Features
Letter from one Russian dissident to another dissident
The April 13, 2022 issue of The Jewish Post & News carried my article, “Conversations with a Friend in Russia,” about the war in Ukraine.
My friend and I have continued to exchange messages about the ongoing illegal war of aggression by Russia via a secure network.
Here is an edited version of a recent long letter my friend asked me to send via email to Russian dissident émigré Mark Feygin.
Feygin is a former Russian lawyer and human rights activist. He also served from January 1994 to December 1995 as a deputy of the State Duma and was the vice mayor of Samara, notes Wikipedia.
In 2011 and 2012, Feygin was active in opposition to President Vladimir Putin, and announced that he was forming an opposition party. Since the February 24, 2022 Russian invasion of Ukraine, he has gained a following on YouTube, hosting daily discussions with Ukrainian presidential advisor Oleksiy Arestovych on his channel. I have made some minor grammatical and syntactical corrections to the letter.
“Dear Mark!
“I hope my letter will not only reach you, but you will find time to read it. I considered it important to share with you the following considerations. I developed them as a result of a long – since February 24, and continuing all the time – following the course of Putin’s war against Ukraine.
‘“… this (Putin’s lies) is not obvious to the Russian layman …”’ These were your words in the New Year’s Eve stream at Zhdanov’s. That’s exactly what it is – for the main contingent, from which Putin’s occupying army is replenished, Putin’s lie is not obvious! This category of citizens has their brains blocked by many years of Putin’s propaganda. But it is necessary to make sure that Putin’s lies, his real war crimes and crimes against his own people become obvious even to the most recent idiots in this country! We need replacement drivers in their primitive and zombied brains.
“Why is it important to do this now, and not wait until Putin is somehow demolished and his accomplices, remaining in power, begin to explain to the masses that the dwarf ‘turned out to be not a father, but a bitch’ (as Andrey Piontkovsky voiced this scenario).
“This must be done now, in the midst of the war; because the doubts sown in the brains of marginals deformed by Putin’s propaganda is a real mechanism for influencing their motivation. This is a real mechanism to reduce the ranks of creatures ready to become consumables in Putin’s occupying army. The more degenerates join the ranks of the occupying army, the longer the war will last, the longer the torment of Ukrainians will continue, the more destruction there will be in Ukraine, the longer the maniac will be able to continue his terrorist activities. Therefore, it is important to reduce their ranks and change their motivation.
“The human psyche is a plastic material, an easily induced substance, but in order to reorient it, it must be acted upon. Putin’s propagandists, for their part, make an active direct impact on the brains of this redneck mass (and very effectively), but there is no counter-influence on this contingent.
“Clever verbose analytical streams of opposition bloggers and experts do not solve the problem of suppressing the drivers operating in the heads of this category of the population. They do not hear and do not listen to these clever arguments.
Here, Kiriyenko calls on the masses to make this real terrorist war the people’s war…. And, who is calling the Russian layman to the people’s war against Putin and his occupation regime?
Some of the citizens come to understand the realities themselves. But the majority in this demographic cohort won’t make it on its own. If such appeals are heard, then (it must be done) in the verbose context of analytical reasoning and assessments.
“But in this format, these appeals will not pierce the brains of idiots. They must be broken through with short and sharply directed formulations – directly calling Putin the only enemy of their homeland, of their nation.
“Cattlemass, which includes representatives of all social categories of citizens, does not care about the suffering of Ukrainians. On the contrary, they rejoice at this because they have already had hammered into their heads that their enemies have settled in Ukraine, and Putin is their protector. These deformed brains cannot be reoriented by clever reasoning and revelations.
“They need to briefly and clearly drive other formulas into their minds: that Putin is an enemy of the Russian (their) people; that Putin has plundered their country and is now finally destroying it; that Putin is an enemy of Russia, destroying the population of their country, exterminating them; that Putin is depriving their children and grandchildren of a future in this country; that each of their volleys in Ukraine is a volley that destroys their own country; that those who serve Putin are traitors to their country and there will be punishment for this; that Putin in power in Russia is Hitler’s revenge for the defeat in the Second World War, etc. – that Putin must be destroyed in order to save Russia and restore a normal life in their country for themselves.
