Features
Interview with Daniel Levin – author of international best seller “Proof of Life”, the sensational true story of the hunt for a young man gone missing in Syria in 2012
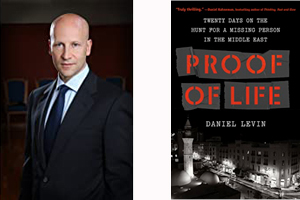
By BERNIE BELLAN A couple of months back I had the opportunity to read and review an advance copy of a terrific new book titled “Proof of Life”, by Daniel Levin.
In it Levin tells the true story of a task he was given to try and find out what happened to a young man who disappeared in Syria during the early stages of what turned out to be a protracted struggle between the regime of Bashar Assad and the many different groups that emerged determined to fight him.
By now we know how incredibly vicious that fighting became – with all sides committing atrocities that shocked much of the world. Yet, despite the tremendous dangers he knew he would face in accepting his assignment, Levin was able to navigate some of the murkiest corners of the Middle East in pursuit of his goal.
Levin’s book was so completely riveting – and disturbing in many aspects, that when I was offered the opportunity to interview Levin himself, I immediately accepted. It took some time, however, to find a time where Daniel Levin could sit down and talk with me over the phone – about his life and his endlessly fascinating career which has involved his working in some of the world’s most dangerous areas.
Finally, on June 4, Levin was available – for what I originally thought was only going to be about 20 minutes, but when he told me that he actually had 45 minutes to spare, I took advantage to delve as much as I could into how he came to be doing what he does. I spoke with Levin, who was in his home somewhere in New York.
Levin’s early years took him all over the world
I had thought that what might follow would be a give and take, but in reality Levin operates in such a different world that would be so unfamiliar to most of us that he spent a good deal of his time explaining just what it is that he does. I began by saying to him: “Your background was as sort of as a negotiator – you were working to develop modes of democracy in states that had authoritarian-led governments. Is that correct?”
Rather than answer that question in a brief manner, however, Levin entered into a long and fairly complex explanation of what he does and how he ended up in the world of hostage negotiation, which is a byproduct of his primary work.
He began by informing me that he had read my review of his book, which, he said, was quite good, except that I had made one mistake. I had written that Levin was a “Swiss-born Jew”.
“I was actually Israeli-born,” he clarified – “in 1963. My father was an early founder generation – served in the Palmach, ended up going into politics, was close to Ben Gurion, became a diplomat, and in the mid-60s he was posted to Kenya – where my sister was born.
“We were there during the Six-Day War and after he returned – in 1969, his views diverged from those of his colleagues in the Labor Party. He favoured a negotiation with the Palestinians immediately – despite the Khartoum Resolution (which became famous for the “three nos: no peace with Israel, no recognition of Israel, no negotiations with Israel”), had a big clash with most of them, and decided to leave for a few years. And because my mother was from the Italian part of Switzerland, we moved to Switzerland in 1970. That’s how the Swiss angle started.
“We lived there for most of my school years – elementary and high school. After high school I came to the US, where I went to Yeshiva, also studied martial arts. I went back to Switzerland, went to law school, moved back to Israel in 1988, both to do my military service, also because I was working on my doctorate in law and my thesis was about clashes between religious and secular legal systems.
“I came to the States in 1992 – I’m basically anchored here since.
“The reason that I’m telling you all this is that my most of my work as a lawyer involved conflicts between different legal, religious, and political systems and how they can be reconciled.
“As an example, if you have a Jewish divorce that a secular judge has to evaluate for compliance with secular constitutional norms – does he just go into his American law – or his Swiss law or his French law, or does he look at the Jewish law and see whether it might provide suitable alternate solutions that would be more compliant with his secular law principles?
“That was my initial background and when I came to the States in the early 90s I did a post doctorate at Columbia, then ended up working in a large law firm, and most of our work was in developing countries, trying to develop their new financial markets and judicial systems. I did that for a few years until I decided I wasn’t interested in doing just the transactional part and I started my own law firm with some partners with the idea of initially helping countries – in Africa, South America, in the Middle East, help them emerge from poverty and high debt levels, and try to develop new political and economic structures.
“That was in the 90s. We developed essentially a development platform – at its core a non-World Bank approach. We didn’t just fly in experts and tell them what to do, but rather we developed a kind of knowledge platform – like a library, and we would provide that platform as a tool to local talent, to young professionals on the ground, and we would work with them to develop their own solutions.
Contacted by the Prince of Liechtenstein to help start a foundation
“That was the origin of our work and, around 2006 I was contacted by a head of state – a monarch in Europe, the Prince of Liechtenstein, who said ‘I really like your approach to development. What I’d like to do is start a not-for-profit foundation and you’ll use your methodology as a way to work in failed states, conflict zones, war torn areas, to help rebuild them by helping with the next generation of leaders to develop solutions that might work – so that, for example, if you go to a country like Yemen, which has been shattered by civil war and by tribalism – 187 tribes, can we figure out different political systems, different constitutional systems – rotation governments for example – not what you have in Israel right now, but rotations among tribes, and can those solutions work?’ ”
Levin continued: “We develop platform tools for training of next-generation leaders. We work with partners in the different regions. For Yemen, for example, we’re working with a partnership in Abu Dhabi. In Libya we’re working with a very high quality individual to develop a think tank outside of Libya, where we’re training young Libyans to take future leadership positions in the country.
“It’s not as if we’re coming into countries and telling people what their countries should look like. Our goal is to use our knowledge platform and our tools to help teams on the ground to develop their country based on their own preferences and traditions, but with the benefit of best practices from other countries and regions.”
Levin went on to describe the often painfully slow steps required in trying to develop democratic institutions within countries that have not had any sort of tradition of democracy. He said that his foundation tries to find young, uncorrupted individuals – not the sons and daughters of ruling elites, he emphasized – and teach them about such things as constitutions and a judicial system that will remain uncorrupted.
I wondered whether it was even possible to find – and train, young individuals, inside the countries themselves where Levin’s foundation might be attempting to develop basic democratic norms.
He admitted that, in many cases, it involves having to take individuals outside of their countries for training. “But,” he cautioned, “there is no way to replace the presence in the country itself. There is no way, for example, to avoid having to go to Syria in those early years and interact with people there.”
Levin added though, that the goal, “at some point, is to take the core team that you’re working with out of the country – and take them for further training, in the Syrian case – to Lebanon, because it’s just not safe for your own staff and for the individuals who you’re wanting to train to leave them there.”

As much as one may harbour notions of glamorous international diplomacy – jetting into world hot spots – such as how American diplomat Richard Holbrooke was famous for doing, Levin said, he wanted to make sure to dispel any idea that what he and his small team do is anything except very hard work – often leading to total disappointment.
With that in mind, Levin launched into a more detailed explanation how he became involved in what was, at the time, a civil war in Syria between the Assad regime and a large number of factions opposed to that regime.
“That became the beginning of my work and, since the Arab Spring (which began in 2011), we’ve been so heavily involved in war zones – in Syria, for example, which is the basis of the book, that we were involved not just in developing these solutions, but in mediating between the war sides. This was early in the war – when it wasn’t clear how the war was going to end or that the regime would end up with the upper hand following the Russian intervention in 2015.
How Levin became a hostage negotiator in Syria
“It was in that context that I was approached by various families (including of the young man who went missing in Syria), who said: ‘You’re active in Syria, you’re active in Libya, can you help us find our missing son, our missing husband? That was the entry into the world of hostage negotiations.”
At that point I said to Levin that I was glad he provided context for how he ended up involved in trying to find out what happened to one young man in particular in Syria. I said to him that anyone who would read “Proof of Life” would find themselves plunged right into the harrowing tale of Levin being immersed in a very dangerous pursuit of information – without knowing all that much about Levin himself. In fact, I said to him, if he hadn’t made clear at the outset of the book that what the reader was about to read was all true, I’m sure that a great many readers would think that it’s a work of fiction.
I said to Levin that “the next question that would probably come to mind to any Jewish reader, for sure, and probably almost anyone for that matter, is how does a Jew – and you didn’t pretend to be anything other, gain entrée into all these countries where one would think a Jew – never mind an Israeli, would not exactly be received with open arms. Was it a problem at all?”
Never hid the fact he was a Jews – although he didn’t advertise his being Israeli-born
Levin responded: “There are a number of elements to that. First of all I never have hidden the fact that I’m Jewish; I did not advertise the fact that I’m Israeli. I have multiple citizenships, but I am Israeli-born. Israeli was my first one (citizenship) and the one I’m most attached to. I view myself as Israeli; I served in the army there, my father served in the army there; I was in combat multiple times. I didn’t advertise that and that is why I am very careful how I describe myself in the book.
