Features
Pogroms in Poland and Ukraine in 1920-21 presaged what was to follow 20 years later
Review by MARTIN ZEILIG Pogrom is a Russian word meaning ‘‘to wreak havoc, to demolish violently,” says the online Holocaust Encyclopedia on the United States Holocaust Museum website.
“Historically, the term refers to violent attacks by local non-Jewish populations on Jews in the Russian Empire and in other countries. The first such incident to be labeled a pogrom is believed to be anti-Jewish rioting in Odessa in 1821.
As a descriptive term, “pogrom” came into common usage with extensive anti-Jewish riots that swept the southern and western provinces of the Russian Empire in 1881–1884, following the assassination of Tsar Alexander II.
“The perpetrators of pogroms organized locally, sometimes with government and police encouragement. They raped and murdered their Jewish victims and looted their property. During the civil war that followed the 1917 Bolshevik Revolution, Ukrainian nationalists, Polish officials, and Red Army soldiers all engaged in pogrom like-violence in western Belorussia (Belarus) and Poland’s Galicia province (now West Ukraine), killing tens of thousands of Jews between 1918 and 1920.”
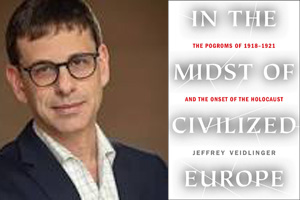
In this rigorously researched, powerful book, award winning historian Jeffrey Veidlinger presents us with, as an earlier reviewer wrote, the first full depiction of the wave of anti-Jewish pogroms that followed the Russian Revolution “and how they laid the groundwork for the Holocaust.”
Veidlinger is a graduate of McGill University and a professor of history and Judaic studies at the University of Michigan. His books, which include “The Moscow State Yiddish Theatre” and “In the Shadow of the Shtetl”, have won a National Jewish Book Award, the Barnard Hewitt Award for Outstanding Research in Theatre History, two Canadian Jewish Book Awards, and the J.I. Segal Award. He lives in Ann Arbor, Michigan.
“In the years after the Holocaust, survivors around the globe began compiling memorial books, one for each city and town,” the author writes in his introduction, “‘Will a Slaughter of Jews Be the Next European Horror?’”
But, as he notes, such memorial books are not only histories of the prewar period; they are also histories of the war itself.
“Take, for instance, the memorial book from the town of Proskuriv, located in today’s Ukraine. The book’s title, “Khurbn Proskuriv”, captures the calamity the city endured. The Yiddish world khurbn (‘destruction’), a term derived from the Hebrew word hurban, denotes the destruction of the two biblical temples in the sixth century BCE and the first century CE—and has been used to describe an array of other disasters, from earthquakes to the sinking of the Titanic. After the Second World War, it became widely understood to refer to the fate of European Jewry under the Nazis.”
What differentiates “Khurbn Proskurov” though, is that it was written in 1924—nine years before Hitler’s rise to power and 15 years before the start of the Second World War, Veidlinger writes.
“The destruction of Prokuriv took place a year after the establishment of a Ukrainian state that promised broad freedoms and national autonomy to its Jewish minority, and three months after the armistice of November 11, 1918, that ended the Great War. Delegates from thirty-two nations had just gathered in Paris to work out the treaties that would formally cap what H.G. Wells called ‘the war that will end war.’”
Meanwhile, 1300 miles to the east, on the afternoon of February 15, 1919, Ukrainian soldiers murdered over a thousand Jewish civilians “in what was at the time the single most deadliest episode of violence to befall the Jewish people in their long history of oppression.”
The massacre in Proskuriv was not an isolated event.
“Between November 1918 and March 1921, during the civil war that followed the Great War, over one thousand anti-Jewish riots and military actions—both of which were commonly referred to as progroms – were documented in about five hundred different locales throughout what is now Ukraine, and which was at the time contested territory between Russian, Polish, Ukrainian, and multinational Soviet successor states of the Russian and Austro-Hungarian empires,” Veidlinger states.
He observes that a closer analysis of the progroms of 1918-1921 shows them not only to be ethnic riots carried out by enraged townsfolk and peasants, but also military actions perpetrated by disciplined soldiers, including some units of the Red Army committing atrocities.
“Thus, what happened to Jews in Ukraine during the Second World War, then, has roots in what happened to the Jews in the same region only two decades earlier,” Veidlinger maintains.