“Your own shirt is closer to the body” and this should be emphasized in the information war. For them, these formulas should sound short, repeated and continuous. Otherwise, the majority will not reach.
“The lamentations of some well-known anti-Putin and anti-Russian bloggers-journalists that ‘Russians are genetically predetermined slaves’ are not just stupid and unfair (remember how the people rose in Khabarovsk, at least) – they are harmful, because they only help Putin’s mafia to consolidate the rednecks around Putin and use them as an instrument of his crimes.
“For the benefit of the cause of victory over Putin’s evil, it is necessary to reprogram these deformers as far as possible, in all possible ways, right now. Seeds of doubt can only germinate if they are thrown into the ground. Otherwise no.
“There is such a formula: “If a person is told every day that he is a donkey, he will soon scream like a donkey!’
“This is how the human psyche works. Putin’s propaganda actively and aggressively uses this principle, it is built on this. And it gives results, as we all see. And yet there is no effective counteraction to this in the information war! The situation in the information field is similar to the situation in the real war on the combat front, where the defenders of Ukraine are forced (so far) to respond to massive shelling by the occupiers only by shooting down missiles in their skies and destroying the occupiers within their own territory.
“In the information war, Putin’s people are persecuting lies, but by a method that affects simple brains. They aggressively stigmatize the victims of their aggression as ‘Nazis’, attribute all their own crimes to the victims, inspire their inhabitants that this is a holy war for the ‘defense of the Russian world’, etc. In the brains of Russian inhabitants (in very many) induced by Putin’s propaganda, there was a merger of retrospective images of the Second World War with their perception of the current acts of Putin’s occupiers as the war against enemies. And, in response to that from the so-called opposition on the information field, only wordy explanations of the depth of the maniac’s mental deformation, endless exposure and ridicule of his paranoid delirium, repeated discussions of his health and the vile tricks of his lackeys, etc.
“This also needs to be voiced, of course, but this is absolutely not enough to achieve a result. Where are the active direct accusations and calls for a people’s war against the occupiers? The information war on the part of the anti-Putin forces should change from debatable and explanatory to offensive and accusatory, calling for resistance.
“Moreover, now the long-winded and repeatedly repeated arguments of anti-Putin bloggers also come with oppositionists (true and pseudo) attacking each other and their mutual denials. I do not give examples, they are well known. Well, what result should be expected from such an ‘information war’? Oppositionists cease to be trusted. The opposition seems to be there, well, at least this, but the result? In the current format, these moans of the opposition can last forever.
“To achieve success on the field of “information warfare” an active, aggressive counter-action is needed. We need a consolidation of all forces, and not neurotic outbursts and mutual pecking. If there is real resistance, it will objectively work to sow doubts in the zombie brains of the bulk of the Russian layman, reprogram them – point them to their real enemy, urge them not to become accomplices in the destruction of their own country. Moreover, it will be pure truth, reinforced for them by what they experience every day in their own skin. They experience, but endure and do not think about the reasons, because they are under hypnosis. There is no anti-hypnosis. There is no massive ‘trench agitation’. (It is all the more strange that it does not exist in a country with such historical experience – let us recall what successes the Bolsheviks achieved with their “trench agitation”).
“Orcs can only be changed by driving other motivating blocks into their minds – that their real enemy is the one they currently serve. There are still surprisingly few examples of such active offensive work on the information front (as Arestovich said – “little, bad, not enough” – that’s exactly the case here!)
“A positive example of how this should be done is the New Year’s address of the Minister of Defense of Ukraine Reznikov. Everything is on point, strong and concise. It is all the more strange that “trench propaganda” is not used by anti-Putin informationists, when a maniac and the actions of his gang provide abundant objective texture for guilty verdicts and calls for a people’s war against a real enemy.
“These accusations and appeals must be made not only on some Telegram channels and (intricate, lengthy, often contradictory) on some YouTube streams, but in 24×7 mode, on all possible channels, briefly, persistently, with conviction and clearly.
“It is necessary to use all available modern technologies in order to convey the necessary messages to the addressee. It is necessary to hack federal TV channels and load them with the necessary content (experience with regional TV has already begun to appear).
