Features
Berdina Shorten: Her long and circuitous journey to returning to her Jewish roots
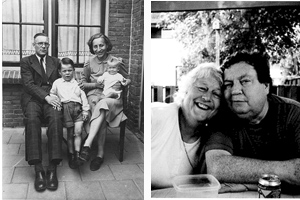
By BERNIE BELLAN Berdina Shorten has lived in Winnipeg since coming here with her family from the Netherlands in 1953. Although Berdina was Jewish by ancestry (going back to her great-grandmother), she hadn’t been raised Jewish. It was only several years after having come to Canada – and having got married, that Berdina – and her late husband, Ken Shorten, both converted to Judaism.
Typically, the stories we publish in this paper about people’s wartime experiences have to do with the Holocaust. Those stories are all certainly horrendous – and almost always riveting, but when I happened to be talking to Berdina about a totally unrelated subject (the renewal of her subscription) and the conversation got around to her wartime experiences, I said to her that I wanted to write about her story.
I should also mention that I had heard Berdina speak at the Shaarey Zedek several years ago, but at that time I didn’t take any notes. (I can’t recall exactly why I was there or how I happened to be in the room when Berdina told her story, but I remember thinking that this would make a great story for the paper some day.)
In any event, here’s a recounting of the first part of Berdina’s story, based on a phone interview that I conducted with her on February .
First, a little history is needed, in order to understand the context for what happened to Berdina and her family.
The German army had invaded Poland in September 1939. After consolidating its gains there, Germany turned its attention to Western Europe in April 1940, first by invading Norway and Denmark, then launching an attack through Belgium into that country, also the Netherlands and Luxembourg (despite those three countries having adopted positions of neutrality).
The German invasion of The Netherlands began on May 10, 1943.
That is where Berdina’s story picks up. But first, a little background on her family history.
Berdina’s father, Theodore (or Theo, as he was known) was a master leather cutter. His “family was Protestant, but his mother was Catholic, so he was raised Catholic,” she said.
As Berdina explained, “his family had come from France in 1610. He used to say the reason his family didn’t go to the New World was ‘no pretty cruise directors, no first class cabins, no air conditioning.’ The real reason was they were Huguenots and they weren’t allowed to go to the New World – unless they went to England and went with the Protestants,” e.g., the Pilgrims on the Mayflower.)
Berdina’s mother (Anna), however, “was born Jewish” but, as Berdina noted, “the family never practiced Judaism. What happened was her mother was born Jewish to a Dutch girl and a German Rhine skipper. Her father died when she was four years old, so her mother went back to Holland, but her family wouldn’t accept her back because she had married someone who was not Jewish. She raised her child (Berdina’s grandmother) with the help of local charities and working in a grocery store.
“When she met my great-grandfather, he was more Catholic than the Pope, so she never practiced her religion and she raised her children as Catholic – but they were actually Jewish – by Jewish law.
“It wasn’t until I was 12 – and I had been sent to Catholic school. I was always challenging the nuns. I wanted to check out Judaism, but I wasn’t allowed.
I asked Berdina whether “she had an awareness that she was Jewish?”
She said she did. “I always knew. My mother knew also, but they hid it.”
I asked then how she knew about her Jewish heritage?
She answered: “My relatives. I heard conversations when I was a child.”
While, Her mother “didn’t practice any religion, her “father did. He’d go to Mass once in a while,” Berdina noted.
When the Germans invaded the Netherlands, Berdina’s father was in the Dutch army, fighting on the “Grebenberg (or the Grebbe line, the main line of Dutch defence)– where they held the Germans back for many days.” (Actually, it wasn’t many days at all – only three. The Dutch were badly equipped and totally outmaneuvered by the Germans.)
Berdina continued her story: “My father was a fantastic shot…But the Queen (Wilhelmina) capitulated. They were bombing the hell out of Rotterdam (May 14, 1940).” The Netherlands surrendered the next day.
Berdina’s father was taken prisoner and sent to work as a forced labourer (in Germany): “So my father was taken and put into a factory. He was a master leather cutter – making shoes.”
Berdina’s family lived very close to the German border with the Netherlands. Thus, even though Theo was forced to work in Germany, it was only a three-hour walk for him to return to his hometown – and his family. It seems somewhat strange to think of someone who’s kept as a forced labourer – which Berdina described as “slave labour”, yet who was allowed to return home on weekends, as she explained:
He was allowed to go home (where mother lived) once a week, Berdina said. “He was given one egg a week, so he would take that egg with him, so my brother (Corey, who was born four years before Berdina) would be able to have at least a little bit of protein in his diet.”