In April 1920, Polish and Ukrainian forces advanced toward Kyiv from the north, beginning what came to be known as the Polish-Soviet War.
“Their goal was to challenge Bolshevik ascendency in the region and reclaim the historic lands of the Polish-Lithuanian Commonwealth,” the author writes.
“One study submitted to the Jewish Public Committee in January 1921 on the basis of material gathered by the Society for the Protection of the Health of the Jewish Population blamed Bulak-Balachowicz for the murder of 435 Jews in 17 locations between October and November 1920. The society also counted a total of 617 incidents of sexual assault in seven towns, including the repeated rape of a twelve-year old child by three officers. The report held locals responsible for having actively participated in the progroms, or at least having done nothing to stop them.”
Veidlinger includes photographs and eyewitness accounts of this gruesome sequence of pillage, brutality and murder in Eastern Europe during those years leading up the Second World War. Even, as he intones, in the midst of civilized Europe.
“Life went on in the 20 years between 1921 and 1941:…From the fields of Ukraine to the halls of the world’s parliaments, decent people reached out to their Jewish neighbours, heeded the warnings of Jewish activists and worked to make the world a better, more civilized place,” the author notes.
“The tragedy is that it wasn’t enough.”
At one point Veidlinger quotes US President Bill Clinton during a visit to Kigali, where he acknowledged the historic failure to prevent the 1994 Rwandan genocide: “Each bloodletting hastens the next, as the value of human life is degraded and violence becomes tolerated, the unimaginable becomes more conceivable.”
Lest we forget.
“In the Midst of Civilized Europe: The Pogroms of 1918-1921 and the Onset of the Holocaust”
By Jeffrey Veidlinger (Harper Collins
466 pg. $39.99)
Features
Tracking U.S. Immigration Statistics by Year: Shifts in Policy and Population Growth

Every number tells a story. Behind each datapoint on U.S. immigration lies a family that crossed a border, a student who arrived with a scholarship, or a worker chasing opportunity. Taken together, these stories form the demographic backbone of the country.
This article traces how immigration has shifted across time and into 2026. By focusing on statistics, we can see how policies, world events, and enforcement measures leave clear marks on US immigration. The aim is not just to report numbers, but to understand what they mean for America’s growth, its labor force, and its future.
Illegal Immigration Statistics USA 2026
Numbers on unauthorized immigration are never exact, but careful estimates reveal striking trends. This section draws from research led by Jennifer Lockman, a senior analyst affiliated with an essay writing service, EssayService, known for blending demographic data with policy context.
Lockman, who often collaborates with professional human essay writers online to translate complex data into accessible reports, describes her process as “writing an essay in numbers”: collecting surveys, interviewing migrants, and checking official counts against lived experience. Her 2026 research involved both government datasets and community-based surveys, making the results more credible.
She found that by 2023, the U.S. undocumented population had surged to 14 million, the largest in history. Roughly 27% of all immigrants in the U.S. lacked legal status at that point. But in early 2026, the trend reversed: deportations rose, border encounters fell, and the total unauthorized population declined for the first time in over a decade.
Lockman’s approach gave weight to personal accounts, such as Central American families waiting years for asylum rulings or Venezuelan migrants finding “twilight” legal status. These essay-style narratives backed the data: 6 million of the 14 million undocumented migrants in 2023 held temporary protections (asylum applicants, DACA, TPS holders), leaving them neither fully documented nor fully unauthorized.
Unauthorized Immigrant Population and Trends (2010–2026)
| Year | Estimated Unauthorized Population | Share of Total Immigrant Population | Notes |
| 2010 | 11.2 million | 24% | Plateau after 2007 surge |
| 2015 | 11.0 million | 23% | Stable, slight decline |
| 2020 | 10.3 million | 22% | Pandemic slowed inflows |
| 2022 | 12.8 million | 25% | Border arrivals surged |
| 2023 | 14.0 million | 27% | Record high |
| Jan 2026 | 13.9 million | 26% | Peak levels |
| Jun 2026 | 13.5 million | 26% | Decline after policy changes |
Key facts:
- Mexico remains the top origin, about 5.5 million people (40%).
- Central America accounts for ~20% (Guatemala, Honduras, El Salvador).
- Venezuela has grown rapidly, adding ~500,000 recent arrivals.
- Roughly 4% of the entire U.S. population is unauthorized.
Lockman concludes that immigration enforcement in 2026 created “the first visible dip in the shadow population,” but warned that long-term structural issues remain unresolved.
U.S. Immigration by Year: A Historical Perspective
The US immigration tendencies show clear peaks and valleys tied to events. In the 1990s, the U.S. legalized millions under the Immigration Reform and Control Act, pushing green card totals to a historic 1.8 million in 1991. After that, flows stabilized at about 1 million new permanent residents annually, until the COVID-19 pandemic in 2020 cut arrivals by nearly half.
By FY 2023, recovery was in full swing, with 1.17 million new green cards issued. Adding temporary migrants, asylum seekers, and undocumented arrivals, the foreign-born population climbed to 53.3 million by January 2026, or 15.8% of the U.S. population. That was the highest share since records began.
Yet, for the first time in 50 years, the number dipped in the first half of 2026, down to 51.9 million (15.4%) by June. This decline underscores how quickly policy can reshape the chart, from expansion to contraction in just months.
The US immigration chart for the last three decades makes the shift visible:

| Year | Total Foreign-Born Population | Share of U.S. Population | Notable Context |
| 1990 | 19.8 million | 7.9% | Start of modern growth |
| 2000 | 31.1 million | 11% | Post-1990s inflows |
| 2010 | 40.0 million | 13% | Strong growth |
| 2020 | 45.0 million | 13.7% | Pandemic slows flows |
| 2023 | 47.8 million | 14.5% | Border surge |
| Jan 2026 | 53.3 million | 15.8% | All-time high |
| Jun 2026 | 51.9 million | 15.4% | First decline in 50+ years |
The picture is clear: immigration has been the sole driver of U.S. population growth in recent years, even as birth rates among the native-born decline.
How Many Immigrants Came to the U.S. in 2026?
By mid-2026, immigration flows had already shifted noticeably. According to US immigration statistics released by DHS and the Census Bureau, roughly 1.2 million immigrants entered the U.S. in the first half of 2026 through legal channels: green cards, work visas, student visas, and refugee admissions combined. That’s a slight drop compared to 2023 and 2024, when yearly admissions reached over 2 million.
When unauthorized migration is factored in, early 2026 arrivals added another estimated 250,000 to 300,000 people. This marked the smallest six-month increase in over a decade, reflecting tightened enforcement and economic slowdowns abroad.
Immigrant Admissions and Arrivals (2023–2026)
| Year | Legal Permanent Residents | Temporary/Work/Study | Refugees & Asylum Grants | Estimated Unauthorized Arrivals | Total |
| 2023 | 1.17 million | 1.1 million | 200,000 | 1.7 million | ~4.2 million |
| 2024 | 1.05 million | 950,000 | 180,000 | 1.5 million | ~3.7 million |
| 2026 (Jan–Jun) | 600,000 | 500,000 | 95,000 | 250,000 | ~1.45 million |
These figures reveal a paradox: even as the U.S. foreign-born population peaked in early 2026, inflows slowed soon after, signaling a turning point.

Facts About Immigrants: Beyond the Numbers
Every chart hides a set of lived experiences. Behind US immigration statistics are students, workers, and families reshaping communities. Here are some highlights:
- Top origins: Mexico (23%), India (6%), China (5%), Philippines (5%).
- Education levels: 47% of immigrants arriving since 2010 hold a bachelor’s degree or higher.
- Labor force impact: Immigrants represent 18% of the U.S. workforce as of 2026.
- Citizenship: Nearly 45% of the foreign-born are naturalized U.S. citizens.
- Households: Roughly 14% of U.S. households are headed by an immigrant, many of them multigenerational.
- Economic output: Immigrant-led businesses generate over $1.3 trillion in sales annually, fueling both local and national economies.
These numbers remind us that immigration is not just a border issue. It shapes schools, hospitals, and industries across every state.
Policy Shifts and Their Impact
Immigration ebbs and flows with the law. Every reform, executive order, or court ruling alters the trajectory of entries and the size of the foreign-born population.
Key policy-linked shifts:
- 1990s IRCA reforms legalized millions, creating the largest one-year spike in green cards.
- Post-9/11 tightened visa screening and slowed flows in the early 2000s.
- 2017–2020 restrictions cut refugee resettlement to historic lows (below 20,000 annually).
- 2021–2023 expansions raised ceilings again and offered protections to Venezuelans and Afghans.
- 2026 enforcement showed the first measurable decline in the total immigrant population in half a century.
Taken together, these shifts reveal a pendulum effect: expansion, contraction, and expansion again. Immigration policy has never been static, and each wave leaves long shadows in classrooms, in labor markets, and in family reunifications.
Conclusion: The Changing Shape of Immigration
Looking ahead, immigration will remain central to U.S. growth. With declining birth rates among native-born Americans, new arrivals sustain both population and workforce numbers. Whether immigration grows or contracts depends less on individual desire to migrate than on how U.S. policy balances enforcement and opportunity.
Immigration data is a mirror. It reflects national priorities, international crises, and the human drive to move. The question is not whether immigration shapes the U.S., but how the U.S. chooses to shape immigration.
Features
Brave American hero only US soldier to be included among Yad Vashem’s Righteous Among the Nations

By MYRON LOVE Courage is a rare quality. More than 80 years ago, Roddie Edmonds, a master sergeant in the American army, showed what courage looked like when the then-POW successfully stared down the barrel of a Nazi gun, thereby saving the lives of about 200 of his Jewish fellow POWS.
In 2013, Edmonds became the first American soldier to be inducted into Yad Vashem’s list of Righteous Among the Nations – a designation that recognizes non-Jews who risked their lives during World war II to shelter and save Jewish lives. Earlier this year, he was also awarded the Medal of Honour, America’s highest medal for bravery.
On Wednesday, May 6, Roddie’s son, Chris, was in Winnipeg to tell his father’s story. Speaking at the Truth and Life Worship Centre in St. Vital to an audience of Jewish community members and non-Jewish supporters, the younger Edmonds, a Christian pastor from Tennessee, related how his father – at the age of 14 – in Chris’s words, committed himself to Jesus.
In the brutal winter of 1944, Master Sargent Roddie Edmonds and his 106th infantry division were thrust into action for the first time, in the Ardennes Forest. They were unprepared for what was to come.
Five days after their posting, they were hit hard by an unexpected Nazi onslaught in what became known as the Battle of the Bulge, the last great battle of the war on the Western front. Edmonds’ unit was quickly overrun and he was one of as many as 9,000 GIs who were taken prisoner.
Chris Edmonds described the POWs’ dire situation in detail. They were forced to walk for four days in freezing cold, deep snow, and constant rain. They were then put into the Nazis’ notorious sealed box cars – standing room only – and subsequently divided among several POW camps.
Master Sgt. Edmonds found himself the ranking officer responsible for almost 1,300 POWS – among them about 200 Jewish American GIs. It was Nazi practice to separate the Jewish GIs from the others and ship them to concentration camps.
On January 7, the POWs’ first day in camp, the Nazi commandant ordered Edmonds to tell only the Jewish GIs to turn up for roll call the next morning. The night before, Edmonds spoke to all of his charges and they all agreed on a plan. The next morning, all of the GIs presented themselves – including the weak and the sick – all claiming to be Jewish.
The Nazi commandant – red in the face with anger – put a gun to the 22-year-old Edmond’s head and demanded that he identify the Jewish GIs. He refused. Instead, according to his son, Chris, Roddie calmly pointed out to the commandant that the war would soon be over, the Allies were going to win, and if the commandant were to harm any of the POWs, he might be prosecuted for war crimes after the war.
As Chris noted, the colour drained from the commandant’s face, he put the gun down, and returned to his office.
Liberation for the POWS came on May 5, 1945, with the arrival of a couple of American tank columns.
Chris attributed his father’s bravery to his deep faith and love of God.
“Dad used to say that fear of people makes you scared, but fear of God makes you brave.”
Now, as was the norm, returning soldiers, POWs and Holocaust survivors rarely spoke about their war time experiences – not even to their families. All Chris knew about his father’s war was that he was a POW.
Roddie Edmonds came home, married, had a family, was an outstanding dad – according to his son – and enjoyed a successful career in sales. He died in 1985 at the age of 66.
Chris Edmonds first learned about his father’s heroism in 2008 while reading an interview in the New York Times with Lester Tanner, a prominent New York-based attorney. During the course of the interview, Tanner – whose original name was Tannenbaum – mentioned the American master sergeant who had saved his life.
Chris Edmonds reached out to Tanner, who subsequently invited the Edmonds family to come to New York where the former GI arranged for the family to be lodged at the prestigious Harbor Club and generally gave them the royal treatment. Tanner also described what had happened in that POW camp.