“I do show how I recorded and documented everything in the book, but I didn’t want the book to be too much about myself. I am the protagonist in this, but I really wanted to tell the story of this war economy (in Syria) and some of its victims (some girls who were forced into prostitution in Dubai became subjects of Levin’s interest during the course of his investigation).
“As to my own background and my ‘Israeliness’, it shines through – and some of the things that I did in the army were tools that I needed to navigate these 20 days (Levin spent in pursuit of his goal) and some other scenarios.
Levin answered: “I never hide my Israeliness; I just don’t advertise it. If someone asked me I wouldn’t lie about it. Anything I’m telling you now – unless I say something is off the record, you can go ahead and write about.”
As for how Levin recorded actual conversations (which are often quoted verbatim in the book – and some of them are extremely frightening as he is able to get certain characters to open up about some terrifying incidents in which they have been involved, including murder) – “The way I recorded (conversations),” Levin explained, “was primarily with my phone. I created a short cut to my home screen. I didn’t have to open my phone; I just had to tap a button and start recording, and I had a separate recording device.
“Whenever I was able to record a conversation, I did that. There were several situations in which I was unable to do that – especially the night in Beirut where I had to surrender all my electronic devices. In those cases, I would take notes whenever I could and I’m careful in the book to indicate when I’m writing down from memory, also when the memory of others was different from the way I remembered moments, so that I try to be as honest as I can.
Levin said he “wanted to add (in response to my question how Levin was able to navigate some of the murkiest areas of the world in the Middle East) that I had lived in Africa as a kid, and one of the languages I learned was Swahili – and Swahili has a very strong Arabic base. It later helped me when I learned Arabic, much, much later in my professional career. So, part of the answer to your question is I was able to blend in, rather than stand out as Jewish or Israeli.”
I wanted to switch tacks from talking about “Proof of Life” to Levin’s experience as a negotiator in other venues. “Have you been asked by various governments to get involved in behind the scenes negotiations at other times?” I wondered.
“Yes – there are two angles to this. Usually – in the case of hostages, I get approached by families and then I coordinate with governments if it’s relevant – with the intelligence community or diplomats, but generally I get approached by families because they’re not getting anywhere with their home governments.
“With respect to mediation between the sides in the Middle East (and it’s usually the Middle East where Levin gets involved, he noted) it’s on our foundation’s platform either to mediate a conflict or to provide what I call a ‘Track 3 diplomacy’ channel, which is a very informal – with full plausible deniability, communication channel, so that the sides that might not otherwise be talking – and there are several of those in the Middle East, as you can imagine, have a way to communicate – not so much to sign some sort of peace agreement – that’s an illusion, but just, for example, to prevent unintended escalations.
“Very often Israel is one side of this equation – and an action gets misinterpreted as an intended act of aggression, and there’s a real need to have indirect conversation and make sure that it doesn’t trigger consequences. It’s something that I get very involved in as part of my daily work.”
I asked: “Given that, is there anything you’d like to say about the recent war between Israel and Hamas? If you had been involved, was there some sort of expertise that you might have been able to offer that could have prevented that war?”
“The short answer to your question,” Levin offered, “is no.
“I’ve been involved in escalations both between Israel and Palestinians and countries surrounding Israel. The issue in all the clashes between Israel and Hamas – as well as Israel in Lebanon, is: ‘Are you trying to mediate this for the sake of finding a solution or are you trying simply to mitigate the suffering or are you merely going through the motions based on your own particular identity – even if you look at the recent clash and, even if you try to avoid the particular tribal or political affiliation – Jewish, not Jewish, conservative, progressive – those types of discussions tend to be tedious and unproductive, because once people have identified who they are, their positions tend to flow from there without much flexibility or room for negotiation.
“My job is different because, in the case of Israel and Hamas, these types of escalations have clear political benefits for very specific individuals or parties. If you take the recent one, it’s very clear that Netanyahu’s political fortunes had reached an end…and obviously with this most recent case, it started with a very clear provocation by right wing Israeli groups in Sheikh Jarrah. If you want to start into a discussion about who’s been in the Middle East longer – 3,000 years, 5,000 years – I’m not interested in that.