All the while Theodore though, was part of the Dutch underground– meeting with other members of the underground surreptitiously while he was in forced labour for the Germans.
Berdina told this story about one harrowing brush with danger her father had while he was in the resistance: “A story he told was that he was going to a meeting (of the underground) with a friend. They were caught by a young German soldier and the soldier” pointed his rifle at them and “told them to put their hands up. Somehow my father was able to overtake this young soldier.
“His friend said ‘We have to run.’ My father said, ‘No, we can’t. If we run and they find him (the soldier), they’ll kill ten people on this street.“ (That was the retribution the Germans typically exacted, Berdina explained.)
“So my father was able to get a hold of some liquor, put it over the kid’s mouth, then took his guns and papers to the nearest police station, which was controlled by the Germans, and said: ‘One of your soldiers was drunk and we took his guns and papers before he hurt someone.’
“My father was given a pass to go anywhere he wanted that night.”
I asked Berdina if she knew when it was that her father fled the factory for good and ended up going totally “underground” with the Dutch Resistance, but she said she didn’t know exactly when that happened.
When the Canadian army reached Holland in September 1944, anyone who had been in the Dutch army was able to join the Canadian army, Berdina explained, so her father ended up joining the Canadian army.
“When the Dutch army reorganized, he went back to the Dutch army.”
Her father was uncomfortable talking about what he did during the war, Berdina noted, but according to her brother, Theo had once told him that he “had killed at least one German that he knew of (a sniper) and probably more, but he wasn’t sure.”
I asked Berdina whether there were any other memories from the war that she wanted to talk about.
She said there was a young girl – only 14, in her town, “who was the first girl (in Berdina’s home town) to get pregnant by a German soldier.”(That soldier died in a plane crash coming back from North Africa, Berdina added.) “She was also the first girl to get pregnant by a Canadian soldier.
“After the war the people in that community were going to get her and shave her head and send her packing.
“My mother said to my father: ‘That little girl is still only 15 years old. She’s still walking around in Bobby socks and skipping with a skipping rope. Theo (Berdina’s father), could you please do something to stop those people from hurting her?’
“My father went out on to the street and he saw about 50 people coming for the girl. He stopped them.”
In 1953, Berdina, along with her parents and three brothers (two of whom were born after the end of the Second World War), came to Canada.
“My father started to work as leather cutter in the Canada West shoe factory,” Berdina explained.
“Maitland Steinkopf hired him. Eventually my father started to work in St. Boniface Hospital; he’d had a year’s medical training in Edinborough after the war – so he started to work in the hospital, in the x-ray department.
“He worked four hours a night doing piece work for Maitland. He made more money doing that than he did in the hospital.”
I was curious to know more about Maitland Steinkopf and his connection to the shoe business. I knew that Steinkopf was a very successful businessman who also played a leading role in the development of the Centennial Concert Hall, as well as being a prominent Conservative politician and cabinet minister, but other than that I didn’t know much about him.
Berdina said to me that Steinkopf’s success in the shoe manufacturing business was a result of his decision to go to Minneapolis at one point and come back with the Canadian rights to a line of shoes called “Hush Puppies”. That reminded me of another famous decision made by a local Jewish businessman – Samuel Cohen, who decided to begin importing transistor radios made by a company called Sony.
Turning to Berdina’s decision to become Jewish, here is how she explained how that came about:
“My late husband, Ken Shorten (whom I incorrectly referred to as Frank in my previous article), came from an Irish family – that originally came to Canada in 1690, and they farmed in the McCreary area.
“He worked in Eatons – and I worked in Eatons as well. That’s where I met him and we got married.
“Well, he was Protestant and I had been raised in a Catholic environment. We decided that we weren’t going to let the difference in our faiths have a negative effect on us, so we just stuck to ourselves when it came to the religious part.
“But that didn’t work for me and it didn’t work for him and I always knew about my Jewish heritage, so I said to him one day: ‘You know, I’d like to learn more about Judaism; it’s part of my heritage.’ And he said: ‘Me, too.’
“He had some very good Jewish friends at the time (who were all in the NDP). One of them was Cy Gonick, another was Harry Shafransky. He got to know quite a few Jewish politicians. He liked their ethics, liked their values, and so we started to look into Judaism.
“We went to see Rabbi Nesis and (the late) Rabbi Berkal, and we studied with them for two years, and then made the conversion.”
Interestingly, Berdina said that she also spoke with (the late) Rabbi Weizman, who told her that “You can’t convert – you’re already Jewish”.
“But, I said to him, ‘It’s my decision. It’s my journey. I want to do the process.’
“We had two children that we had adopted before we decided to convert – and we brought them in with us.”
I asked when this all happened?
Berdina said the conversion process went from 1973-75.
“We were officially converted in May of ’75,” she said, “and then we were married in the rabbi’s office again.”
“I sang in the Shaarey Zedek choir for 36 years,” Berdina added, “and my son, Theodore, sang in the choir for 20 years…and both kids had their bar and bat mitzvah together.”
“It was the best decision I ever made in my life,” Berdina observed. “It completed me as a human being. I finally fit – because I used to question those nuns. I must have been a real pain in the tuch.”
I asked, “Do you have relatives remaining in Holland?”
Berdina answered: “Yes, I have many.”
I asked, “Are any of them Jewish?”
She answered, “I have one cousin who recognizes himself as Jewish – and that’s it.”
I said to Berdina that what she had told me about her Jewish ancestry and her family’s subsequent conversion to Christianity, it jives with what I had read about how commonplace it was for Jews to have become Christians. I said that I recalled hearing from the late Rabbi Rappaport that only about one-quarter of all Jews in Europe remained Jewish through the years. The rest either converted willingly or by force.
During the course of our conversation, Berdina told me many more stories about her wartime experiences in the Netherlands, all of which were fascinating. Since she was only two years old by war’s end, naturally the stories she tells are one that have been recounted to her by others, but they are all worth retelling.
One that stood out for me in particular was about a Jewish doctor who was kept hidden by his Dutch housekeeper, unbeknownst to anyone else in the town. According to Berdina, when German soldiers came to the house looking for the doctor in 1940, the housekeeper said to them: “I kicked him out long ago when I knew you would be coming. He was miserable to work for and he never paid me enough.”
All through the war that housekeeper was ostracized by her fellow townspeople, as the doctor was universally loved. As Berdina told it, when the town was liberated by Canadian soldiers in 1944, the doctor emerged from the basement – where he had been kept hidden the entire period of occupation by the housekeeper.
Berdina is a great storyteller and when I asked her whether she’d be willing to tell her story to other audiences – as I had heard her do several years ago at the Shaarey Zedek, she readily agreed. If a day comes when Berdina will be able to tell her story to a new audience, I’ll be sure to post something in this paper.
Features
The complete story of the delusional Winnipeg con man who duped people all over the world

By BERNIE BELLAN I have been publishing different chapters from a book I have written about a Winnipeg man who has been telling people for years that he is someone of great wealth who wants to invest in various projects in which those people are engaged.
I’ve now compiled those stories into one large pdf file, which you can read here – or download as a pdf. Simply click on the image below to open the pdf:
Features
I’m 15. Here’s why Kinew’s social media ban needs work

By NOAH STRAUSS I’m 15 years old, and last Saturday night at an NDP fundraising gala, Premier Wab Kinew announced his intentions to ban social media and AI chatbots for kids. His brief announcement made no clear ruling on the age of his ban. As someone who uses social media daily to communicate with friends, I have some thoughts on whether this is actually a good idea— and how it could work.
If Kinew wants his ban on social media to be effective, he should target kids born in 2014 and younger, placing the ban on kids who have not yet had the time to build their lives around it.
Looking at what other countries have done is a useful starting point. Australia banned social media last year to users under the age of 16. France, also, is currently in the process of passing laws through its National Assembly to ban it for kids under 15. Closer to home, the Liberal Party of Canada recently passed a motion at its convention that would seek to adopt legislation that would ban social media for kids under 16, signalling how controlling social media is becoming a mainstream idea.
Social media isn’t all bad. Yes, it causes developmental issues in teens, and it causes anxiety, but so many of us rely on it every day to communicate, share ideas and spread messages. For someone like me, losing it overnight would cause a massive disruption to my daily life. That is exactly why a blanket ban on all social media for minors would miss the point.