Chris was inspired to learn all he could about his father’s war time experiences. Fortunately, his mother had kept all of his father’s effects. Among his father’s possessions, Chris found a detailed diary of his father’s time as a POW.
As a result of Chris Edmonds’ research, he wrote a book titled “No Surrender; A father, a Son and an extraordinary Act of Heroism That Continues to Live on Today” (with co-author Douglas Century). He also produced a documentary, “Footsteps of My Father,” which includes commentary by Tanner and some of the other Jewish POWs who were spared as a result of Roddie Edmonds’ bravery.
The documentary was part of Chris’s presentation at the Truth and Life Worship Centre.
Chris Edmonds has also founded an organization: “Roddie’s Code,” which is dedicated to “extending the leadership and legacy of his father to future generations.”
Edmonds was brought to Winnipeg by community leader Larry Vickar and Christian Zionist Pastor Rudy Fidel, both of whom heard Edmonds speak in Florida earlier this year. The presentation here was sponsored by B’nai Brith Canada’s Manitoba Jewish-Christian Roundtable.
While in Winnipeg, Edmonds was also able to present his inspiring story to close to 700 students at Gray Academy, St. Paul’s High School, and Vincent Massey Collegiate.
In closing, Chris Edmonds noted that his father’s actions in that POW cap didn’t just save the 200 Jewish POWs who were there, but also their future generations – numbering around 20,000, who would not have been alive today.
“My dad used to say that there are two main purposes in life,” Chris said. “
Features
The Growing Impact of Mobile Gaming on Online Casino Play in Canada

A decade ago, desktop platforms dominated the iGaming market. People mostly used PCs, Macs, and laptops to play table classics like poker, as well as live dealer games. That changed as smartphones became more powerful and mobile internet speeds improved across Canada and across the continents – a market that Apple takes the greatest market share in.
Players are used to casino games loading quickly, streaming smoothly, and working well on smaller devices. Operators have made their websites more responsive, released apps, and designed touch-friendly games designed for mobile players. For many Canadians, smartphones are the main way they access online casinos.
Reports from NetNewsLedger and Inside2U point to mobile gaming as the main reason for growth in Canada’s online casino market. The AI Journal has reported that mobile gaming accounts for 68% of slot gaming in urban areas, and 78% in rural communities.
Mobile-first gaming
The move toward mobile gaming happened because smartphones made casino access more convenient. Players can log in away from home, at home, or while travelling without needing a desktop setup. Faster 5G coverage improved streaming quality and reduced loading times.
Modern platforms allow gamers to play casino table games on mobile with live streams, touch-optimized interfaces, and real-time gameplay available on smartphones and tablets.
Many operators redesigned their platforms around mobile use instead of adapting desktop layouts for smaller screens. Cross-platform syncing is common, allowing players to move between desktop and mobile without losing progress or account access.
Live dealer games
Early live casino platforms worked best on desktop because mobile connections struggled with video streaming. That changed as streaming technology improved and newer smartphones had more processing power.
Live dealer games support HD video and stable streams across most modern devices. Players can access blackjack, roulette, baccarat, or a poker table either from browsers or apps.
Evolution and Pragmatic Play were among the providers to optimize their live casino products for portrait and landscape mobile viewing. Features like one-tap betting, live chat, and adjustable stream quality made mobile sessions easier to manage on smartphones.
Apps and browser games
Gaming apps sometimes offer faster login options, push notifications, and biometric security features (e.g. Face ID, fingerprint authentication). Apps also help operators improve performance consistency across different devices.
Meanwhile browser-based gaming is now more reliable because of HTML5 technology and responsive web design. Reputable casinos usually provide full mobile access directly through Safari or Chrome without requiring a player to download their app.
The flexibility helped casinos reach more users across iOS and Android devices. According to coverage from TorontoMike, HTML5 development played a part in making modern casino games reaching wider audiences.
Feature-driven games
Feature-driven games became popular on mobile partly because they fit short, pick-up-and-play sessions. Quick bonus rounds, tap controls, and fast loading times work well for players using phones.
Developers, as in other gaming genres, have improved optimization to reduce battery usage and data consumption. Adaptive streaming and compressed graphics help games run smoothly even on comparatively slow connections.
Canadian casino platforms will keep refining app performance, live streaming quality, and cross-device compatibility. The focus is fast access, stable gameplay, and interfaces built specifically for smartphones and tablets. Players should remember to use licensed platforms and make use of available responsible gambling tools and account controls.