“What I’m interested in is that people are suffering in the region and you have to make a decision whether you’re working toward a political solution or not. This particular escalation benefited Netanyahu – at least very temporarily, and it benefited Hamas. Hamas itself was starting to lose control over the street in Gaza. I’ve been to Gaza many times and Gaza today is not Gaza of 20 years ago – before Israel pulled out – in 2005. It’s also not Gaza of ten years ago.
Youth in Gaza feel oppressed by Hamas
“In Gaza today you have a youth fighting battles that were born after those conflicts of 20-25 years ago and they don’t feel the same allegiance to Hamas; they feel oppressed by Hamas. Hamas is starting to lose some of its authority and needs to resort to more and more oppression to stay in power. They had an interest in this escalation because they can present themselves as the protector of Al Aqsa Mosque in Jerusalem and responding to the provocation of Israeli policemen and soldiers with boots in the mosque. Those kinds of games and provocations have been going on for decades. There’s really nothing for me to do because no one is really trying to find a solution, through mediation or by other means – yes, there’s mediation for a cease-fire, but you’re never getting at the root of the conflict. I want to get involved when there’s a genuine desire to go beyond just repeating the same mistakes.”
I wanted to return to Levin’s experience in Syria, which, after all, led him to write “Proof of Life”. I asked him whether his involvement in mediating between various sides – both pro-regime and anti-regime, would also have led him to get involved with “Islamist groups” as well?
He answered: “No, not at the time. If you look at the timeline of the war in Syria, you have the uprising starting in 2011 – and it’s really starting over an increase in bread and food prices. And, instead of responding intelligently, they (the Assad regime) responded brutally – like many countries in the Arab Spring they started to slaughter children – 15-year-old boys spraying on a wall ‘We want cheaper food’ would be beaten to death in a police van, and that triggered huge uprisings and an insurgency started in September 2011.
“My involvement was primarily in 2012-13 in a mediating capacity. It was when the UN was trying to negotiate a cease-fire. It was before the rise of the Islamists in 2014, which also led to those gruesome executions of American and other Western hostages. It was also before the Russian intervention in September 2015, which completely tipped the war in favour of the regime.”
Levin also reminded me that there were no Islamist insurgents in 2011 in Syria, although Assad did release thousands of Islamists from prison at the very beginning of the insurgency – exactly the same way Saddam Hussein did during the American invasion of Iraq – and those released prisoners became the core of ISIS.
“At the point that we were involved, it was to see if we could deescalate the violence; the regime was not gaining the upper hand, the opposition was organized under the Free Syrian Army, and there were – within each camp, really genuine requests to see if there was a way that we could end this slaughter.
“When the whole thing collapsed – in 2014 and 15, we aborted our project there and stopped any form of mediation because the regime was no longer interested in a peaceful, negotiated solution. But I still remained involved in several matters in Syria, including the searches for missing persons and hostages.”
Levin’s current focus is on Libya and Yemen
I asked: “You say you’ve been involved in countries in Africa and the Middle East that could be described either as failed states or states attempting to emerge from authoritarian rule. Are there any other countries in which you’ve been involved?”
Levin said: “Yes, certainly in a development capacity, in Central America, Southeast Asia – Malaysia, Indonesia, but in terms of real conflict negotiation in the sense that I’ve been describing (during this conversation), it’s been primarily in north Africa, the Middle East, and the Gulf – from Yemen to Libya, even some aspects of the Iran conflict.”
“Libya and Yemen?” I said. “Those can best be described as failed states run by gangs and warlords. Is there anything you can offer as a ray of hope for the futures of those two countries?”
“Yes, I think so,” Levin replied. “Our foundation is actively involved in both those countries. In Libya, there is some hope – not so much because of the current temporary prime minister – (whose name is Dbeibeh), but rather because there is a weakening of the warlords, particularly the warlord in the east of the country, whose name is Khalifa Haftar, who is supported primarily by Egypt and the United Arab Emirates, and Russia. There is some form of reconciliation there, also encouraged and supported by European countries which finally recognized that the only way to stem the flow of African refugees coming to Europe through Libya was to have some form of stability in Libya.
