Features
The Little Synagogue in Me: How one of the last surviving prairie synagogues found a home at Calgary’s Heritage Park

By IRENA KARSHENBAUM Looking back, I can’t believe it’s been 12 years since The Little Synagogue came to Calgary’s Heritage Park Historical Village, the largest living history museum in Canada. It feels like another life.
I remember lying in bed at night, dreaming about this project, how I was going to put a synagogue in Heritage Park. Everything seemed so far into the future.
Then all the things I was wanting to do, planning to do, needing to do, happened. All the nights, all the emails, all the meetings, all the phone calls, all the begging for money, all the running around are now a blur.
There is a false front, yellow, wooden synagogue with a white veranda at Heritage Park today, one of the last rural synagogues to survive on the prairies and have the distinction — and good fortune! — of being included in the permanent collection of any historic park in Canada. The first, and only one. To date.
The Montefiore Institute, as it was originally known, tells the story of early Canadian prairie settlement and that history includes Jews who fled the raging anti-Semitism of Russia and Romania, to the edge of the earth, to Alberta. They built their colony in 1910 in the Palliser Triangle, blanketing much of southeastern Alberta and southwestern Saskatchewan, where nothing was supposed to grow, and in the bitter cold and in the dry, scorching heat, they broke the land. The Jewish people were living on the Canadian prairies from the very beginning, beside the Danes, Italians, Ukrainians, Volga Germans and many others, the Montefiore Institute tells this story today.
The Montefiore Institute was built in 1916, abandoned by the mid 1920s, and moved to Hanna, about 130 kilometres west, around 1940. In time, it was plastered in green and white siding, the porch was covered to create a much-needed extra bedroom for the family’s numerous children, an addition was built in the back, and the cutout where the Magen David once looked out into the distant horizon disappeared under siding. Its transformation to an unassuming bungalow was complete. Its Jewish history was lost from memory. The family thought they were living in the most luxurious home they had ever lived in, a conversion from an old church.
Two generations later a motley crew of volunteers found the Montefiore Institute and, after discovering that thanks to the dryness of the climate, it was like new, and would be able to withstand a 230 kilometre trek on a truck from Hanna to Calgary.
Two years had passed since I emailed my proposal to Heritage Park, when we drove to Hanna early one June morning, in 2008, and watched a crew of young men remove the building from its foundation. They inserted giant, square wooden beams under the house and “rolled” them. The building ripped off the foundation and slowly slid on to the truck bed. Oh how those workmen’s bodies moved! None of them were big or stocky or bulky – what you’d think they’d have to be for such physically demanding labour. They moved like ballerinas. They were lean, the kind of lean that I have encountered in men who have lived difficult lives. How hard they worked! And when they were done, we gave them pies, bought at a Hanna bakery, as an expression of our gratitude. It felt shameful. They got paid, sure. But it still felt wrong. Like it wasn’t enough.
Hanna was left behind and for five long months there was that farm at Strathmore, 50 kilometres east of Calgary, where the synagogue underwent exterior restoration. The ugly siding was removed, and lovely, raw wood was revealed underneath, covered in nails as numerous as a child’s freckled face. The nails were yanked, the holes were filled and smoothed and the exterior was painted by the restoration crew that drove out to Strathmore and back to Calgary and back out there and back to Calgary, day after day.
Every time I would speak in public about the project, my voice would crack and a tear would betray me. What’s wrong with me? I’d ask. I’m not religious. This isn’t even my history, if you think it in simple terms. My family left Kharkov, the Soviet Union in 1978, travelled through Vienna and stayed in Rome before arriving in Calgary in 1979. Those homesteaders came from Russia and Romania in 1910. If you think of it as our collective Jewish history, then sure, this is my history. Maybe my soul knows something my head does not.
People thank me for loving history. It sounds simple. I’m not simple. This is more than loving history. I love ideas. Projects. A good story. Adventure. I love to create things. Work with people, that’s when you really get to know them. This is about that. It’s about creating beauty in the world, in one small place.