At the age of 12, most kids have not spent too much of their lives on social media before their lives are built around it. Britain has implemented a similar year-based ban, banning those born in 2009 and younger from ever purchasing cigarettes. Banning people before they have a chance to be exposed ensures they cannot get addicted. The same logic applies to social media: If kids never get a chance to become dependent on it, the ban won’t uproot their lives. Implementing a ban for kids born in 2014 and younger will ensure they cannot use social media during their developmental stages, just as Kinew intends.
Beyond the social impacts, there is also a political problem behind the ban. In time, kids who have had social media banned by Wab Kinew will head to the polls. How does this look for the man who took it away from them? It will be hard for Kinew to win over a generation of voters whose first political memory is him restricting their online lives.
Kinew succeeded in at least one category, and that is the blame game. He rightfully made sure that the people of Manitoba should know that this is not the fault of our parents, but it is the fault of the technology companies, whose one goal is to make their products successful through making them addictive to the user.
Good intentions are a start, but if Kinew is serious about protecting kids, the details of his ban matter just as much as the principle behind it.
Features
Part 10 of the story of the delusional Winnipeg con man: The con man asks to meet with me and ends up being thoroughly grilled about the cons he’s pulled

By BERNIE BELLAN This is the tenth -and final part of a story about a delusional Winnipegger who believes he is someone of great wealth and has spent the better part of 30 years contacting people all over the world telling them that he wants to invest in their businesses or projects. The first nine parts of this story are all available to read under the FEATURES category on this website.
Here is the final part of my story:
On April 9, 2026 I finally had a chance to meet with Fred Devlin again. The day before, I was totally surprised when I saw a message from him saying he wanted to talk to me – and gave his phone number (which is the same phone number I had for him from years ago).
I called him – and he was quite pleasant, although he said he was suffering from pneumonia. After just a couple of minutes, however, he said his wife had just walked in and he couldn’t talk.
The next day he messaged me and asked whether we could meet. I said “yes” and we agreed to meet at either the Fairmont Hotel or Hy’s. He said he would let me know. It ended up being Hy’s.
When I walked in Fred was standing beside the bar. He looked remarkably the same from the last time I had seen him, although a little dissheveled. There were no apparent signs of his having had pneumonia.
He asked the server if we could have a private table somewhere and she told us that we could go upstairs to the dining room, which was empty. We sat down and I placed my iPhone on the table, as did Fred. I told him that I wanted to record our conversation so that everything he might say would be on the record. He agreed and also said he was going to record it himself – presumably to make sure that I wouldn’t alter anything.
In every instance where he refers to the name of his company or supposed group of companies, I’ve omitted the actual name – even though in the rest of my story I refer to his group of companies as the Xanadu group. In a couple of instances he referred to real people during our conversation, but since they are not mentioned anywhere else in this story and play no part in the story I’ve told, I decided to retain their real names.
I want to explain what follows is not easy reading. Fred Devlin clearly suffers from a psychotic delusion and my intent is not to make light of his illness. There are many people who suffer from various psychoses and many of them are capable of committing great harm to others if their psychoses aren’t treated – or, even if they are treated, the treatments fail.
What makes Fred Devlin’s story so unusual, however, is the harm he was able to inflict and is apparently still inflicting on so many others by his believing the story he had somehow developed to explain his life. Even as I was talking to him I could see that his calm, measured tone could seem quite convincing to most people with whom he would connect. I deliberately went after him as hard as I could though, to see whether I could break his composure by asking him questions quickly and not giving him the opportunity to start rambling on about his group of companies, his charitable endeavours and, most important, his vast wealth.
By the end of our conversation he was shaking and kept saying the was tired. I honestly felt sorry for him, but I wanted to get him on the record contradicting his story fully in so many ways so that no one reading this would doubt for a moment that Fred Devlin is fully psychotic and can be quite dangerous when he tries to envelop trusting individuals in his web of deceit, regardless whether he himself is unaware just how deceitful he really is.
One more note: As is the case with most conversations, speakers often interrupt one another, thoughts don’t get fully expressed – and even though the transcription program I used is quite accurate, a lot of what Fred Devlin said was indecipherable. I’ve tried to do justice to what was said, but I’ve left out a lot of the pauses and words that made no sense.
Here is how the conversation went:
Devlin: Now do you want me to just talk or you ask questions – or do you have questions?
Me: Well, of course I have questions, but if you want to start off by saying something, go right ahead.