“Yemen,” Levin observed, “is a very tribal society – some 187 different tribes – very fragmented, fragmented religiously between Sunni and Shia – fragmented between south and north. Yemen has been in a tenuous state since the 50s and every outside party that has tried to get involved in Yemen has failed. It’s sort of the Arab Vietnam. It’s a very complicated place to try to turn into a functioning state.
“There are very legitimate questions – and we’re working with groups, trying to figure out whether Yemen should be one nation or should it be a confederation of states or even tribes? Yemen was also a terrible mistake by the Saudi Crown Prince who thought he could prove his manhood with a quick win in Yemen and didn’t realize he would face the same fate as Nasser did 65-70 years ago (when Egypt’s then President Nasser also intervened in Yemen).
“So, Yemen is in far worse shape than Libya, I would say in answer to your question.”
As much as reading “Proof of Life” led me to want to find out quite a bit more about Daniel Levin, talking to him about the book and his career led me to ask him whether there might be more books in the works.
He said that in September a book called “Milena’s Promises” will be released in German (“Milenas Versprechen”). “It’s a crime story, a dialogue between an Israeli woman and a young man in the U.S. in the form of an email exchange. It’s all about the question of God’s existence and omnipotence, the suffering of innocent people, and the meaning of being a “chosen” people.”
“Proof of Life”, which was released on May 18th, has garnered a myriad of sensational reviews – including my own. As a result, I can hardly wait to read “Milena’s Promises” once it comes out in English.
Features
The Tech That Never Sleeps: Inside the Always-On Engines of No Limit Casinos

In communities across Canada, including Winnipeg’s dynamic Jewish community, technology has become an integral part of daily life, whether through synagogue livestreams, local cultural programming, or real-time coverage of global events affecting Israel and the diaspora. Modern digital infrastructure, while often unseen to the public, runs continuously behind the scenes, enabling information networks that never stop. The same notion of ongoing connectivity drives the 24-hour digital entertainment platforms.
One example of this infrastructure is seen in online gaming settings, where real-time data systems enable experiences that are meant to run without interruption. The global online gambling industry is expected to increase from around $97.9 billion in 2026, with internet penetration and mobile connectivity continuing to climb globally. As a result, readers interested in how these platforms work often consult a comprehensive list of No Limit casino platforms to gain a better understanding of the ecosystem.
While conversations about casinos sometimes center on the games themselves, what’s underneath the narrative is technical. Behind every digital table or interactive game is a network of servers, verification tools, live data processors, and uptime monitoring systems that must run continually. Unlike traditional venues that close at night, online platforms rely on always-on design, which means that their software infrastructure must run 24 hours a day, seven days a week, independent of player time zones.
Infrastructure That Never Closes
Although Winnipeg readers may be more familiar with the servers that power newsrooms, streaming services, and community websites, the technology center of global platforms shares similar concepts. Modern digital systems rely significantly on distributed cloud computing, which means that data is handled simultaneously over several geographical locations rather than in a single location.
This layout increases credibility while also allowing platforms to run consistently even when millions of people are actively accessing the system. Similarly, big cloud providers operate worldwide networks of data centers capable of providing near-constant uptime. According to reliability measures released by major cloud providers, such as Google Cloud infrastructure reliability overview, modern corporate systems typically aim for uptime levels greater than 99.9 percent.
That figure may sound abstract, yet it corresponds to only a few minutes of disturbance every month. In fact, ensuring such regularity needs sophisticated monitoring systems that identify faults immediately, quickly divert traffic, and maintain redundant backups across different continents. Unlike early internet platforms, which relied on a single server room, today’s large-scale systems function as interconnected worldwide networks.
Real-Time Data: The Pulse of Modern Platforms
While infrastructure keeps systems operating, real-time data engines guarantee that information is constantly sent between users and servers. These systems handle massive amounts of data per second, including player activities, system status updates, and verification checks. Although the public rarely observes these operations, they are the digital pulse of today’s internet platforms.
Real-time computing has also revolutionized industries known to Canadian readers. Financial markets, for example, use comparable high-speed data processing to quickly update stock values across trading platforms. The same logic applies to global logistical networks, airline scheduling systems, and even newsrooms that monitor breaking news as it occurs.