The Little Synagogue races along the highway one late November day in 2008. It has an escort of electrical crews. It slows down, the electrical crews raise the overhead wires and the building slowly passes underneath. Imagine a little yellow synagogue racing down the highway. Very cute. It comes to a stop on the corner of a farm on the outskirts of Calgary because it can’t travel through the city in the middle of the day. It will cause traffic jams. We go home and wait ‘till night. I’m scared that some kook might burn down our precious jewel. The time can’t pass quickly enough, but then it does and we move our kinder, don’t shlof we tell it, in the middle of the night. Television crews chase it. It’s quite the sight. It would make for a great musical. The name is easy, “Little Synagogue, The Musical!” With an exclamation point. Too bad I can’t write lyrics or music or act or carry a tune or tap dance. It might also make a nice Disney cartoon. Barbra Streisand can sing my parts.
The Little Synagogue arrives at Heritage Park at 4:00 o’clock in the morning. The Meshugenah Synagogue Chasers go to Denny’s for breakfast as there are no Heritage Park staff up that early to accept our gift. We warm up, fill our bellies with eggs and toast and return to the park where we are greeted by “Important People”. They graciously accept our gift. The Little Synagogue is driven into the park grounds and placed on its foundation.
Another long winter, the begging for money is endless, the interior is restored, the benches are made, the bimah is built, the mezuzahs are carved to look like they are worm-eaten. Very apropos for a rural synagogue. As all of this is happening, the grand opening celebration is being organized. There is no time to go grocery shopping, there is no time to trap the dust bunnies hopping all over my floors. There is hardly time to work to earn a living to pay my bills. There is no time for anything other than the grand opening, the synagogue, work, the grand opening, the synagogue, and what should I wear? And what shall I say in my speech at the opening?
We’ll get a thousand people at the opening, I tell my board and opening committee. They tell me I’m crazy. 600, 800 max. No, we’ll get 1,000, I argue with them.
The speech gets written and rewritten, over three months. The dress is bought. I’m lent a choker festoon necklace, a vintage looking handbag. I cave and buy a $400 hat. There are people all around working hard, doing this and that, and on the Thursday before the grand opening everything stops. I can hear the silence. I have nothing to do that weekend except show up at the grand opening celebration on Sunday, June 28, 2009. We eat burgers at a park the night before. The air has the sweet smell of flowers, the sun blushes its pretty face on us like from a scene out of Akira Kurosawa’s “Dreams.”
The day of the grand opening arrives. My mother dresses me as if I am a princess, lunch at Heritage Park, and the crowds start coming, and coming, 2,000 people appear, and more. Our most generous donors take turns carrying the Torah, regally crowned by a chuppah and the joyful people follow behind. They sing and clap and have tears in their eyes. Very Important People give speeches. My voice cracks, again, when I give my speech. My soul knows something my head does not.
The greatest joy in life, I think, comes from dreaming. Then doing.
Founding president of The Little Synagogue on the Prairie Project Society, Irena Karshenbaum will give a talk about this special project for the Jewish Heritage Centre of Western Canada on Sunday, May 30, 2021 at 2:00 pm CDT. Click here to register: https://www.jhcwc.org/programs/
Irena Karshenbaum writes in Calgary. She can be reached at irenakarshenbaum.com.
Features
The United Arab Emirates are Moving Away from Saudi Arabia

By HENRY SREBRNIK The United Arab Emirates, the world’s third-largest oil producer, quit the Organization of Petroleum Exporting Countries (OPEC) at the end of April. And that’s a very big deal.
Apart from its effect on the cartel’s ability to control oil prices, the move reflects a widening confrontation with Saudi Arabia and a fundamental realignment of alliances as a result of the current Middle East war over Iran, as well as the ongoing civil war in Yemen.
The Saudi-Emirati fracture is not new, but it crossed a qualitative threshold in late 2025. On December 29, Saudi Arabian air strikes targeted an Emirati weapons convoy at the port of Mukalla in Yemen, an act without precedent between two nominal allies. Riyadh then publicly demanded the withdrawal of all UAE forces from Yemeni territory and in early 2026, that call was answered with the dissolution of the Southern Transitional Council (STC), Abu Dhabi’s principal proxy in the country.
The Saudi foreign ministry accused the UAE of pressuring the STC to conduct military operations along the kingdom’s southern borders, describing the move as a direct threat to Saudi national security and a “red line” for Riyadh that it would not hesitate to confront.
These developments also point to a significant Emirati miscalculation. By backing the STC’s advance into eastern Yemen along the coast, Abu Dhabi has sought to build leverage over Saudi Arabia and Oman while consolidating its influence across the Arabian Sea and the Horn of Africa.
