Features
Remembrance of Things Present

By BILL MARANTZ When I woke up, on Monday, November 11, I forgot it was Remembrance Day. Or, as the “Chosen People” call it, Groundhog Day. Aka: “today.” True, as usual, I had pinned on a fake poppy (that, as usual, had fallen off) but that is the extent of my involvement in this memorial holiday. You don’t have to be reminded of something you can’t forget.
Take the Holocaust.
Please. As far as Velvel Marantz is concerned, Yom Hashoah is redundant. An annual guilt trip I’ve been on since the age of ten, shortly after Donald Trump’s previous incarnation made an ash of himself, and his “Final Solution” was revealed. To atone for the sin of being born in Canada, and being too young to be forced to risk my life on a European battlefield, I would lie awake, in bed, and torture myself with fantasies of being tossed into a roaring fire, kicking and screaming, as the iron door shut behind me. In my innocence, I didn’t realize it was not my European brothers and sisters that were fuel for Adolph Hitler’s “ovens,” but their lifeless remains.
When I learned the true details of their martyrdom, I had a slightly less harrowing nightmare to conjure up. One that involved “shower rooms” that dispensed Cyclone B, rather than H2O. This may seem like a rather morbid turn of mind but I am not an exception, but the rule. That’s what Judaism is all about. Remembrance of things present. Every morning, the first thing we do, is count our blessings. Recite fourteen prayers of thanks that can be summed up in a single prayer: “Thank you, ha’Shem for letting me wake up.” And every Saturday, and Jewish holiday, we recite a passage from the same book we’ve been reading for several thousand years. Lest we forget where we came from, and where we don’t want to go.
Again.
It’s like a joke my late friend Ron Brooker, who worked for Fox films, used to tell. The Jolson Story and Jolson Sing Again were such big hits that they were thinking of making another sequel: Jolson Sings Again and Again.
Jews dominate the movie industry but we don’t all go to the synagogue. Or “Temple,” as my New York cousins say. Not all Jews are created equal. There are secular Jews, self-hating Jews and assimilated Jews, who don’t “identify” as Jews (to use the current jargon). But there’s no escape. It’s like the Mafia. “Just when I think I’m out, they pull me back in!” Judaism is not a choice; it’s “bashert.” A blessing and a curse. Like winning a Gold Medal in the women’s 100 meter butterfly and still having to pee, standing up. To paraphrase my favorite author, Isaac Bashevis Singer: “If you ever forget you’re a Jew, don’t worry, there will always be a Gentile around to remind you.”
Which is why I don’t bother to celebrate Remembrance Day.
Features
Brave American hero only US soldier to be included among Yad Vashem’s Righteous Among the Nations

By MYRON LOVE Courage is a rare quality. More than 80 years ago, Roddie Edmonds, a master sergeant in the American army, showed what courage looked like when the then-POW successfully stared down the barrel of a Nazi gun, thereby saving the lives of about 200 of his Jewish fellow POWS.
In 2013, Edmonds became the first American soldier to be inducted into Yad Vashem’s list of Righteous Among the Nations – a designation that recognizes non-Jews who risked their lives during World war II to shelter and save Jewish lives. Earlier this year, he was also awarded the Medal of Honour, America’s highest medal for bravery.
On Wednesday, May 6, Roddie’s son, Chris, was in Winnipeg to tell his father’s story. Speaking at the Truth and Life Worship Centre in St. Vital to an audience of Jewish community members and non-Jewish supporters, the younger Edmonds, a Christian pastor from Tennessee, related how his father – at the age of 14 – in Chris’s words, committed himself to Jesus.
In the brutal winter of 1944, Master Sargent Roddie Edmonds and his 106th infantry division were thrust into action for the first time, in the Ardennes Forest. They were unprepared for what was to come.
Five days after their posting, they were hit hard by an unexpected Nazi onslaught in what became known as the Battle of the Bulge, the last great battle of the war on the Western front. Edmonds’ unit was quickly overrun and he was one of as many as 9,000 GIs who were taken prisoner.
Chris Edmonds described the POWs’ dire situation in detail. They were forced to walk for four days in freezing cold, deep snow, and constant rain. They were then put into the Nazis’ notorious sealed box cars – standing room only – and subsequently divided among several POW camps.
Master Sgt. Edmonds found himself the ranking officer responsible for almost 1,300 POWS – among them about 200 Jewish American GIs. It was Nazi practice to separate the Jewish GIs from the others and ship them to concentration camps.
On January 7, the POWs’ first day in camp, the Nazi commandant ordered Edmonds to tell only the Jewish GIs to turn up for roll call the next morning. The night before, Edmonds spoke to all of his charges and they all agreed on a plan. The next morning, all of the GIs presented themselves – including the weak and the sick – all claiming to be Jewish.
The Nazi commandant – red in the face with anger – put a gun to the 22-year-old Edmond’s head and demanded that he identify the Jewish GIs. He refused. Instead, according to his son, Chris, Roddie calmly pointed out to the commandant that the war would soon be over, the Allies were going to win, and if the commandant were to harm any of the POWs, he might be prosecuted for war crimes after the war.
As Chris noted, the colour drained from the commandant’s face, he put the gun down, and returned to his office.
Liberation for the POWS came on May 5, 1945, with the arrival of a couple of American tank columns.
Chris attributed his father’s bravery to his deep faith and love of God.
“Dad used to say that fear of people makes you scared, but fear of God makes you brave.”
Now, as was the norm, returning soldiers, POWs and Holocaust survivors rarely spoke about their war time experiences – not even to their families. All Chris knew about his father’s war was that he was a POW.
Roddie Edmonds came home, married, had a family, was an outstanding dad – according to his son – and enjoyed a successful career in sales. He died in 1985 at the age of 66.
Chris Edmonds first learned about his father’s heroism in 2008 while reading an interview in the New York Times with Lester Tanner, a prominent New York-based attorney. During the course of the interview, Tanner – whose original name was Tannenbaum – mentioned the American master sergeant who had saved his life.
Chris Edmonds reached out to Tanner, who subsequently invited the Edmonds family to come to New York where the former GI arranged for the family to be lodged at the prestigious Harbor Club and generally gave them the royal treatment. Tanner also described what had happened in that POW camp.
Chris was inspired to learn all he could about his father’s war time experiences. Fortunately, his mother had kept all of his father’s effects. Among his father’s possessions, Chris found a detailed diary of his father’s time as a POW.
As a result of Chris Edmonds’ research, he wrote a book titled “No Surrender; A father, a Son and an extraordinary Act of Heroism That Continues to Live on Today” (with co-author Douglas Century). He also produced a documentary, “Footsteps of My Father,” which includes commentary by Tanner and some of the other Jewish POWs who were spared as a result of Roddie Edmonds’ bravery.
The documentary was part of Chris’s presentation at the Truth and Life Worship Centre.
Chris Edmonds has also founded an organization: “Roddie’s Code,” which is dedicated to “extending the leadership and legacy of his father to future generations.”
Edmonds was brought to Winnipeg by community leader Larry Vickar and Christian Zionist Pastor Rudy Fidel, both of whom heard Edmonds speak in Florida earlier this year. The presentation here was sponsored by B’nai Brith Canada’s Manitoba Jewish-Christian Roundtable.
While in Winnipeg, Edmonds was also able to present his inspiring story to close to 700 students at Gray Academy, St. Paul’s High School, and Vincent Massey Collegiate.
In closing, Chris Edmonds noted that his father’s actions in that POW cap didn’t just save the 200 Jewish POWs who were there, but also their future generations – numbering around 20,000, who would not have been alive today.
“My dad used to say that there are two main purposes in life,” Chris said. “
Features
The Growing Impact of Mobile Gaming on Online Casino Play in Canada

A decade ago, desktop platforms dominated the iGaming market. People mostly used PCs, Macs, and laptops to play table classics like poker, as well as live dealer games. That changed as smartphones became more powerful and mobile internet speeds improved across Canada and across the continents – a market that Apple takes the greatest market share in.
Players are used to casino games loading quickly, streaming smoothly, and working well on smaller devices. Operators have made their websites more responsive, released apps, and designed touch-friendly games designed for mobile players. For many Canadians, smartphones are the main way they access online casinos.
Reports from NetNewsLedger and Inside2U point to mobile gaming as the main reason for growth in Canada’s online casino market. The AI Journal has reported that mobile gaming accounts for 68% of slot gaming in urban areas, and 78% in rural communities.
Mobile-first gaming
The move toward mobile gaming happened because smartphones made casino access more convenient. Players can log in away from home, at home, or while travelling without needing a desktop setup. Faster 5G coverage improved streaming quality and reduced loading times.
Modern platforms allow gamers to play casino table games on mobile with live streams, touch-optimized interfaces, and real-time gameplay available on smartphones and tablets.
Many operators redesigned their platforms around mobile use instead of adapting desktop layouts for smaller screens. Cross-platform syncing is common, allowing players to move between desktop and mobile without losing progress or account access.
Live dealer games
Early live casino platforms worked best on desktop because mobile connections struggled with video streaming. That changed as streaming technology improved and newer smartphones had more processing power.
Live dealer games support HD video and stable streams across most modern devices. Players can access blackjack, roulette, baccarat, or a poker table either from browsers or apps.
Evolution and Pragmatic Play were among the providers to optimize their live casino products for portrait and landscape mobile viewing. Features like one-tap betting, live chat, and adjustable stream quality made mobile sessions easier to manage on smartphones.
Apps and browser games
Gaming apps sometimes offer faster login options, push notifications, and biometric security features (e.g. Face ID, fingerprint authentication). Apps also help operators improve performance consistency across different devices.
Meanwhile browser-based gaming is now more reliable because of HTML5 technology and responsive web design. Reputable casinos usually provide full mobile access directly through Safari or Chrome without requiring a player to download their app.
The flexibility helped casinos reach more users across iOS and Android devices. According to coverage from TorontoMike, HTML5 development played a part in making modern casino games reaching wider audiences.
Feature-driven games
Feature-driven games became popular on mobile partly because they fit short, pick-up-and-play sessions. Quick bonus rounds, tap controls, and fast loading times work well for players using phones.
Developers, as in other gaming genres, have improved optimization to reduce battery usage and data consumption. Adaptive streaming and compressed graphics help games run smoothly even on comparatively slow connections.
Canadian casino platforms will keep refining app performance, live streaming quality, and cross-device compatibility. The focus is fast access, stable gameplay, and interfaces built specifically for smartphones and tablets. Players should remember to use licensed platforms and make use of available responsible gambling tools and account controls.
Features
Colleges With the Largest Jewish Student Communities
Choosing a college is hard enough without factoring in whether you’ll be the only Jewish person at the Shabbat table. For students who want Jewish life to be a real part of their college experience – not a weekly drive to the nearest city – campus community matters as much as academic reputation.
The good news: several major universities have Jewish student populations large enough that Jewish holidays are actually acknowledged, kosher dining isn’t a special request, and you’ll find everything from traditional minyanim to social justice groups to Jewish Greek life. What follows is a breakdown of the schools that consistently rank highest, based on Hillel International’s annual data and campus reporting.
What to Look For Beyond the Numbers
Raw population numbers don’t tell the whole story. Some students want a large Jewish population to maximize the number of organizations, fraternities and sororities, and participation at Jewish events. Others want schools with easy kosher dining options and a range of religious options for services. Still others want easy access to a large Jewish community off campus.
Top schools also come with serious academic demands. Jewish students who want to stay active in community life while keeping up with coursework often treat writing as something to outsource strategically. Students who decide to hire essay writer online guidance for specific writing tasks often find that the quality of that support keeps them on track without sacrificing everything else. Some things are worth delegating so you can actually show up for Shabbat or make it to the Hillel event on a Tuesday.
The questions worth asking before committing to any campus:
- Does the Hillel have a dedicated building, or does it operate out of shared space?
- Is kosher dining available in the main dining hall, or is it a separate facility that separates you from non-Jewish friends?
- Does the school adjust exam schedules around major Jewish holidays?
- Is there a Chabad house nearby for students who want a more observant environment?
- What’s the campus climate like regarding antisemitism, and how does the administration respond?
The Top Schools by Jewish Population
University of Florida
UF has 6,500 Jewish students – bigger than some entire colleges. The Jewish community is so established that they have multiple Jewish fraternities and sororities, plus Hillel programming that goes well beyond awkward mixers. The Hillel at UF is nationally recognized, with kosher dining and daily minyanim. Gainesville’s Jewish community includes Orthodox synagogues within reach, and UF’s administration’s efforts to combat antisemitism, as noted in 2024 Hillel reports, ensure a welcoming environment.
Rutgers University
With 6,400 Jewish students, Rutgers gives you every type of Jewish person – from very religious to “only goes to synagogue on Yom Kippur.” Being in New Jersey means NYC is accessible for internships, Shabbat with family, or just a real bagel. Rutgers Hillel is one of the most active in the country and the campus has a long history of Jewish student life.
University of Maryland
One of the most significant Hillel building projects underway anywhere in the country. The new Ben and Esther Rosenbloom Hillel Center For Jewish Life at University of Maryland will be a 40,000-square-foot building in College Park, including a kosher dining area, café, rental catering spaces, and classrooms. Maryland’s Jewish population is large, geographically convenient to Washington D.C., and has been growing.
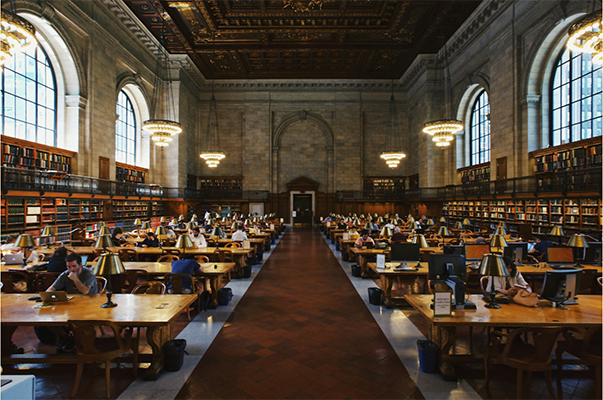
New York University
NYU sits in the middle of one of the largest Jewish communities in the world, which changes what campus Jewish life looks like entirely. The off-campus options – synagogues, kosher restaurants, Jewish cultural institutions – are unmatched anywhere else on this list. NYU Hillel is active, and students who want a more immersive Jewish urban experience rather than a contained campus bubble tend to thrive here.
Brandeis University
A different category from the others. Brandeis was founded as a Jewish-sponsored institution and still reflects that in its campus culture. Brandeis Hillel recently announced a $20 million project to renovate a former administrative building into a new 28,000-square-foot center for Jewish life on campus. Jewish studies programs are among the strongest in the country, and the campus calendar is built around Jewish holidays as a matter of course.
Cornell University
Cornell has the largest Jewish student population in the Ivy League and is finally getting the college hilel building to match. Construction began in spring 2026 on the Steven K. and Winifred A. Grinspoon Hillel Center for Jewish Community at Cornell – a 24,000-square-foot facility expected to serve over 3,000 Cornellians each year, featuring a kosher café, event hall for Shabbat dinners, a communal kosher kitchen, and a Beit Midrash. Until it opens, the community operates out of Anabel Taylor Hall, where space has been consistently stretched.
Princeton University
Smaller numbers than the large state schools, but the infrastructure is serious. Princeton’s Mandelbaum Family Dining Pavilion opened in March 2025, providing twenty kosher meals a week supervised by the Orthodox Union. Anyone on a Princeton meal plan can eat there – and students of all backgrounds eat there because the food is genuinely good.
Campus Comparison
| School | Approx. Jewish enrollment | Kosher dining | Hillel building | Chabad presence |
| University of Florida | ~6,500 | Yes | Yes | Yes |
| Rutgers University | ~6,400 | Yes | Yes | Yes |
| Cornell University | Largest in Ivy League | Yes (new facility 2027) | Under construction | Yes |
| University of Maryland | Large | New facility opening | Under construction | Yes |
| NYU | Large | Yes + off-campus | Yes | Yes |
| Brandeis | Majority Jewish | Yes | Renovation underway | Yes |
| Princeton | ~13% | Yes (OU-certified) | Yes | Yes |
What Actually Makes a Jewish Campus Community Strong
Numbers matter, but they’re not everything. When you get above around 25% Jewish, the whole campus culture shifts. Jewish holidays become things that professors acknowledge. Kosher food isn’t some weird special request. Everyone understands why you disappear for three days during Rosh Hashanah.
Beyond that threshold, what separates good Jewish campus communities from great ones is programming depth and physical space. A Hillel with a real building, a kosher kitchen, and regular Shabbat dinners creates the conditions for genuine community. A Hillel sharing a conference room and running events sporadically does not.
The schools on this list all offer something real. What varies is the scale, the feel, and whether you want a sprawling state school where Jewish life is one of many communities, or a smaller institution where it’s closer to the center of things.