This is essentially one of the distinguishing features of modern digital infrastructure: information no longer moves in batches, but rather continuously over high-capacity data pipelines. Regardless of how complicated these systems are, they must stay reliable and safe, which is why developers invest much in automated monitoring and predictive maintenance.
Security and Verification in the Always-On Era
Technology that never sleeps must also be self-verifying. Modern digital platforms use multilayer security systems to identify suspicious conduct, validate user identities, and safeguard critical data. Many of these procedures remain in the background, but they are extremely important for preserving confidence in online services.
Unlike older internet platforms, which depended heavily on passwords, newer systems often include behavioral analytics, device identification, and automatic danger detection. These technologies work silently, yet they examine patterns in real time, detecting unacceptable behavior before it spreads throughout a network.
The larger IT sector has made significant investments in these measures. Organizations such as the National Institute of Standards and Technology cybersecurity framework overview give guidelines for software developers throughout the world in designing resilient digital systems. Similarly, academic research from universities continues to investigate how internet infrastructure can stay safe while yet allowing for large-scale connectivity.
Lessons for the Wider Digital World
Although talks regarding entertainment platforms often focus on user experiences, the underlying technology symbolizes a larger revolution in the digital economy. Today’s online systems must run constantly, expand fast, and stay safe even under high demand. While normal user may only observe the automatic interface on their screen, the real story is the engineering it takes to maintain that experience.
While technology develops very quickly, one thing remains constant: systems meant to function indefinitely need both intelligent engineering and meticulous management. Despite their complexity, these digital engines have become the silent basis for modern life, powering everything from local news websites to global platforms that never sleep.
Features
ClarityCheck: Securing Communication for Authors and Digital Publishers
In the world of digital publishing, communication is the lifeblood of creation. Authors connect with editors, contributors, and collaborators via email and phone calls. Publishers manage submissions, coordinate with freelance teams, and negotiate contracts online.
However, the same digital channels that enable efficient publishing also carry risk. Unknown contacts, fraudulent inquiries, and impersonation attempts can disrupt projects, delay timelines, or compromise sensitive intellectual property.
This is where ClarityCheck becomes a vital tool for authors and digital publishers. By allowing users to verify phone numbers and email addresses, ClarityCheck enhances trust, supports safer collaboration, and minimizes operational risks.
Why Verification Matters in Digital Publishing
Digital publishing involves multiple types of external communication:
- Manuscript submissions
- Editing and proofreading coordination
- Author-publisher negotiations
- Marketing and promotional campaigns
- Collaboration with illustrators and designers
In these workflows, unverified contacts can lead to:
- Scams or fraudulent project offers
- Intellectual property theft
- Miscommunication causing delays
- Financial loss due to fraudulent payments
- Unauthorized sharing of sensitive drafts
Platforms like Reddit feature discussions from authors and freelancers about using verification tools to safeguard their work. This highlights the growing awareness of digital safety in creative industries.
What Is ClarityCheck?
ClarityCheck is an online service that enables users to search for publicly available information associated with phone numbers and email addresses. Its primary goal is to provide additional context about a contact before initiating or continuing communication.
Rather than relying purely on intuition, authors and publishers can access structured information to assess credibility. This proactive approach supports safer project management and protects intellectual property.
You can explore community feedback and discussions about the service here: ClarityCheck
Key Benefits for Authors and Digital Publishers
1. Protecting Manuscript Submissions
Authors often submit manuscripts to multiple editors or publishers. Before sharing full drafts:
- Verify the contact’s legitimacy
- Ensure the communication aligns with known publishing entities
- Reduce risk of unauthorized distribution
A quick lookup can prevent time-consuming disputes and protect original content.
2. Safeguarding Collaborative Projects
Digital publishing frequently involves external contributors such as:
- Illustrators
- Designers
- Editors
- Ghostwriters
Verification ensures all collaborators are trustworthy, minimizing the chance of intellectual property theft or miscommunication.
3. Enhancing Marketing and PR Outreach
Promoting a book or digital publication often involves connecting with:
- Bloggers
- Reviewers
- Book influencers
- Digital media outlets
Before sharing press kits or marketing materials, verifying email addresses or phone contacts adds confidence and prevents potential misuse.