“It is necessary to hack the loading of advertising plasmas on the streets of big cities and display the necessary frames and appeals on them. (It is technically possible, because there was a case when an amateur hacker put a porn video on Moscow street plasmas). Well, and so on. Do it now, and not wait until after the victory over Putin’s fascism. Information warfare is important as a direct instrument of real physical warfare, but to be effective it must be carried out with methods that penetrate to the target.
“That’s all for now. But, there’s a lot more to say.
“Respectfully,
“Good luck and victories in your fight!
Features
Gary Golden still rocking after 50 years
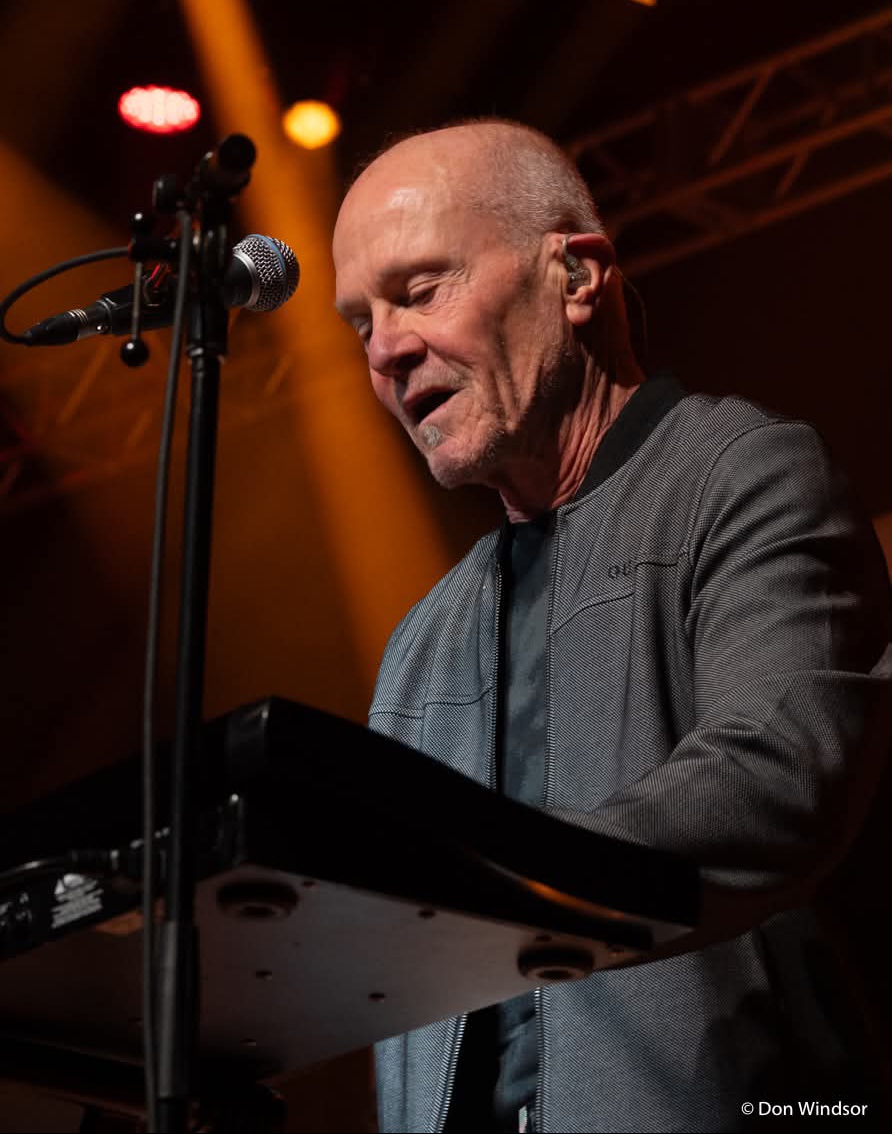
By MYRON LOVE Our Jewish community has produced several high profile musicians over the years. Among more recent stars, the members of Finjan come to mind, as does Ariel Posen – as well as Danny Greaves, Joey Serlin and Sammy Kohn of the rock band, “The Watchmen.” Arguably though, no other Jewish musician has hit the heights that Gary Golden has.
“We were all learning to play something,” Golden recalls of his teen years at Grant Park High School. “Everyone thought the guitar was really cool.”
(A an aside, I recently read an autobiography of the multi-talented Theodore Bikel who noted at one point that, by the early ‘60s, for the first time guitars outsold pianos.)
On Thursday, March 13, Golden and his band, Harlequin, celebrated their 50th anniversary as a band with a sold-out performance at Club Regent.
“It was wonderful,” says the veteran rocker. “If anyone had told us when we started that we would still be going 50 years later, we probably would have laughed .”
The Golden family (including parents Don and Helen and older sister Darlene) were among the first wave of Jewish families to relocate to south River Heights in the 1950s. Coming of age in the exuberant 1960s, Golden remembers that everyone his age was immersed in music.
Golden notes that he learned to play the guitar through trial and error.He recalls that he joined his first band when he was 18. “A couple of friends from high school were looking for a guitar player to join their band. Our band played local venues as well as touring throughout the province.”
Through contacts he made in the local music business, Golden got to know the Murphy siblings and David Budzak. Together, they formed what Golden describes as Winnipeg’s “most progressive” band at that time. Performing under the name Bentwood Rocker, the band toured from Northwestern Ontario to the West Coast.
In1975, Golden and Budzak hooked up with musicians Ralph James and the late John Hanna – both recently having moved back to
Winnipeg from Toronto – to form a band called Holy Hannah. The latter were looking for a guitar and keyboard player – that would be Golden – and a drummer (Budzak).
“After six months, we added another two musicians (one being singer George Belanger another being guitar player Glen Willows) and changed our name to Harlequin,” Golden says.
It has been quite a ride for Golden and Harlequin.
“We gelled,” he recalls. “We had the right people. And we started touring right away.”
“We were everywhere. We toured throughout the United States. We were in Venezuela. We performed in Puerto Rica in front of 35,000 people. We saw more of Canada than most politicians.
“Everywhere we went, we met a lot of wonderful people. Music is a universal language. We gave a lot of people a lot of joy.”
Along the way, the band put out six albums and was the subject of a documentary.
Golden reports that Willows and Belanger wrote most of the original material. “While I contributed some music, I was satisfied playing guitar,” he notes.
In 1987, however, Gary Golden stepped away from the band. “I was tired,” he says. “I also wanted to start a family. I had seen too many of my colleagues get married and try to have a family life. Too often, it didn’t work, The odds were against them.”
Golden was able to realize his new goal. To earn a reasonable living, he first tried real estate.
“It wasn’t for me,” he says.
He found his niche as a financial planner. He worked for Investor’s Group for ten years – then moved to the credit union world.
“In the private sector, I found that there was too much of an emphasis on sales,” he observes. “Working for the credit union, I had more scope to really advise people in terms of prudent investment. That better reflected my values.”
After 20 years or so, Golden notes, and having done reasonably well financially, Golden retired.
In 2007, George Belanger asked Golden to get back into the fray. The two are the only original members of Harlequin who are still active.
“I said yes and here we are,” the long time guitar player says.
Gary Golden is now in his early 70s and not immune to the vagaries of aging. “I try to be proactive,” he says. “I don’t sit. I work out regularly. I walk and do the treadmill. And I practice guitar for at least an hour every day.
After 50 years, Golden says that he has no plans to retire any time soon. “Being on stage is electric,” he notes. “They may have to carry me off stage.”
Features
Monitored phone calls and fear of arrest: What life looks like for Iran’s Jews now

This story was originally published in the Forward. Click here to get the Forward’s free email newsletters delivered to your inbox.
Amid the war in Iran, one Iranian Jewish woman who lives in the United States, but whose family remains in Iran, has been wracked with fear. Before the ceasefire, she spoke with her parents once a week for exactly one minute — both because of the exorbitant cost, about $50 per minute, and because of the fear of surveillance.
During one call a few days into the war, she said, something felt off.
“I could see that something is so wrong. It’s as if someone was there,” the woman, who moved to the U.S. in 2008, said in an interview with the Forward. “It seemed like my mom was actually reading from a note.”
She later learned that the Islamic Revolutionary Guard Corps had come to her parents’ home, questioning why they frequently called an American number. They instructed her parents to download Bale, an Iranian messaging app widely believed to be monitored by authorities, before making any further calls.
“It’s a spy app, and everyone knows that,” the woman said with a wry laugh. Her parents refused. Instead, they were told to call their daughter and read from a script while IRGC members watched.
“Basically, they said to prove that you are with us and not with Israel, read this when you call her,” the woman said. “After that day, they didn’t call for a long time.”
Eventually, she learned that her parents had fled to a safer part of the country to escape bombardment.
Her family are among the estimated 10,000 Jews who still live in Iran, in the largest Jewish community in the Middle East outside of Israel. Once numbering around 120,000, the community has dwindled significantly since the 1979 Islamic Revolution, when life for religious minorities fundamentally changed. Today, Jews who remain in Iran must carefully navigate life under the regime, publicly expressing loyalty to avoid being falsely accused of Zionist espionage.
Amid Iran’s war with the U.S. and Israel, that pressure has intensified.
With an ongoing internet blackout, communication is limited and closely monitored. To understand what life is like for Iranian Jews today, I spoke with several people in the U.S. who remain in sporadic contact with family members inside Iran. Everyone interviewed requested that they not be identified, fearing repercussions for either themselves or their families.
A synagogue vigil for the Supreme Leader
On April 16, Tehran’s Yusef Abad synagogue held a memorial for Ayatollah Ali Khamenei, who was killed on the first day of the war. The event was attended and reported on by several state-affiliated media channels, filming as participants from Iran’s Jewish community shared their appreciation for the deceased Supreme Leader.
Inside and around the synagogue, posters featuring photos of Khamenei were displayed alongside Farsi slogans like “Unity of Iran’s faiths against aggression — condemnation of the attack on the Tehran synagogue by the child-killing Zionist regime and criminal America” and “The Jewish faith is separate from Zionism.”
Regime media pointed to the vigil as evidence of Jewish support for Iran’s theocratic government. But experts say that interpretation misses the reality.
Beni Sabti, an Iranian-born analyst at Tel Aviv’s Institute for National Security Studies, said displays like the synagogue vigil are often a matter of survival. Jews who remain in Iran are frequently compelled to demonstrate loyalty to the regime — and opposition to Israel — in order to avoid suspicion of having ties to Israel. Allegations of such ties have often led to imprisonment and executions following the Islamic Revolution in 1979.
To protect the community, Jewish leaders — especially rabbis — often participate in pro-regime events, including memorials for senior regime figures. In some cases, Iranian rabbis have even sat alongside members of Hamas and Hezbollah to pay their respects to senior IRGC commanders responsible for funding and training terror groups across the Middle East.
The regime exerts significant pressure to stage these displays, Sabti said, “because it’s good for them to show the world, ‘You see, we don’t oppress anyone.’”
Beyond public displays, much of Iran’s economy is tied to the state — what officials often describe as a “resistance economy.” In that system, some say, expressions of loyalty can become intertwined with economic survival.
The woman who left Iran in 2008 said one of her relatives was once pressured to confiscate land from dozens of people and transfer it to the government in order to keep his job — a loyalty test she says was especially harsh because of his Jewish identity. “In the job interview, they told him, you have a Jewish background, so you have to first prove how far you will go,” she explained.
Since the 12-Day War between Israel and Iran in June 2025, the situation has grown even more tense. More than 30 Jewish Iranians were reportedly detained during that conflict because of alleged contact with Israel. While some Jewish community members were arrested during the wave of anti-regime protests that occurred at the beginning of the year, Sabti said he has not heard of a similar wave of arrests during the current war.
Still, the fear remains.
Synagogues as shelter
Some Iranian Jews have managed to stay in touch with relatives via landline phones, although calls are expensive and likely monitored. Most avoid discussing politics, using their limited time simply to confirm they are alive.
“After the 12-Day War, people really didn’t talk on the phone,” said the woman who moved to the U.S. in 2008. “We do talk, it’s not like they literally cannot, it’s just like they realized that the scrutiny was so high that no one has meaningful conversations.”
Even so, fragments of sentiment emerge.
One 25-year-old Iranian Jew from Los Angeles said his Jewish cousins in Iran cried tears of joy when they heard of the Ayatollah’s death.
He said his great uncle and cousin told him over the phone, “I don’t care, whatever the cost. If you can eliminate Khamenei, if you can eliminate Mojtaba, his son, if you can eliminate any threat… do it.” He added, “Most Persian Jews in Iran are happy, is what I hear.”
Amid the current ceasefire, a 64-year-old Iranian Jewish woman from LA said her Jewish friends in Iran have expressed relief. “They are happy that the situation is calm, but on the other hand, nobody is happy. They all want it to get finished,” she said, adding that they hope for “regime change.”
For Nora, an Iranian Jew living in New York, the war has come at a time of crisis for her family in Iran. She says her aunt has been focused on caring for her son, who is suffering from bone marrow cancer. Because the family keeps kosher, her aunt has had to leave the house — even during bombardments — to ensure he has food and other necessities.
Around three weeks into the war, her house in Tehran was destroyed after a nearby police station was struck. She briefly moved into a local synagogue; now, she lives with another Jewish family who opened their home to her. Her son remains too sick to leave the hospital.
A synagogue destroyed
Nora’s aunt is not the only Iranian Jew to find shelter in a synagogue. Sabti heard from another Jewish family inside Iran that Jewish communities have been using synagogues as bomb shelters throughout the war. He recalled doing the same during his youth at the time of the Iran-Iraq war that began in 1980.
Beyond using the space for physical safety, synagogues have also become a place for Jews to be together during the difficult time. “They come just to gather there, passing the time, meeting and having a little bit better time together,” he said.
For members of the Rafi’ Nia synagogue, a 150-year-old religious institution in Tehran, this sense of comfort has disappeared. On April 6, the community gathered there for Passover services. The next morning, they learned the building had been destroyed by an Israeli strike.
The Israel Defense Forces said that the target of the strike was not the synagogue, but rather a top commander from Khatam al-Anbiya, Iran’s military emergency command. But Iranian media suggested that the IDF had intentionally targeted the building. The head of the synagogue made a statement condemning the attacks and wishing the Iranian regime success in the war.
The woman who immigrated in 2008 had visited the Rafi’ Nia synagogue during Passover around 10 years ago. She described it as a beautiful old building. Seeing images of its destruction brought back painful memories of her family’s past.
She and her family were forcibly converted to Islam around 70 years ago, she said, with one uncle publicly hanged after he refused to convert. Her family continued practicing Judaism in secret — celebrating Shabbat behind locked doors and in her grandmother’s basement, always afraid.
She believes her family became a target for conversion after the synagogue in their area was destroyed, leaving them without formal affiliation to a recognized religious institution. On two occasions, she said, the IRGC raided their home during Jewish holidays, searching for evidence of religious practice. When they found a menorah, her father was detained. “When my dad came back, he was a ghost.” She fears that members of the destroyed synagogue could now face a similar vulnerability.
In Iran, certain religious minorities, including Jews, are constitutionally recognized. But she says that their protection is closely tied to existing institutions.
“When we talk about the lack of protection, it has a very nuanced meaning. In Iran, this doesn’t mean that the synagogues cannot exist, but it means that the existing synagogues are the only legal protection that Jews do have,” she said. “Good luck with rebuilding that place. Good luck with asking for a new synagogue.”
Sabti said the regime has already used the synagogue’s destruction as propaganda, publicly condemning the attack while reinforcing the state narrative of religious inclusion. “The head of the Islamic clerics condemned Israel and paid condolences to the Jews,” he said. “Everyone pays condolences and says, ‘Oh, sorry, we are in this together’ … but everyone knows that the other one also is lying.”
An American Jewish detainee
For one Iranian American Jew, the war has made a dire situation worse.
Kamran Hekmati, a 70-year-old Iranian American from Great Neck, New York, traveled to Iran in June 2025 and was detained during the 12-Day War. According to advocates, his alleged crime was traveling to Israel 13 years earlier for his grandson’s bar mitzvah.
Kieran Ramsey of the Global Reach advocacy group, who represents Hekmati’s family, said in an interview that Kamran being the Iranian regime’s only Jewish American prisoner puts him in a particularly precarious position. “There can be risk of retribution or reprisals against him at any moment,” Ramsey said, “from prison guards or other prisoners…his identity certainly puts him at higher risk.”
On March 16, almost three weeks into the war, Secretary of State Marco Rubio designated Hekmati as wrongfully detained, a status that allows the federal government to deploy all possible levers — diplomatic, legal, and economic — to secure his release. Ramsey says that change in designation is helpful, but only goes so far.
His organization is now pushing for the release of all American prisoners in Iran to be an integral part of the U.S.-Iran negotiations to end the war.
“Our hope is that Kamran Hekmati and the other Americans that are being held are put to the front of the list in terms of issues to decide, and not as a deal sweetener,” he said adding, “We know the U.S. negotiators have a list of American names. We know Kamran is at the top of that list…. We also know there are some very rational actors inside the regime, and we are trying to convince them that you have a no-cost way to open doors. Use Kamran as that no-cost way.”
The last time the woman who emigrated in 2008 visited Iran was two years ago. Even then, she worried that photos taken of her in the U.S. wearing a Jewish star necklace might draw the regime’s suspicion.
Now, she believes whatever space existed for quiet concessions from the Iranian government to Jews may disappear. The regime’s efforts to retain a firm grip on the Iranian people following January’s massive anti-regime protest wave and the war pose new risks.
“Just because of everything that has happened… I’m sure that any type of like ‘OK, let this go,’ ‘Let this person go,’ will end,” she said.
“Now I know that I could not go back,” she added. “I really feel if the Islamic Republic stays — and they probably have a good chance of staying — I feel like I lost Iran.”
This story was originally published on the Forward.
Features
‘Don’t give up on us now’: Israel peace summit convenes thousands to aim for elusive progress

By Rachel Fink April 30, 2026
This story was originally published in the Forward. Click here to get the Forward’s free email newsletters delivered to your inbox.
TEL AVIV, ISRAEL — On Thursday’s bright, sun-drenched morning during a rare pause in the multi-front war Israel has been locked into for nearly three years, in between the protests, funerals and steady drumbeat of violence and trauma, something decidedly more hopeful was taking place.
In one of the city’s largest conference centers, thousands gathered for the third annual People’s Peace Summit under the banner “It must be. It can be. It will be.” The event was organized by the It’s Time coalition, a partnership of more than 80 grassroots peacebuilding and shared society organizations.
Young activists in T-shirts representing their various causes stood alongside older attendees, some in kippot, others in hijabs. Diplomats in business attire moved through the crowd, as did the handful of Israeli politicians still publicly associated with the peace camp – familiar faces in a political landscape where their ranks have thinned considerably. Outside the main arena, Hebrew mingled with Arabic and English as participants strolled through art installations and an organizational fair showcasing the work of It’s Time’s partners.
While previous events took place at the height of war — while hostages remained in captivity and Gaza endured devastating destruction — this year’s summit unfolded during a fragile lull in fighting, the tenuous ceasefires with Hamas, Hezbollah, and the Islamic Revolutionary Guard Corps allowing, however briefly, for conversations to move beyond issues of immediate survival. Speakers tackled settler violence in the West Bank, looming elections, the immense challenge of rebuilding Gaza and the broader question of how to move Israel and Palestine beyond its default state of perpetual conflict. Inside the packed sessions, the tone was equal parts practical, sober and hopeful.
After a quick coffee break, the thousands of participants came together for an evening of stirring speeches and raucous musical performances. When Israeli pop icon Dana International took the stage with a familiar anthem of peace, the crowd rose to its feet, wrapping their arms around one another and belting out the words.
Despite the joyous atmosphere, the event — and the coalition behind it — is not immune from criticism. Some critiques appear to have been internalized: this year’s programming leaned more heavily into policy, strategy and the hard realities of war than previous gatherings. Other issues remain unresolved. Palestinian participation, while present, was still markedly limited, which organizers attribute largely to government-imposed restrictions on movement rather than a lack of interest. Still, the question of whether a civil society movement like this can translate hope and optimism into concrete political change remains to be seen.