The Emiratis, however, underestimated both Riyadh’s willingness to assert itself directly in its immediate neighborhood and its enduring leverage over Yemen’s political and military actors. The episode emphasizes a central reality of the conflict: While the UAE has built deep influence through local partners, Saudi Arabia remains the decisive external actor in Yemen.
Saudi Arabia seeks to preserve the territorial integrity of Arab states and to position itself as a regional stabilising power. The UAE, on the other hand, has built, since 2015, a doctrine founded on force projection through non-state actors in Libya, Sudan, Somalia and Yemen.
The UAE has backed the rebel Rapid Support Forces (RSF) against the Sudanese Armed Forces (SAF) in the Sudanese civil war that began in April 2023, while Riyadh supports the latter. In Somalia, breaking ranks with other Arab nations, the UAE became the first Arab and Muslim country to recognise the breakaway region of Somaliland.
“The Saudis want obedience, or at least alignment with their regional policies,” according to Jonny Gannon, a former senior CIA officer with decades of experience in the Middle East. “The Emiratis don’t want to be obedient. They want optionality.”
Most important, in 2020, the UAE became the first Gulf country and only the third Arab country to establish diplomatic relations with Israel under the Abraham Accords facilitated by the first Trump administration. That paved the way for other Arab countries, such as Bahrain and Morocco, to normalize ties with Israel.
The Saudis have attacked the UAE as “Israel’s Trojan Horse” and denounced the Abraham Accords, as “a political military alliance dressed in the garb of religion.” Emirati officials believe the Saudis are waging a deliberate incitement campaign centered on the UAE’s relationship with Israel. After Saudi Arabia bombed the UAE’s partner forces in Yemen last December, Saudi posts criticizing Israel spiked dramatically, with 77 per cent of the comments attacking the UAE as “Israel’s proxy executing Zionist plans to divide Arab states.”
The accords helped deepen economic, cultural, trade, investment, and intelligence cooperation between the UAE and Israel, which extended to defence as well. This is perhaps why Iran made the UAE its biggest target in the current war. Iran has launched roughly 550 ballistic and cruise missiles and over 2,200 drones specifically at the Emirates. For years, the UAE had pursued a strategy of “omni-alignment,” attempting to maintain deep security ties with Washington and economic ties with Beijing, while fostering a détente with Tehran to protect its status as a safe haven for global capital.
The Iranian bombardment violently disproved this thesis. It proved that economic integration and diplomatic hedging do not grant immunity when regional hostilities boil over. In a historic move, Israel deployed an active Iron Dome battery, accompanied by dozens of Israel Defence Forces operators, directly to the UAE to help defend Emirati airspace against Iran. This marked the very first time Israel deployed its premier air-defence system and its own troops to protect a foreign Arab nation. The UAE realized that when its survival was on the line, the Arab League issued statements, but Israel sent interceptors.
This traumatic realization served as the catalyst for Abu Dhabi to aggressively assert its own sovereignty, deciding that if it must endure the costs of a regional war, it will no longer subvert its economic or political interests to regional consortiums that offer no tangible protection.
So Abu Dhabi has made a choice that goes well beyond energy policy. It is purchasing American strategic goodwill, at the precise moment when its regional alliance framework is collapsing and when it needs a substitute security guarantee. With Iran having conducted direct attacks on Emirati territory and shipping, and with Saudi Arabia having shifted into open confrontation mode, Abu Dhabi’s strategic calculus has fundamentally changed. Washington is no longer a preferred partner. It has become a necessity.
Henry Srebrnik is a professor of political science at the University of Prince Edward Island.
Features
Gary Golden still rocking after 50 years
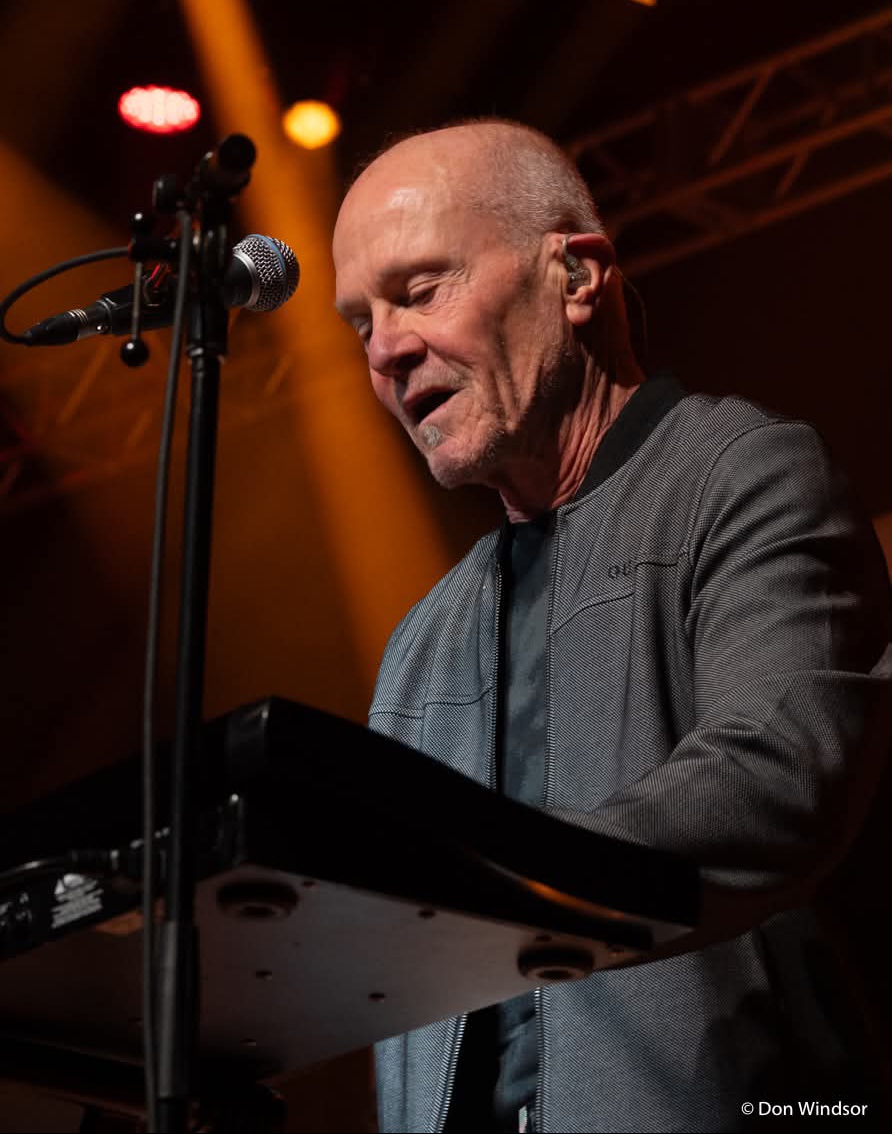
By MYRON LOVE Our Jewish community has produced several high profile musicians over the years. Among more recent stars, the members of Finjan come to mind, as does Ariel Posen – as well as Danny Greaves, Joey Serlin and Sammy Kohn of the rock band, “The Watchmen.” Arguably though, no other Jewish musician has hit the heights that Gary Golden has.
“We were all learning to play something,” Golden recalls of his teen years at Grant Park High School. “Everyone thought the guitar was really cool.”
(A an aside, I recently read an autobiography of the multi-talented Theodore Bikel who noted at one point that, by the early ‘60s, for the first time guitars outsold pianos.)
On Thursday, March 13, Golden and his band, Harlequin, celebrated their 50th anniversary as a band with a sold-out performance at Club Regent.
“It was wonderful,” says the veteran rocker. “If anyone had told us when we started that we would still be going 50 years later, we probably would have laughed .”
The Golden family (including parents Don and Helen and older sister Darlene) were among the first wave of Jewish families to relocate to south River Heights in the 1950s. Coming of age in the exuberant 1960s, Golden remembers that everyone his age was immersed in music.
Golden notes that he learned to play the guitar through trial and error.He recalls that he joined his first band when he was 18. “A couple of friends from high school were looking for a guitar player to join their band. Our band played local venues as well as touring throughout the province.”
Through contacts he made in the local music business, Golden got to know the Murphy siblings and David Budzak. Together, they formed what Golden describes as Winnipeg’s “most progressive” band at that time. Performing under the name Bentwood Rocker, the band toured from Northwestern Ontario to the West Coast.
In1975, Golden and Budzak hooked up with musicians Ralph James and the late John Hanna – both recently having moved back to
Winnipeg from Toronto – to form a band called Holy Hannah. The latter were looking for a guitar and keyboard player – that would be Golden – and a drummer (Budzak).
“After six months, we added another two musicians (one being singer George Belanger another being guitar player Glen Willows) and changed our name to Harlequin,” Golden says.
It has been quite a ride for Golden and Harlequin.
“We gelled,” he recalls. “We had the right people. And we started touring right away.”
“We were everywhere. We toured throughout the United States. We were in Venezuela. We performed in Puerto Rica in front of 35,000 people. We saw more of Canada than most politicians.
“Everywhere we went, we met a lot of wonderful people. Music is a universal language. We gave a lot of people a lot of joy.”
Along the way, the band put out six albums and was the subject of a documentary.
Golden reports that Willows and Belanger wrote most of the original material. “While I contributed some music, I was satisfied playing guitar,” he notes.
In 1987, however, Gary Golden stepped away from the band. “I was tired,” he says. “I also wanted to start a family. I had seen too many of my colleagues get married and try to have a family life. Too often, it didn’t work, The odds were against them.”
Golden was able to realize his new goal. To earn a reasonable living, he first tried real estate.
“It wasn’t for me,” he says.
He found his niche as a financial planner. He worked for Investor’s Group for ten years – then moved to the credit union world.
“In the private sector, I found that there was too much of an emphasis on sales,” he observes. “Working for the credit union, I had more scope to really advise people in terms of prudent investment. That better reflected my values.”
After 20 years or so, Golden notes, and having done reasonably well financially, Golden retired.
In 2007, George Belanger asked Golden to get back into the fray. The two are the only original members of Harlequin who are still active.
“I said yes and here we are,” the long time guitar player says.
Gary Golden is now in his early 70s and not immune to the vagaries of aging. “I try to be proactive,” he says. “I don’t sit. I work out regularly. I walk and do the treadmill. And I practice guitar for at least an hour every day.
After 50 years, Golden says that he has no plans to retire any time soon. “Being on stage is electric,” he notes. “They may have to carry me off stage.”
Features
Monitored phone calls and fear of arrest: What life looks like for Iran’s Jews now

This story was originally published in the Forward. Click here to get the Forward’s free email newsletters delivered to your inbox.
Amid the war in Iran, one Iranian Jewish woman who lives in the United States, but whose family remains in Iran, has been wracked with fear. Before the ceasefire, she spoke with her parents once a week for exactly one minute — both because of the exorbitant cost, about $50 per minute, and because of the fear of surveillance.
During one call a few days into the war, she said, something felt off.
“I could see that something is so wrong. It’s as if someone was there,” the woman, who moved to the U.S. in 2008, said in an interview with the Forward. “It seemed like my mom was actually reading from a note.”
She later learned that the Islamic Revolutionary Guard Corps had come to her parents’ home, questioning why they frequently called an American number. They instructed her parents to download Bale, an Iranian messaging app widely believed to be monitored by authorities, before making any further calls.
“It’s a spy app, and everyone knows that,” the woman said with a wry laugh. Her parents refused. Instead, they were told to call their daughter and read from a script while IRGC members watched.
“Basically, they said to prove that you are with us and not with Israel, read this when you call her,” the woman said. “After that day, they didn’t call for a long time.”
Eventually, she learned that her parents had fled to a safer part of the country to escape bombardment.
Her family are among the estimated 10,000 Jews who still live in Iran, in the largest Jewish community in the Middle East outside of Israel. Once numbering around 120,000, the community has dwindled significantly since the 1979 Islamic Revolution, when life for religious minorities fundamentally changed. Today, Jews who remain in Iran must carefully navigate life under the regime, publicly expressing loyalty to avoid being falsely accused of Zionist espionage.
Amid Iran’s war with the U.S. and Israel, that pressure has intensified.
With an ongoing internet blackout, communication is limited and closely monitored. To understand what life is like for Iranian Jews today, I spoke with several people in the U.S. who remain in sporadic contact with family members inside Iran. Everyone interviewed requested that they not be identified, fearing repercussions for either themselves or their families.