Devlin: It’s gonna take a series of interviews to cover my life, but I’m gonna give you everything. I’m gonna give you evidence. I will show you that everything I always say is true. I started my life at… started in Israel when I was 10. My father went to teach at the Weizmann Institute. We went through Europe and then to Israel. We were in Greece on the way to Israel, and there was the (raid on Entebbe). Okay. We got to Israel, ran into by chance Benjamin Netanyahu, who had lost his brother. And we gave our condolences and that was the first meeting I had with Benjamin Netanyahu. We lived there. I went to school there. I was infatuated with the soldiers and the guns and the bullets and… a soldier, a friend – Michael Perl…. I don’t know if you know Michael Perl – but his brother gave us all these empty shells. I went to a sporting goods store, bought a gun, a starting pistol. I converted it into a gun and I guarded my campus in Israel, and that was what I was meant to be. So my life is about guarding Israel, the … Foundation worldwide, which is just a name, it’s actually a numbered company based outta Luxembourg and the … group of companies Worldwide Holdings are also a numbered company under … Investment Corporation, which you can look up at the Manitoba Companies office on Broadway.
Me: Let, let me stop you there. First of all, I’m not so sure about the whole story about meeting Netanyahu, but regardless, the … group of companies has no presence on the internet. I don’t believe there is any such thing as the ….Group of Companies. Do you have any proof that there is something (by that name)?
Devlin: Of course, I will have lawyers write to you.
Me: Never mind lawyers. What can you show in terms of documentation?
Devlin: I can show you the websites. It’s just a name, okay.
Me: And what are the companies in the … group of companies?
Devlin: There’s 3,360.
Me: Okay. Can you name any of them?
Devlin: Of course, but I’m not going to name…
Me: Name one.
Devlin: I’m not gonna name one. It’s private.
Me: You’re not gonna name one?
Devlin: Not today, no.
Me: Why?
Devlin: ’cause they are secret. They’re secret companies. Okay. I want no one knowing my business. I haven’t been in a publication since May, 1990.
Me: How many companies now is it (in the group of companies)?
Devlin: 3,300… 3,306.
Me: When I spoke to you in 2021, it was 300.
Devlin: I was being honest. Okay.
Me: Alright. So, the … group of companies has 3,300 companies. You won’t name one. You won’t provide any proof that there is (even one company).
Devlin: I’ll provide you with okay. But not today.
Me: Alright. And it’s headquartered in Luxembourg, correct?
Devlin: Okay
Me: And David Simkin is what?
Devlin: My CEO.
Me: Okay. Does he exist?
Devlin: Of course.
Me: Where does he live?
Devlin: Luxembourg. Okay. But he traveled.
Me: No one has ever been able to establish that there is anyone by that name.
Devlin: Because he’s Mossad.
Me: Because he’s Mossad?
Devlin: Correct. And that’s not his real name.
Me: Oh, it’s not his real name. Okay. Alright, let’s go on.
I am sort of curious to know about your business career. I did read that you were in real estate and then you became the executive director of the Winnipeg Airport ….
Devlin: No, I first started Winnport. I founded Winnport.
Me: You founded Winnport?
Devlin; Yes. Yeah. Here, I’ll show you.
Me: Okay. And what year was that?
Devlin: About 1992 to 1994.
Me: And you have some proof for that.
Devlin: Of course.
Me: Of course. (According to Wikipedia, Winnport was established in 1998 by Lynn Bishop. Here is what Wikipedia has to say about Winnport: “Winnport Logistics, a Winnipeg-based air cargo consortium, was established in 1998. The company launched Canada’s first scheduled widebody cargo operations during that year, aiming to connect Winnipeg to Asian markets, before eventually ceasing operations in 2002”.)
Me: And then you became executive director of the Airport Area Business Improvement Zone?
Devlin: No. Of the Winnipeg Development Corporation biz, not the Winnipeg…. Never with the Airport Area Business Improvement Zone. (I found that answer particularly strange because the 1998 article I referenced earlier specifically stated that Devlin had been the recently appointed executive director of the Airport Area Business Improvement Zone. Why he would he have chosen to talk about Winnport, with which he may have had some involvement, but certainly not in the years he said he was involved, and not the Airport Area Business Improvement Zone – raises new questions – both about Devlin’s resumé – and his memory.)
Devlin: Yes, I was. And I had it (Winnport) spun off. I’ll tell you the story, but easy for you to look at. (And at that point he pulled out what I immediately recognized as his album of photos that he had first shown me in 2021.)
Me: Are you gonna show me more pictures?
Devlin: Yep. I’m show you.
Me: Okay. I don’t care. I’ve seen your pictures Fred, and you know what? I don’t care about your pictures.
Devlin: You know what, then don’t be rude…
Me; Alright. When was that? You say that was 1992.
Devlin: It’s ’94 or so.
Me: Okay. Alright. Look, I don’t doubt that you had some sort of business career. I wrote that (in my original story that I posted to the internet in February 2026), so the question is: ‘What happened?’ (At that point a waiter came over with our soups and the conversation paused.)
Me: Okay, let’s go on. So how long were you with Winnport then?
Devlin: About a year, and then that was…there’s a story behind that. There’s a lot more to the story. Alright, so can I tell you the story?
Me: The Winnport story? Yeah. Tell me the story.
Devlin: When I was running my company, … Investment Corporation, which I founded in 1987 and still operating, which owns all the … Foundation worldwide. In a … group of companies. It’s in the Companies office. It’s current and operating.
Me: Go on.
Devlin: In May of 1990 I was featured in Manitoba Business Magazine.
Me: Yes, I have that article.
(At this point the man I’ve been calling Devlin launched into a very descriptive, but often incoherent account of part of his earlier business career. As I’ve noted previously, I have no doubt that Devlin was very bright – and successful – until something happened. So, when he weaves names of real people into his stories, there might be more than a semblance of the truth in what he’s saying. The problem is he seems to get key dates wrong – as when he talks about Winnport – and when he claims to have been the person to have started that company.
Still, it’s somewhat sad to think how much potential he had – as he explains in the following account. If only he had never veered completely off the rails and started insinuating himself into so many people’s lives, causing so mach damage along the way.)
Devlin: Yeah, (but) you don’t have the full magazine, which has much more information. (It) talks about me becoming an up and coming… and Izzy Asper saw the article and summoned me…it was a billionaire summoning a millionaire and it was the only time in my life I was intimidated a little bit. We became partners, friends, mentor, and he financed me for the acquisition of land where Centerport is. I still control land at the airport and I started Winnport. I founded it. It was my business plan, my concept, although it was talked about by others. I mapped it out on a plane coming back from Amsterdam, Holland ’cause I mapped out a logistics plan that is now Centerport. So, I was sitting on a Saturday going through the career section at our place on Wellington. I saw a career commercial development officer wanted by the Winnipeg International Airport and Izzy Asper and I had already bought the land, so I figured I’d go as an insider. I got the job the next day ’cause I had a presentation, which included every element of what they were trying to do. I worked technically for someone named Warren Thompson, but I really worked with Lynn Bishop, who was the general manager of the airport and eventually president of the Bombers. I talked to Lynn yesterday, I believe so. I still keep in touch with a great guy. Okay. I realized that I had a conflict of interest owning land and being the insider in the airport. So I realized I had to spin off a company. So we spun off Winnport, which I named. I actually spelled it W-I-N-P-O-R-T. Lynn Bishop on a flight back from, I believe, Chattanooga, Tennessee. No, uh, Huntsville, Alabama, where we were looking at CargoX airplanes from Luxembourg, which I own now in control. Go look it up and you’ll see nothing about me. Every company I own does not come back to me. My business is silent.
(A few days after meeting Fred Devlin, I did manage to get a hold of Lynn Bishop, who was the original founder of Winnport – in 1998, when Fred would have been around 32. Lynn told me that Fred Devlin did work for the company for a very brief time, but they had to let him go because his behaviour was so erratic. That jives with my thinking that it was sometime when Fred was in his early thirties that he became quite delusional.)
Me: Why? Why is that?
Devlin: Two reasons. I don’t want anyone knowing my business. If I’m to buy land or buy something, the price goes up if they comes from …. So we use shell companies to buy and make offers with legal. That’s one. The other is reputation. God forbid Air Canada has a crash. And it connects to …, then my reputation is real.
Me: So Air Canada is one of the companies you own?
Devlin: I’m not gonna say.
Me: you’re not gonna say?
Devlin: I will tell you next meeting. I will give you a paper with some holdings. I know Michael Rousseau very well, who was vice president of Finance for Air Canada.(He was actually its CEO until recently. when he resigned over his not knowing how to speak French.) I deal with him. He’s been fired. We’re bringing in a new CEO and president. I own part of Boeing, okay.
Me: Let’s move on. What did you do after Winnport?