That tension between aspiration and reality extends well beyond Israel. In the United States, support for Israel, particularly among younger American Jews, is waning. A 2024 Pew survey found that fewer than half of American Jews under 30 say they feel “very attached” to Israel, while a JFNA poll released in February 2026, found that just 37% of all American Jews identify as Zionists. Both numbers represent a sharp decline from older generations.
For Shira Ben Sasson, Israel director of the New Israel Fund, it is precisely the peace camp which could hold the answer to this growing disillusionment. If the state itself no longer reflects the values that once anchored many American Jews’ connection to Israel, she suggests, perhaps their more natural partner is the small but determined coalition of Israelis working to change it.
“I appreciate how difficult it is to be a Jew who cares about Israel right now,” she told the Forward as the conference, which New Israel Fund helped support and coordinate, got underway. “People are struggling with what they are seeing — the way Israel is conducting itself. Its policies. They are watching the value set that once connected them so strongly to the Jewish state disappear.”
Her response is one of both reassurance and redirection.
“Thank you for continuing to care,” she said. “But remember — the Israeli government is not your partner. We are. Pro-democracy civil society is your partner. Those of us who are fighting for equality here, for the rights of non-Israeli Jews and the rights of non-Jewish Israelis are your partners. This is where those shared values still live.”
If that message feels unfamiliar to those in the diaspora, Ben Sasson suggests the reason ultimately comes down to lack of exposure.
“We, the Israeli peace camp, need to be in many more places than we are right now,” she said. “We must get the word out that while we might not be the majority here, we are not only growing in number, we are expanding our diversity as well.”
She pointed to the rising number of Orthodox Jews, like herself, who have joined the movement as one example.
Ben Sasson also emphasized that, as with any strong partnership, the relationship must move in both directions. Israeli peace activists, she said, must make themselves more visible to American Jews. But American Jews also need to be willing to open their eyes.
“The mainstream Jewish community has to challenge itself,” she said. “They have to be able to voice their concern for Israeli democracy, for the violence in the occupied territories. And they have to be willing to engage in an honest discussion about peace.”
She is less worried about reaching individuals whose support for Israel may be wavering — many of whom, she believes, will connect with the movement’s vision — than she is about the institutions that have long shaped American Jewish engagement with Israel. Those institutions, she said, have been slow to open themselves to this kind of messaging.
“I think there’s fear,” Ben Sasson explained. “The word ‘peace’ has come to sound political. And once something is labeled political, these legacy institutions don’t want to touch it.”
But that avoidance, she warned, comes at a cost.
“They cannot afford to just stick with the same old stale perception of Israel,” she argued. “If you aren’t willing to talk about the real-life issues that Israelis are facing, you simply won’t be relevant anymore — particularly for the young people in your community.”
“Do not be afraid of controversy,” she added. “Do not be afraid to invite an Arab and a Jew to your event, where there may be disagreement. That’s okay. Struggling and wrestling is a core part of our identity.”
While Ben Sasson contends there is a critical mass of people who are hungry for an alternative way to relate to Israel, the question of feasibility remains; the same question that follows the peace movement inside Israel: Does its growing visibility reflect real political momentum, or is it simply too late to reverse course?
To those who are ready to walk away altogether, Ben Sasson points out that Israel stands to lose not only their support, but also the values and organizing traditions American Jews have long brought to the relationship.
“You’ve helped us achieve so many things in Israel for decades,” she said. “You helped us get a state. And now we need a different kind of support. The Jewish values that you offer — the concept of tikkun olam, which is not at the heart of Israeli Judaism but is at the heart of American Judaism — this is the support you can offer us right now.”
Her final plea was simple.
“Do not give up on Israel,” Ben Sasson said. “There have been so many times when things felt insurmountable and you did not give up on us. Don’t give up on us now.”
Rachel Fink is a Tel Aviv-based journalist covering Israel and the Jewish world. Her work has appeared in Haaretz, The Times of Israel, The Jerusalem Report, and Kveller.
This story was originally published on the Forward.



