeli government is not your partner. We are. Pro-democracy civil society is your partner. Those of us who are fighting for equality here, for the rights of non-Israeli Jews and the rights of non-Jewish Israelis are your partners. This is where those shared values still live.”
If that message feels unfamiliar to those in the diaspora, Ben Sasson suggests the reason ultimately comes down to lack of exposure.
“We, the Israeli peace camp, need to be in many more places than we are right now,” she said. “We must get the word out that while we might not be the majority here, we are not only growing in number, we are expanding our diversity as well.”
She pointed to the rising number of Orthodox Jews, like herself, who have joined the movement as one example.
Ben Sasson also emphasized that, as with any strong partnership, the relationship must move in both directions. Israeli peace activists, she said, must make themselves more visible to American Jews. But American Jews also need to be willing to open their eyes.
“The mainstream Jewish community has to challenge itself,” she said. “They have to be able to voice their concern for Israeli democracy, for the violence in the occupied territories. And they have to be willing to engage in an honest discussion about peace.”
She is less worried about reaching individuals whose support for Israel may be wavering — many of whom, she believes, will connect with the movement’s vision — than she is about the institutions that have long shaped American Jewish engagement with Israel. Those institutions, she said, have been slow to open themselves to this kind of messaging.
“I think there’s fear,” Ben Sasson explained. “The word ‘peace’ has come to sound political. And once something is labeled political, these legacy institutions don’t want to touch it.”
But that avoidance, she warned, comes at a cost.
“They cannot afford to just stick with the same old stale perception of Israel,” she argued. “If you aren’t willing to talk about the real-life issues that Israelis are facing, you simply won’t be relevant anymore — particularly for the young people in your community.”
“Do not be afraid of controversy,” she added. “Do not be afraid to invite an Arab and a Jew to your event, where there may be disagreement. That’s okay. Struggling and wrestling is a core part of our identity.”
While Ben Sasson contends there is a critical mass of people who are hungry for an alternative way to relate to Israel, the question of feasibility remains; the same question that follows the peace movement inside Israel: Does its growing visibility reflect real political momentum, or is it simply too late to reverse course?
To those who are ready to walk away altogether, Ben Sasson points out that Israel stands to lose not only their support, but also the values and organizing traditions American Jews have long brought to the relationship.
“You’ve helped us achieve so many things in Israel for decades,” she said. “You helped us get a state. And now we need a different kind of support. The Jewish values that you offer — the concept of tikkun olam, which is not at the heart of Israeli Judaism but is at the heart of American Judaism — this is the support you can offer us right now.”
Her final plea was simple.
“Do not give up on Israel,” Ben Sasson said. “There have been so many times when things felt insurmountable and you did not give up on us. Don’t give up on us now.”
Rachel Fink is a Tel Aviv-based journalist covering Israel and the Jewish world. Her work has appeared in Haaretz, The Times of Israel, The Jerusalem Report, and Kveller.
This story was originally published on the Forward.
Features
The complete story of the delusional Winnipeg con man who duped people all over the world

By BERNIE BELLAN I have been publishing different chapters from a book I have written about a Winnipeg man who has been telling people for years that he is someone of great wealth who wants to invest in various projects in which those people are engaged.
I’ve now compiled those stories into one large pdf file, which you can read here – or download as a pdf. Simply click on the image below to open the pdf: