Features
“The Goddess of Warsaw” – recently published novel weaves story of Warsaw Ghetto resistance with modern-day Hollywood intrigue
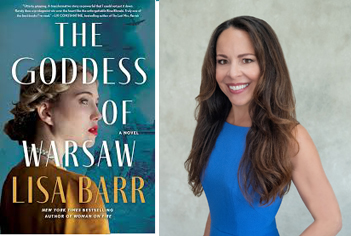
Reviewed by BERNIE BELLAN Here’s a recipe for a great novel: Take one part story of an aging Hollywood former screen star, add in a second part World War II backstory revolving around the Warsaw Ghetto, and finish it with a third part Jewish revenge on Nazis story (remember Quentin Tarantino’s “Inglorious Basterds”) – and you have all the makings of a fabulously good read.
Such is the case with a recently released novel titled “The Goddess of Warsaw,” by American Lisa Barr.
According to the bio on her website, Lisa Barr is the “New York Times and USA TODAY bestselling author of, in addition to THE GODDESS OF WARSAW , WOMAN ON FIRE, THE UNBREAKABLES, and FUGITIVE COLORS. Lisa served as an editor for The Jerusalem Post, managing editor of Today’s Chicago Woman, managing editor of Moment magazine, and as an editor/reporter for the Chicago Sun-Times. Among the highlights of her career, Lisa covered the famous “handshake” between the late Israeli Prime Minister Yitzhak Rabin, the late PLO leader Yasser Arafat, and President Bill Clinton at the White House. Lisa has been featured on Good Morning America and Today for her work as an author and journalist. Actress Sharon Stone has optioned rights to adapt WOMAN ON FIRE for film.”
I was looking for a recently published book by a Jewish author that had an interesting storyline, but since I had never read anything by Lisa Barr prior to reading “The Goddess of Warsaw,” I wasn’t quite sure what to expect.
After all, here is how Amazon describes the book: “the harrowing and ultimately triumphant tale of a Jewish WWII assassin turned Hollywood star …
“The Goddess Of Warsaw is an enthralling story of a legendary Hollywood screen goddess with a dark secret. When the famous actress Lena Browning is threatened by someone from her war-time past, she must put her skills into play to protect herself, her illustrious career, and those she loves, then and now.”
The story seemed kind of formulaic – as I noted in my introductory paragraph – a gorgeous femme fatale sort of story, I thought.
But what I thought at first might be a piece of fluff actually turned into an engrossing – and very harrowing read. Sure, the very first chapter sets the scene by describing an aging Lena Browning (the former Hollywood sex goddess) meeting with a young female star by the name of Sienna Hays, who is anxious to play the part of Lena Browning in a biopic that will not only star Sienna, it will be written and directed by her. Sounds like any number of other similar stories of an aging Hollywood star whose true story is not what had been created for her – right?
But quickly thereafter the story takes us to Warsaw in 1943, at a time when the Nazis had already begun the mass deportation of Warsaw’s Jews to Treblinka, ultimately leading to the deaths of almost all of Warsaw’s prewar Jewish population of 400,000.
We learn that Lena Browning’s real name was Bina Blonski, and she was the daughter of a wealthy Jewish businessman who had been murdered by Nazis right in front of her eyes when she was a young teen. Bina, it turns out, is a very talented actress. Not only that, she has all the trademarks of the prototypical Aryan superwoman: tall, blonde, gorgeous figure who, in this case, while not speaking German, speaks perfect Polish.
To Lisa Barr’s credit, however, she has clearly done quite a bit of research about what life was like in the Warsaw ghetto – and her writing does not spare the reader from any of the horrors that became commonplace aspects of life there.
I was somewhat afraid that the story would go back and forth between wartime and the present – which is 2005 in this case, when Sienna first meets Lena. I’m no great fan of trying to keep events in mind that happened several chapters back. But Barr, it turns out, is a masterful storyteller who, while she does engage in leaps back in time to help explain how certain things turned out the way they did, concentrates for the most part on Bina’s time spent in the Warsaw Ghetto.