How ClarityCheck Works
While the internal system is proprietary, the user workflow is straightforward and efficient:
| Step | Action | Outcome |
| 1 | Enter phone number or email | Search initiated |
| 2 | Aggregation of publicly available data | Digital footprint analyzed |
| 3 | Report generated | Structured overview presented |
| 4 | Review by user | Informed decision before engagement |
The platform’s simplicity makes it suitable for authors and publishing teams, even those with limited technical expertise.
Integrating ClarityCheck Into Publishing Workflows
Manuscript Submission Process
- Receive submission request
- Verify contact via ClarityCheck
- Confirm identity of editor or publisher
- Share draft or proceed with collaboration
Collaboration with Freelancers
- Initiate project with external contributors
- Run ClarityCheck to verify email or phone number
- Establish project agreement
- Begin content creation safely
Marketing Outreach
- Contact media or reviewers
- Verify digital identity
- Share promotional materials with confidence
Ethical and Privacy Considerations
While ClarityCheck provides useful context, it operates exclusively using publicly accessible information. Authors and publishers should always:
- Respect privacy and data protection regulations
- Use results responsibly
- Combine verification with personal judgment
- Avoid sharing sensitive data with unverified contacts
Responsible use ensures the platform supports security without compromising ethical standards.
Real-World Use Cases in Digital Publishing
Scenario 1: Verifying a New Editor
An author is contacted by an editor claiming to represent a small publishing house. Running a ClarityCheck report confirms the email domain aligns with publicly available information about the company, reducing risk before signing an agreement.
Scenario 2: Screening Freelance Illustrators
A digital publisher seeks an illustrator for a children’s book. Before sharing project details or compensation terms, ClarityCheck verifies contact information, ensuring the artist is legitimate.
Scenario 3: Marketing Outreach Safety
A self-publishing author plans a social media and email campaign. Verifying influencer or reviewer contacts helps prevent marketing materials from reaching fraudulent accounts.
Why Verification Strengthens Publishing Operations
In digital publishing, speed and creativity are essential, but they must be balanced with security:
- Protect intellectual property
- Maintain trust with collaborators
- Ensure financial transactions are secure
- Prevent delays due to miscommunication
Verification tools like ClarityCheck integrate seamlessly, allowing authors and publishing teams to focus on creation rather than risk management.
Final Thoughts
In a world where publishing is increasingly digital and collaborative, verifying contacts is not just prudent — it’s necessary.
ClarityCheck empowers authors, editors, and digital publishing professionals to confidently assess phone numbers and email addresses, protect their intellectual property, and streamline communication.
Whether managing manuscript submissions, coordinating external contributors, or launching marketing campaigns, integrating ClarityCheck into your workflow ensures clarity, safety, and professionalism.
In digital publishing, trust is as important as creativity — and ClarityCheck helps safeguard both.
Features
Israel’s Arab Population Finds Itself in Dire Straits

By HENRY SREBRNIK There has been an epidemic of criminal violence and state neglect in the Arab community of Israel. At least 56 Arab citizens have died since the beginning of this year. Many blame the government for neglecting its Arab population and the police for failing to curb the violence. Arabs make up about a fifth of Israel’s population of 10 million people. But criminal killings within the community have accounted for the vast majority of Israeli homicides in recent years.
Last year, in fact, stands as the deadliest on record for Israel’s Arab community. According to a year-end report by the Center for the Advancement of Security in Arab Society (Ayalef), 252 Arab citizens were murdered in 2025, an increase of roughly 10 percent over the 230 victims recorded in 2024. The report, “Another Year of Eroding Governance and Escalating Crime and Violence in Arab Society: Trends and Data for 2025,” published in December, noted that the toll on women is particularly severe, with 23 Arab women killed, the highest number recorded to date.
Violence has expanded beyond internal criminal disputes, increasingly affecting public spaces and targeting authorities, relatives of assassination targets, and uninvolved bystanders. In mixed Arab-Jewish cities such as Acre, Jaffa, Lod, and Ramla, violence has acquired a political dimension, further eroding the fragile social fabric Israel has worked to sustain.
In the Negev, crime families operate large-scale weapons-smuggling networks, using inexpensive drones to move increasingly advanced arms, including rifles, medium machine guns, and even grenades, from across the borders in Egypt and Jordan. These weapons fuel not only local criminal feuds but also end up with terrorists in the West Bank and even Jerusalem.
Getting weapons across the border used to be dangerous and complex but is now relatively easy. Drones originally used to smuggle drugs over the borders with Egypt and Jordan have evolved into a cheap and effective tool for trafficking weapons in large quantities. The region has been turning into a major infiltration route and has intensified over the past two years, as security attention shifted toward Gaza and the West Bank.
The Negev is not merely a local challenge; it serves as a gateway for crime and terrorism across Israel, including in cities. The weapons flow into mixed Jewish-Arab cities and from there penetrate the West Bank, fueling both organized crime and terrorist activity and blurring the line between them.
The smuggling of weapons into Israel is no longer a marginal criminal phenomenon but an ongoing strategic threat that traces a clear trail: from porous borders with Egypt and Jordan, through drones and increasingly sophisticated smuggling methods, into the heart of criminal networks inside Israel, and in a growing number of cases into lethal terrorist operations. A deal that begins as a profit-driven criminal transaction often ends in a terrorist attack. Israeli police warn that a population flooded with illegal weapons will act unlawfully, the only question being against whom.
The scale of the threat is vast. According to law enforcement estimates, up to 160,000 weapons are smuggled into Israel each year, about 14,000 a month. Some sources estimate that about 100,000 illegal weapons are circulating in the Negev alone.
Israeli cities are feeling this. Acre, with a population of about 50,000, more than 15,000 of them Arab, has seen a rise in violent incidents, including gunfire directed at schools, car bombings, and nationalist attacks. In August 2025, a 16-year-old boy was shot on his way to school, triggering violent protests against the police.
Home to roughly 35,000 Arab residents and 20,000 Jewish residents, Jaffa has seen rising tensions and repeated incidents of violence between Arabs and Jews. In the most recent case, on January 1, 2026, Rabbi Netanel Abitan was attacked while walking along a street, and beaten.
In Lod, a city of roughly 75,000 residents, about half of them Arab, twelve murders were recorded in 2025, a historic high. The city has become a focal point for feuds between crime families. In June 2025, a multi-victim shooting on a central street left two young men dead and five others wounded, including a 12-year-old passerby. Yet the killing of the head of a crime family in 2024 remains unsolved to this day; witnesses present at the scene refused to testify.
The violence also spilled over to Jewish residents: Jewish bystanders were struck by gunfire, state officials were targeted, and cars were bombed near synagogues. Hundreds of Jewish families have left the city amid what the mayor has described as an “atmosphere of war.”
Phenomena that were once largely confined to the Arab sector and Arab towns are spilling into mixed cities and even into predominantly Jewish cities. When violence in mixed cities threatens to undermine overall stability, it becomes a national problem. In Lod and Jaffa, extortion of Jewish-owned businesses by Arab crime families has increased by 25 per cent, according to police data.
Ramla recorded 15 murders in 2025, underscoring the persistence of lethal violence in the city. Many victims have been caught up in cycles of revenge between clans, often beginning with disputes over “honour” and ending in gunfire. Arab residents describe the city as “cursed,” while Jewish residents speak openly about being afraid to leave their homes
Reluctance to report crimes to the authorities is a central factor exacerbating the problem. Fear of retaliation by families or criminal organizations deters victims and their relatives from coming forward, contributing to a clearance rate of less than 15 per cent of all murders. The Ayalef report notes that approximately 70 per cent of witnesses refused to cooperate with police investigations, citing doubts about the state’s ability to provide protection.
Violence in Arab society is not just an Arab sector problem; it poses a direct and serious threat to Israel’s national security. The impact is twofold: on the one hand, a rise in crime that affects the entire population; on the other, the spillover of weapons and criminal activity into terrorism, threatening both internal and regional stability. This phenomenon reached a peak in 2025, with implications that could lead to a third intifada triggered by either a nationalist or criminal incident.
The report suggests that along the Egyptian and Jordanian borders, Israel should adopt a technological and security-focused response: reinforcing border fences with sensors and cameras, conducting aerial patrols to counter drones, and expanding enforcement activity.
This should be accompanied by a reassessment of the rules of engagement along the border area, enabling effective interdiction of smuggling and legal protocols that allow for the arrest and imprisonment of offenders. The report concludes by emphasizing that rising violence in cities, compounded by weapons smuggling in the Negev, is eroding Israel’s internal stability.
Henry Srebrnik is a professor of political science at the University of Prince Edward Island.