A synagogue vigil for the Supreme Leader
On April 16, Tehran’s Yusef Abad synagogue held a memorial for Ayatollah Ali Khamenei, who was killed on the first day of the war. The event was attended and reported on by several state-affiliated media channels, filming as participants from Iran’s Jewish community shared their appreciation for the deceased Supreme Leader.
Inside and around the synagogue, posters featuring photos of Khamenei were displayed alongside Farsi slogans like “Unity of Iran’s faiths against aggression — condemnation of the attack on the Tehran synagogue by the child-killing Zionist regime and criminal America” and “The Jewish faith is separate from Zionism.”
Regime media pointed to the vigil as evidence of Jewish support for Iran’s theocratic government. But experts say that interpretation misses the reality.
Beni Sabti, an Iranian-born analyst at Tel Aviv’s Institute for National Security Studies, said displays like the synagogue vigil are often a matter of survival. Jews who remain in Iran are frequently compelled to demonstrate loyalty to the regime — and opposition to Israel — in order to avoid suspicion of having ties to Israel. Allegations of such ties have often led to imprisonment and executions following the Islamic Revolution in 1979.
To protect the community, Jewish leaders — especially rabbis — often participate in pro-regime events, including memorials for senior regime figures. In some cases, Iranian rabbis have even sat alongside members of Hamas and Hezbollah to pay their respects to senior IRGC commanders responsible for funding and training terror groups across the Middle East.
The regime exerts significant pressure to stage these displays, Sabti said, “because it’s good for them to show the world, ‘You see, we don’t oppress anyone.’”
Beyond public displays, much of Iran’s economy is tied to the state — what officials often describe as a “resistance economy.” In that system, some say, expressions of loyalty can become intertwined with economic survival.
The woman who left Iran in 2008 said one of her relatives was once pressured to confiscate land from dozens of people and transfer it to the government in order to keep his job — a loyalty test she says was especially harsh because of his Jewish identity. “In the job interview, they told him, you have a Jewish background, so you have to first prove how far you will go,” she explained.
Since the 12-Day War between Israel and Iran in June 2025, the situation has grown even more tense. More than 30 Jewish Iranians were reportedly detained during that conflict because of alleged contact with Israel. While some Jewish community members were arrested during the wave of anti-regime protests that occurred at the beginning of the year, Sabti said he has not heard of a similar wave of arrests during the current war.
Still, the fear remains.
Synagogues as shelter
Some Iranian Jews have managed to stay in touch with relatives via landline phones, although calls are expensive and likely monitored. Most avoid discussing politics, using their limited time simply to confirm they are alive.
“After the 12-Day War, people really didn’t talk on the phone,” said the woman who moved to the U.S. in 2008. “We do talk, it’s not like they literally cannot, it’s just like they realized that the scrutiny was so high that no one has meaningful conversations.”
Even so, fragments of sentiment emerge.
One 25-year-old Iranian Jew from Los Angeles said his Jewish cousins in Iran cried tears of joy when they heard of the Ayatollah’s death.
He said his great uncle and cousin told him over the phone, “I don’t care, whatever the cost. If you can eliminate Khamenei, if you can eliminate Mojtaba, his son, if you can eliminate any threat… do it.” He added, “Most Persian Jews in Iran are happy, is what I hear.”
Amid the current ceasefire, a 64-year-old Iranian Jewish woman from LA said her Jewish friends in Iran have expressed relief. “They are happy that the situation is calm, but on the other hand, nobody is happy. They all want it to get finished,” she said, adding that they hope for “regime change.”
For Nora, an Iranian Jew living in New York, the war has come at a time of crisis for her family in Iran. She says her aunt has been focused on caring for her son, who is suffering from bone marrow cancer. Because the family keeps kosher, her aunt has had to leave the house — even during bombardments — to ensure he has food and other necessities.
Around three weeks into the war, her house in Tehran was destroyed after a nearby police station was struck. She briefly moved into a local synagogue; now, she lives with another Jewish family who opened their home to her. Her son remains too sick to leave the hospital.
A synagogue destroyed
Nora’s aunt is not the only Iranian Jew to find shelter in a synagogue. Sabti heard from another Jewish family inside Iran that Jewish communities have been using synagogues as bomb shelters throughout the war. He recalled doing the same during his youth at the time of the Iran-Iraq war that began in 1980.
Beyond using the space for physical safety, synagogues have also become a place for Jews to be together during the difficult time. “They come just to gather there, passing the time, meeting and having a little bit better time together,” he said.