There is a love story as part of the novel, and it revolves around Bina’s being in love with one man, Alexander, while she is married instead to his brother, Jakub. What happens to both Alexander and Jakub provides many surprises through the course of the book.
It is Bina’s story throughout, however, that continues to pull in the reader. As others around her come to realize, her talent as an actress lends itself fully to the mission that the leader of one group of Jewish Resistance fighters in the ghetto has planned for her, which is to send her out of the ghetto and find guns and bomb making material that can be smuggled back into the ghetto.
Bina is able to come into contact with a faction of the Polish Resistance whose leader, as fate would have it, is a longtime actor friend of Bina’s. The dangerous missions upon which Bina embarks are as good as any I’ve read in any spy novel, with the difference being that, according to Lisa Barr’s website, many of which are based on true events.
One particularly gut-wrenching episode though – and one which also stems from something that actually occurred during the latter stages of the Warsaw Ghetto’s existence, involves 93 young Jewish women – most of whom are in their teens, who are taken by the Nazis to be their sex slaves. Bina is instructed by Zelda, the leader of the Jewish resistance, what she has to do as a result. It’s hard not to read the description of what happens without your stomach ending up in knots.
Since we know from the start that Lena, a.k.a. Bina (also Irina, when she has to impersonate a Polish woman while she is living outside the ghetto) will survive the war, the question becomes: How did she go from being a Jewish refugee to a Hollywood actress of great fame – and talent?
Barr fashions a believable scenario that is not beyond the realm of possibility for explaining how Bina Blonski is able to transform herself into Lena Browning, but what I found a little hard to believe is how someone whose face would have become familiar to millions of movie fans around the world – and who had not undergone any plastic surgery to change her appearance, would have gone unrecognized throughout her film career?
Still, that’s a minor quibble – and hardly enough to get in the way of what is ultimately a riveting story.
With a combination of excellent research and an admirable talent for storytelling, Lisa Barr has fashioned a compelling book that should appeal to readers of all ages and genders.
Since so much of the action takes place at a time when Bina Blonski is a very young woman and many of the characters with whom she has connections in the Warsaw Ghetto are only teens themselves, I would think that The Goddess of Warsaw is a novel that might also appeal to teen readers. Some parts might be awfully difficult for younger readers to read , such as what happens on a day-to-day basis to children in the ghetto, but in the end, this book is so compelling that I would recommend it to anyone.
The Goddess of Warsaw
By Lisa Barr
368 pages
Published by HarperCollins
May, 2024
Available on Amazon
Features
Israeli Government Report Ranks World’s 10 Most Influential Antisemites

Israel’s Ministry of Diaspora Affairs and Combating Antisemitism published this week its official ranking of the 10 most influential antisemitic figures in the world in 2025, and the No. 1 spot was given to social media influencer Dan Bilzerian, who is running for US Congress in Florida.
The Armenian-American entrepreneur and US military veteran is a prominent critic of Israel and Judaism who has promoted antisemitic conspiracy theories and Holocaust denial. He has said he wants to “kill Israelis” and thinks Judaism is “terrible.” He recently claimed antisemitism is a “made-up term” and there is a “big Jewish supremacy problem” in the United States. He formally filed paperwork earlier this month to run as a Republican and unseat incumbent Jewish Rep. Randy Fine in Florida’s 6th Congressional District.
Swedish climate activist Greta Thunberg is the world’s second most influential antisemite, according to Israel’s Ministry of Diaspora Affairs, which highlighted her use of terms such as “genocide,” “siege,” and “mass starvation” in reference to Israel’s military actions in the Gaza Strip.
Third place was given to Egyptian comedian and former television host Bassem Youssef, followed by far-right American political commentator Candace Owens in fourth place and Palestinian-British journalist and editor Abdel Bari Atwan in fifth.
The list includes American imam Omar Suleiman, Denmark-based doctor Anastasia Maria Loupis – who has shared online conspiracy theories about Jews and Israel – far-right commentator and white nationalist Nick Fuentes, and conspiracist Ian Carroll.
Rounding out the top 10 is far-right podcaster and former Fox News host Tucker Carlson, who regularly promotes antisemitic conspiracy theories about Jewish influence.
Israel said the 10 most “prominent influencers in the global antisemitic and anti-Zionist arena in 2025” were selected based on “both the severity of their actions/statements and the scope of their influence” related to their activities last year. “Each of them has expressed antisemitic views or promoted false information related to Jews, Israel, or both,” the ministry explained. The list does not include individuals with formal political or government positions.
Each individual was ranked based on their influence on social media, but also other factors such as their repeated appearances on news channels, “perceived influence on public opinion, and prominence in certain communities.” The ministry also took into consideration each person’s “level of impact and risk,” which includes how often they upload antisemitic and anti-Israeli posts on social media. The report was released ahead of Israel’s Holocaust Remembrance Day, known in Hebrew as Yom HaShoah.
In a separate section of the report dedicated to antisemitic and anti-Israel influencers in the US, Israel’s Ministry of Diaspora Affairs singled out YouTuber and children’s educator Ms. Rachel, who has “increasingly used her social media accounts to amplify pro-Palestinian messages and criticize Israel.”
“Her posts have been interpreted by pro-Israel organizations as one-sided and hostile to Israel, and organizations such as StopAntisemitism have accused her of spreading anti-Israel or pro-Hamas propaganda and called for an examination of her activities,” the ministry stated.
Features
4000 Quarters for my Uncle Lew – a new story by David Topper

Introduction: David Topper has been featured on this website many times. His stories about Albert Einstein have drawn huge audiences, but David’s interests range far beyond writing about science. Most recently, we have featured stories about “Jews in strange places.”
If you want to find all of David Topper’s stories that have appeared on this site, just enter his name in our search engine (the magnifying glass). Here’s David’s latest story – but be warned: As David told me, it’s a “story”:
I adored my Uncle Lew. He was one of many uncles in the large extended family on my mother’s side. Of course, this means that there were many aunts too. But there were not many cousins – at least, none my age. And I was an only child; so I guess you could call me an “only cousin” too. At least when I was very young – say, from ages 6 through 12 or so – until many cousins were eventually born. In all, it seems that I was alone, in those early years.
But I’m digressing already, and I just want to tell you about my grandmother’s brother, my Uncle Lew. You see, he lived in the same city when I was very young, and he came to visit a lot – especially on Sundays, when there was a large gathering of the extended family at my grandmother’s home, with lots of food. He came with his wife, Aunt Lil. But it was Lew who was especially nice to me. He always came with jokes; jokes that the adults laughed at – and I did too, but often not really knowing what was funny.
Most importantly, for me, sometime during the visit, Uncle Lew would sneak up behind me and put his hand in the right side-pocket of my trousers. I knew what was happening, and so I’d just walk away to a quiet part of the house, reach inside my pocket, and pull out a shiny quarter. Rubbing it in my hands, thinking about what I might buy, and putting it back in my pocket – I was happy, and set for the week to come. You must realize that this was sometime in the late 1940s and into the 1950s – and a quarter was worth a lot to a kid. These were the days when a penny could buy a nice treat at the candy store nearby where I lived. And, well you do the math: a quarter was worth 25 pennies. Yes, I adored Uncle Lew, although I’m not sure I would have used that word at the time.
Speaking of money. I remember that the family, especially the men, talked a lot about money. I’m not sure that many of them had a lot of it, since most were of the working class. Maybe that’s why they talked about it. Although I suspect that rich people spend a lot of time talking about money too. Yet, what do I know?
I mention this because, at some point – I don’t remember the date or my age – but Uncle Lew and Aunt Lil moved to another city. Thus: no more shiny quarters in my pocket at the Sunday dinners. Instead, I listened to the talk, mainly among the men, about Uncle Lew. And as best I could surmise: Uncle Lew owed people money that he didn’t have, and so he had to skedaddle to save his skin. It made me think about my quarters, and if I had put them in the bank, maybe I could have helped Uncle Lew pay back his debts. But now it was too late. Uncle Lew was gone and I spent all the quarters on myself – my selfish self, I thought sadly.
But Uncle Lew was not completely out of my life. A few years later he came to town for a short visit. He came for a weekend; and had Sunday dinner with the family. I guess he thought it was safe enough. And nothing happened. So, he did it again, a few months later. And so it went. Thus, Uncle Lew was not out of my life completely. And yes, a quarter was deposited in my pocket on the Sunday dinners. As well, by now, I had a bank account; and I occasionally put Uncle Lew’s quarters in the bank – just in case he might need a loan someday, I thought.
Oh, I forgot to mention: he now came alone. From the talk of the adults, I figured out that he and Aunt Lil were divorced – something my mother later explained to me, because in those days it was not a common occurrence. And people were often embarrassed to talk about it.
Now fast forward several years to the late 1950s, when I was in High School. One day Uncle Lew appeared out of nowhere, carrying all that he owned in a few suitcases. I don’t know why, but he stayed with us. Being an only child, I had a room of my own and so the family got a cot from the basement and they put it in my room. I was okay with this, since I always liked Uncle Lew and was glad to know that he was safe with us.
Our first night together – I in my bed and he a few feet away in the cot – was memorable. Because, in the middle of the night, I woke up and saw a spark of light moving around the room near Uncle Lew’s cot. I guess I forgot to tell you that Uncle Lew was a smoker. Of course, smoking was common in those days, so it was no big thing that he smoked. In fact, if you watch any movie from that period, every time people walk into a room and sit down to talk, someone takes out a pack of cigarettes and they all light up. But I digress, again. Anyway, as you may have surmised, the spark of light moving around in the dead of night was Uncle Lew having a smoke. He was so addicted to cigarettes that he couldn’t get through a night’s sleep without one. And so it went: night after night.
Also, at the time he moved in with me, I was working on building a model airplane out of balsa wood. I usually worked on this in the evenings, after I did all my homework. The parts were strewn across a table in my room, and Uncle Lew often watched me assemble the plane – saying he hoped to see the plane actually fly someday. He said he enjoyed watching me put the thing together (since he seemed to have nothing else to do), and I enjoyed the conversations. I glued pieces of balsa wood together and he smoked cigarettes, depositing the ashes in a tray on my table.
In a short time, I came to understand why Uncle Lew was here. When I was at school during the day, my relatives were taking turns driving Uncle Lew to the hospital for treatments. In those days, people didn’t talk about some things directly. Especially cancer, which was a word that was often spoken in a hushed voice. So that was it; he had lung cancer.
At the same time, Uncle Lew was seeing a dentist for the pain he was having with a tooth in the right side of his mouth. He showed it to me one day, while I was working on my airplane. He was sure that the dentist knew what he was doing, and Uncle Lew was looking forward to getting it removed and replaced with a new tooth. We didn’t talk about the cancer, but looking back on this I can only surmise that Uncle Lew was in denial – or he was overly optimistic about the cancer treatments.
In a short time, the tooth was removed and replaced by the false one. Uncle Lew was elated, and told me that it was the best $1000 he ever spent. Yes, $1000 for the tooth. I don’t know where he got the money. And I’m afraid to ask, for obvious reasons. But I now also question the ethics of that dentist, allowing a patient undergoing cancer treatments to spend so much money. But maybe the dentist didn’t know. Then again, where were my relatives in all this? I am only thinking of this now. As for all things in life while growing up: what is, is reality for that time, and you just go with the flow. Only later, looking back, do you see the quirks and foibles of the past.
Indeed, did I think of helping Uncle Lew with his dental bill? I had a bank account. And some of that money was from deposits of Uncle Lew’s quarters. I don’t know. What I do remember is that not long after the new tooth was planted in his mouth, relieving him of that pain, the cancer got worse – and he spent the rest of his days in the hospital. And that’s where he died.
At the funeral I wanted to mourn. To grieve at the loss of this beloved uncle, who lived with me in the last stage of his life.
But I kept thinking about that tooth – that damned $1000 tooth. While saying the prayer for the dead, the Kaddish, I wanted to concentrate on the meaning of the prayer – even though I couldn’t read Hebrew. But that costly tooth kept flashing in front of me – like the spark of Uncle Lew’s cigarette in the middle of the night.
Even when the body was lowered into the grave, and I took my turn throwing several shovels of dirt over Uncle Lew’s plain wooden coffin – in my mind, I was doing the math: how many quarters are there in $1000?
In a way, on that day, and in my mind, I really buried a tooth – and it just so happened that a body came along with it.
My one consolation in all this is that about a few weeks after the funeral, I finished building my airplane; and I took it out to an empty ball-field near where I lived. Just me and my airplane.
The propeller was attached to a rubber band, and so I wound it up and gave it a push. It took off, rising up, almost as high as the trees beyond the outfield. Then it banked a bit toward the left; and, after heading back towards me, it moved in a circle – almost overhead. It continued circling – rather as if it were caught in a tornado – moving down and down.
When it crashed into a heap of shards of balsa wood right next to me standing on the pitcher’s mound … I laughed, a deep laugh – a laugh that turned into crying. A deep cry – a cry I sorely needed.
Sitting in that empty field next to my shattered airplane – looking up and beyond the trees – I screamed to the sky. “There are 4000 quarters in $1000.”
I walked home, and went to my room. Sitting at my empty table, I said to myself out loud. “I guess I should build another airplane. What do you think Uncle Lew? Let’s go to the store and use some of those quarters to buy another model airplane. Maybe this one won’t be jinxed. What do you think?”
But before leaving the house – and for the first time since Uncle Lew died – I was able to fold up that cot and put it back in the basement.
Features
Part 3 of the story of the delusional Winnipeg con man
An explosive email arrives in my inbox on January 16
By BERNIE BELLAN This is the third part of a story about a delusional Winnipegger who has inflicted great harm on people over the world. The first two parts of the story can be read at Part 1: “The delusional Winnipeg con man who actually believed his own elaborate con and led one victim in Africa to consider committing suicide” and Part 2: “Meeting the con man for the first time in 2021.
I would probably not have given another thought to Devlin had an email not arrived in my inbox on January 16, 2026.
That email came from someone I’ll call Charlie. It was so explosive in how it described a vast pattern of broken promises and shattered trust which Devlin had engendered among a wide number of individuals that I was totally floored by what the writer of that email wrote. (Again, I’ve changed Devlin’s name in the email from his true name.)
The subject line of that January 16 email was “The Winnipeg Con Man.” Here is that email in its entirety:
“This report is being posted by a group of individuals who connected privately after discovering that we share strikingly similar experiences involving Frederick Devlin, also known as Fred. Our experiences span anywhere from approximately two years to as long as five, ten, twenty, and in some cases thirty years.
“Across this group, many of us were in frequent communication with Fred, who consistently presented himself as an extraordinarily wealthy and powerful individual with vast global influence and resources. He represented himself as a business leader, investor, or partner and repeatedly assured people that significant funding, compensation, or major opportunities were imminent.
“Over extended periods of time, many of us were told repeatedly that money, contracts, payment, or formal agreements would happen next month or very soon. Despite these ongoing assurances, no verifiable proof of funds, legal documentation, contracts, or concrete follow through ever materialized. Expectations and conditions for moving forward were frequently changed, and individuals were encouraged to continue investing time, labor, trust, and emotional energy without any tangible results.
“As time went on, the claims being made became increasingly extreme and difficult to reconcile with reality. Among the statements reported by multiple individuals were claims that he was the world’s first trillionaire, that he owned thousands of companies, that some of those companies generated billions of dollars per hour, that he owned hundreds of hospitals, hundreds of airports, and thousands of aircraft, and that he controlled vast global infrastructure. He also claimed ownership of thousands of acres of land in both Winnipeg and Israel.
“Additional claims reported include involvement with intelligence agencies, building the Third Temple in Israel, statements that Osama bin Laden was still alive and being held for future rehabilitation, and claims of direct communication with God and receiving guidance from God. He also claimed personal relationships with world leaders and public figures and suggested that he would assume positions of power under certain circumstances. None of these claims were ever supported with evidence despite repeated requests for verification.
“He also represented entities referred to as Xanadu Group of Companies Worldwide and Xanadu Foundation Worldwide as major global organizations under his control. Based on the experiences shared within this group, these entities appear to have no independently verifiable operations, assets, or legitimate structure. Multiple individuals report having worked for extended periods under these names without pay, believing compensation or success was imminent, only to later realize that no payment or formal organization existed.
“Organizational Roles and Unpaid Labor
“Members of this group report a consistent pattern involving individuals who were presented as part of an organizational structure surrounding Fred. These individuals were described as executives, managers, legal advisors, financial professionals, technical staff, or personal assistants connected to the entities he promoted.
“Several individuals report that his spouse was present during meetings and communications with prospective partners or workers, sitting alongside him while representations were made about business operations, funding, and future opportunities.
“Multiple people were introduced to individuals described as senior executives or operational managers who were said to oversee large numbers of companies or global activities. In some cases, individuals were told they were responsible for managing thousands of companies or acting as official representatives on his behalf. These roles were presented as legitimate and authoritative, yet compensation, contracts, or formal structure never materialized.
“Some individuals report being encouraged to create their own business cards, travel internationally, and attend meetings while representing him or the organizations he promoted. These activities were carried out under the belief that the companies were real and that long term compensation or equity was forthcoming. In at least one reported instance, individuals were aware of staged humanitarian activity that appeared to be conducted primarily for promotional imagery rather than meaningful aid.
“Other individuals report providing extensive professional services without pay, including legal work, financial and accounting services, website development, administrative support, and personal assistant duties. These services were reportedly performed over extended periods under the belief that formal employment, payment, or senior roles within a large organization were imminent. In some cases, individuals were asked to assist with sending legal notices or cease and desist communications aimed at discouraging others from speaking publicly.
“Across these experiences, it remains unclear whether certain individuals involved were themselves misled, enabling the behavior, or acting in some other capacity. What is clear to the group is that a wide range of unpaid labor and representation was sustained by repeated promises that never resulted in legitimate compensation, contracts, or verifiable business operations.
“Victim Experiences and Patterns of Harm
“Members of this group report a wide range of deeply concerning victim experiences that illustrate how trust was established, exploited, and maintained over long periods of time.
“One individual reported first meeting Fred while both were present in a medical setting. During that time, Fred presented himself not as a patient, but as an extraordinarily powerful and wealthy figure, claiming ownership or control over the facility and suggesting he was operating undercover to evaluate staff. This individual was told repeatedly that he would be financially supported for life. Over time, Fred encouraged him to identify other people who could also be helped financially, creating a chain of introductions built on trust and false assurances.
“Several victims describe being drawn into prolonged, high intensity communication lasting months or years, including frequent phone calls that extended for hours at a time. During these interactions, victims were promised large sums of money, major investments, salaries, or company acquisitions. In some cases, victims were led to believe they would receive life changing financial support or that their businesses would be purchased for significant amounts. Each time deadlines approached, timelines were pushed back by months, with repeated explanations and new promises offered. This pattern continued over extended periods, with victims investing substantial time, planning, and emotional energy based on assurances that never materialized.
“Another individual reported being promised financial rescue after suffering significant losses in a separate situation. Fred allegedly assured this person that debts would be paid, a new business would be launched, and a substantial annual salary would be provided. This individual was reportedly instructed not to pay existing creditors and was warned that doing so would jeopardize the promised support. Relying on these assurances, the individual experienced cascading financial consequences, including loss of credit, housing, personal property, and severe disruption to family life. This experience is described as having resulted in total financial collapse and lasting personal harm.
“Multiple individuals outside North America reported being approached with promises of humanitarian support, development funding, or life changing financial assistance. In at least two reported cases, individuals were instructed to create promotional materials using company logos and to stage charitable activities in impoverished communities, including distributing small amounts of food while being photographed. These images were then allegedly used to promote an image of vast wealth and global humanitarian impact. Victims report being promised assistance for themselves and their communities for five years or more, receiving no financial support, and in some cases spending their own limited resources in the process.
“One individual involved in these humanitarian related representations stated that Fred told him he was in direct contact with senior leadership or directors at major international aid organizations, including USAID, World Vision, Save the Children, and the World Food Programme. These claims were presented as proof of legitimacy and influence, yet no evidence of such relationships was ever provided.
“Other victims describe being used as intermediaries or connectors, introduced to political figures, industry leaders, or international contacts under the belief that legitimate large scale deals were underway. These efforts often involved months of preparation, meetings, and negotiations involving proposed transactions in the millions of dollars. Victims report that these deals consistently collapsed at the final stages, after extensive time and effort had already been invested.
“International Scope of the Conduct
“Members of this group also report that the conduct described above was not limited to a single location or jurisdiction. Individuals involved are located across multiple regions, including the United States and Canada, and in some cases were connected to activities, communications, or meetings abroad. Victims report involvement spanning locations such as Florida, California, Nevada, Manitoba, Ontario, Israel, and multiple countries in Africa.
“Several individuals report being encouraged to participate in or support proposed international business, humanitarian, aviation, or political initiatives, including travel, meetings, and coordination across borders. In some cases, individuals traveled internationally or were asked to act as intermediaries or representatives in foreign countries based on representations that large scale transactions, funding, or humanitarian efforts were underway.
“As a result, the time invested, financial loss, and emotional harm described by victims occurred across multiple legal jurisdictions, complicating efforts to seek accountability and increasing the number of individuals potentially affected. Victims report that the same patterns of representation, delay, and nonperformance were repeated consistently regardless of location, suggesting a widespread and sustained pattern rather than isolated incidents.
“Attempts at Family Intervention”
“Members of this group also report that concerns were raised directly with his family members in an effort to prevent further harm and encourage intervention. According to individuals involved, family members acknowledged long standing issues and expressed a desire to keep matters quiet in order to avoid upsetting Fred.
“Despite being alerted to the concerns raised by multiple individuals, the response described by victims focused on minimizing confrontation rather than addressing the underlying behavior. Victims report that Fred continued to receive financial support for daily living and social activities, allowing him to maintain the appearance of legitimacy while continuing to hold meetings, conduct outreach, and make representations to others. Many victims believe that the lack of intervention contributed to the continuation of the behavior described above, increasing the number of individuals affected over time.
“Taken together, these accounts describe a pattern in which extraordinary promises, constant engagement, emotional manipulation, and shifting timelines were used to sustain belief and participation, resulting in severe emotional, financial, and psychological harm to numerous individuals over many years.
“Members of this group report a wide range of impacts. Some individuals describe being encouraged to work for months or years without pay under the belief that compensation or equity was imminent, which never occurred. Others report significant financial strain after rearranging their lives, careers, or commitments based on repeated assurances that funding or payment was coming. Several individuals describe being threatened with legal action or intimidation when they attempted to question claims or speak publicly about their experiences. Others report emotional distress and long term psychological impact after years of being strung along by false promises and grand representations.
“Many individuals also report being asked for access to personal or professional contact networks, raising concerns that trust and reputations were being leveraged to gain credibility with others.
“As a result of connecting and comparing experiences, members of this group have taken steps to protect others. Some have contacted the Winnipeg Police Service and crime and fraud units within multiple Canadian agencies to request investigation. Some individuals are pursuing civil legal action. Others are warning their friends, families, and professional networks after believing they may have been targeted or approached in similar ways.
“This report is not being posted out of anger or malice. It is being posted because the consistency, duration, and severity of the experiences reported by many individuals raise serious concerns. We believe others deserve to be warned so they can protect themselves and insist on independent verification before engaging in any personal, professional, or financial relationship.
“If you have had a similar or concerning experience involving Fred Devlin, we encourage you to share your experience so others can be informed.
“This report reflects the collective experiences and observations of multiple individuals. All readers are strongly encouraged to independently verify any claims before proceeding.”
Wow! That was quite the email. But why was I on the receiving end? I wondered. It seemed to be intended for others who might have been taken in by Fred.
But, I was deeply curious why I had been sent that email, so I responded:
“Hi,
“Interesting that you got my name. I wonder where that came from? I met Fred a couple of times over the years and knew immediately that he wasn’t right, but I humoured him and made him think that I believed the nonsense he was feeding me. I didn’t take me very long to establish that nothing he was saying was true – except maybe for the part about Izzy Asper having thought that he had great potential. Fred likely had great ability at one time (he did show me a photo of him descending a jet with his company logo emblazoned on the jet) – but apparently something happened somewhere along the line that led to his delusional behaviour. I contacted Fred”s mother (whom I hold in very high regard) at one point and asked her how she thought I should respond to Fred’s request that I do a story about him – and her response was to treat him gently – which I did by not calling him out to his face. What I don’t understand is how he suckered so many people into believing the crap he was feeding them. How long would it have taken to verify that his ‘Xanadu’ group of companies didn’t exist?
Regards,
“Bernie Bellan
“Former publisher,
“The Jewish Post & News
“and current publisher,
“jewishpostandnews.ca”
I didn’t hear back immediately from Charlie. As events transpired, it was only after a couple of months had passed that I did hear from him – apparently after he had been persuaded by another individual who turned out to play a key role in putting this story together for me (I’ll call him Rick), that he (Charlie) could trust me.
I received a text message from Rick the same day that I had responded to Charlie in which Rick told me that he had all the information I would need to write a full exposé of everything Fred had done to so many individuals.
But, what kept gnawing at me was that there were so many references to a host of different individuals, all involved somehow in helping to perpetrate this vast fraud, at which Devlin was at the centre.
According to that January 16 email, “Multiple people were introduced to individuals described as senior executives or operational managers who were said to oversee large numbers of companies or global activities. In some cases, individuals were told they were responsible for managing thousands of companies or acting as official representatives on his behalf. These roles were presented as legitimate and authoritative, yet compensation, contracts, or formal structure never materialized.”
Who were all these individuals who were supposedly senior executives or operational managers? I wondered. As time wore on, I never came across anyone who could be said to have been working as a senior executive or operational manager in any of Devlin’s companies – because none of those companies ever existed! Thus, as I noted earlier, there are so many rabbit holes in this story – and so many of the individuals to whom I spoke also seemed to be suffering from their own mental illnesses, I still have no idea how much of what supposedly was written in that explosive email was true.
What I did discover though, was that the email had not been written by Charlie, it had been written by someone I’ll call Rick. Why Rick wanted to disguise his identity when he sent me that email, I’m not sure. What I did find out, however, was that Rick himself would veer in and out of normalcy – and what began as a level headed discussion between us ended with him angrily cutting off communication with me for a very long time. Then, when I decided to try to reestablish contact with him, he was perfectly normal – again. Rick proved invaluable in putting me in touch with others who were able to provide me information about how Devlin had conned them, so I still owe him a great debt of gratitude.
Coming next – Part 4 of the delusional con man: How one man was at the centre of figuring out everyone who been conned by the delusional Winnipegger