For members of the Rafi’ Nia synagogue, a 150-year-old religious institution in Tehran, this sense of comfort has disappeared. On April 6, the community gathered there for Passover services. The next morning, they learned the building had been destroyed by an Israeli strike.
The Israel Defense Forces said that the target of the strike was not the synagogue, but rather a top commander from Khatam al-Anbiya, Iran’s military emergency command. But Iranian media suggested that the IDF had intentionally targeted the building. The head of the synagogue made a statement condemning the attacks and wishing the Iranian regime success in the war.
The woman who immigrated in 2008 had visited the Rafi’ Nia synagogue during Passover around 10 years ago. She described it as a beautiful old building. Seeing images of its destruction brought back painful memories of her family’s past.
She and her family were forcibly converted to Islam around 70 years ago, she said, with one uncle publicly hanged after he refused to convert. Her family continued practicing Judaism in secret — celebrating Shabbat behind locked doors and in her grandmother’s basement, always afraid.
She believes her family became a target for conversion after the synagogue in their area was destroyed, leaving them without formal affiliation to a recognized religious institution. On two occasions, she said, the IRGC raided their home during Jewish holidays, searching for evidence of religious practice. When they found a menorah, her father was detained. “When my dad came back, he was a ghost.” She fears that members of the destroyed synagogue could now face a similar vulnerability.
In Iran, certain religious minorities, including Jews, are constitutionally recognized. But she says that their protection is closely tied to existing institutions.
“When we talk about the lack of protection, it has a very nuanced meaning. In Iran, this doesn’t mean that the synagogues cannot exist, but it means that the existing synagogues are the only legal protection that Jews do have,” she said. “Good luck with rebuilding that place. Good luck with asking for a new synagogue.”
Sabti said the regime has already used the synagogue’s destruction as propaganda, publicly condemning the attack while reinforcing the state narrative of religious inclusion. “The head of the Islamic clerics condemned Israel and paid condolences to the Jews,” he said. “Everyone pays condolences and says, ‘Oh, sorry, we are in this together’ … but everyone knows that the other one also is lying.”
An American Jewish detainee
For one Iranian American Jew, the war has made a dire situation worse.
Kamran Hekmati, a 70-year-old Iranian American from Great Neck, New York, traveled to Iran in June 2025 and was detained during the 12-Day War. According to advocates, his alleged crime was traveling to Israel 13 years earlier for his grandson’s bar mitzvah.
Kieran Ramsey of the Global Reach advocacy group, who represents Hekmati’s family, said in an interview that Kamran being the Iranian regime’s only Jewish American prisoner puts him in a particularly precarious position. “There can be risk of retribution or reprisals against him at any moment,” Ramsey said, “from prison guards or other prisoners…his identity certainly puts him at higher risk.”
On March 16, almost three weeks into the war, Secretary of State Marco Rubio designated Hekmati as wrongfully detained, a status that allows the federal government to deploy all possible levers — diplomatic, legal, and economic — to secure his release. Ramsey says that change in designation is helpful, but only goes so far.
His organization is now pushing for the release of all American prisoners in Iran to be an integral part of the U.S.-Iran negotiations to end the war.
“Our hope is that Kamran Hekmati and the other Americans that are being held are put to the front of the list in terms of issues to decide, and not as a deal sweetener,” he said adding, “We know the U.S. negotiators have a list of American names. We know Kamran is at the top of that list…. We also know there are some very rational actors inside the regime, and we are trying to convince them that you have a no-cost way to open doors. Use Kamran as that no-cost way.”
The last time the woman who emigrated in 2008 visited Iran was two years ago. Even then, she worried that photos taken of her in the U.S. wearing a Jewish star necklace might draw the regime’s suspicion.
Now, she believes whatever space existed for quiet concessions from the Iranian government to Jews may disappear. The regime’s efforts to retain a firm grip on the Iranian people following January’s massive anti-regime protest wave and the war pose new risks.
“Just because of everything that has happened… I’m sure that any type of like ‘OK, let this go,’ ‘Let this person go,’ will end,” she said.
“Now I know that I could not go back,” she added. “I really feel if the Islamic Republic stays — and they probably have a good chance of staying — I feel like I lost Iran.”
This story was originally published on the Forward.