Devlin: After I left Winnport, I was not happy. I sold it to Cargojet or behind the scenes, and we have shares in Cargo, which is the largest Canadian cargo companies, so Winnport became very successful domestically. I’m doing the project again to introduce runs by CargoX currently, which will be Winnport again and Cargojet. (As has been noted, Winnport ceased operations after 2002.) And I will make Winnport as I expected it to be. Then I left Winnport and I became executive director…(of what, Devlin didn’t say). Didn’t take a salary or I gave my salary to charity to stay involved with the airport area and Winnport.
Me. And what did you do then?
Devlin: I did nothing. I was executive director of the Airport Area Business Development Corporation. (The chronology is so confusing. Devlin just claimed he left Winnport and became executive director of the Airport Area Business Development Corporation, but Winnport wasn’t established until 1998 and that 1998 magazine article said Devlin was the recently appointed executive director of the Airport Area Business Development Corporation, which would have preceded his becoming involved with Winnport but, In the final analysis, it doesn’t really matter what the sequence of his various positions he hleld was – if he, in fact, actually held the positions he said he held. Still, it seems evident that Fred had an upward career trajectory until he developed his psychosis. I haven’t been able to establish what he was doing when he apparently developed that psychosis when he must have been in his thirties.)
Me: And you didn’t take a salary?
Devlin: I took a salary, but I gave it to charity.
Me: Is there a record – of your having been with Winnport?
Devlin: I can get that for you.
Me: Okay. So you were already in your thirties by then, I’m guessing?
Devlin: Yeah.
Me: Okay. Alright. I wanna move forward though because as you know, I’ve been writing about you. I wanna talk about your relationship….
Devlin: You are slandering me.
Me: I want to talk about your relationship with Jonathan Soloway.
Devlin: Alright.
Me: I have copies of written agreements between you and Jonathan Soloway.
Devlin: You don’t have everything.
Me: I have signed agreements between you and Jonathan Soloway.
Devlin: No, I never signed an agreement with him.
Me: I have your signature on those documents.
Devlin: Never signed it.
Me: Are they forged?
Devlin: Were they forged? I don’t know what Jonathan did with them.
Me: Okay, so you are saying that those agreements are invalid.
Devlin: They’re invalid and I can tell you what I offered Jonathan and I helped save his life, and was the only person who reached out to him after I hadn’t talked to him in 45 years. He flew to Winnipeg to meet with me at 529 (Wellington). I befriended him. I tried my best to help him. He had lost his life savings in a bitcoin scam or some type of scam on the internet. He had nothing. He had no car. He was living at his brother’s place. He lost his marriage. And the custody of his daughter, I believe, and his life was in ruins and I was the only one to step up to offer to help him. I offered him, I’m setting up a real estate investment trust in the fall with Nikki Bello (who, I was able to learn, is a Winnipeg Chartered Professional Accountant), if she’s interested still. And probably Lauren. (I have no idea who that is and I didn’t ask Devlin who Lauren is.)
Me: Did you tell him to stop making payments on all his debts?
Devlin: No.
Me: You deny that?
Devlin: No, I said to him, “Don’t pay if they’re not gonna come after you.”
Me: And you didn’t offer him a salary of $250,000 a year?
Devlin: I, no…. being paid on the first 50. (In talking to Jonathan, he explained that 50 would have meant 50% of the Real Estate Investment Trust he was supposed to be setting up with Devlin.) Would you like to know what it is?
Me: Sure.
Devlin: I offered him 49% of the company outta my goodwill of the shares. Jonathan was confused. He thought he was getting a job. I said, “No, you’re getting a partnership.”
Me: So if I were to show you the agreement (promising to pay Jonathan $250,000 a year) with your signature on it, would you say that is a false document?
Devlin: I’d have to see it.
Me: Well, I can open it up for you if you want.
Devlin: Jonathan turned on me because I was in the hospital. I disappeared for five weeks with a brain injury and I couldn’t help him pay off his debt. I talked to his creditors. I got his debt reduced. I did my very best for Jonathan.
Me: Alright, so you say that you didn’t offer him a salary of $250,000.
Devlin: Yes, I did.
Me: You did?
Devlin: But once we were operational and there was cash flow from the REIT. I wouldn’t take a salary. Nikki wouldn’t take a salary. She took shares and then I promised him a $250,000 salary as long as we had cash flow.
Me: But these agreements are quite recently signed and don’t say anything about having to wait for a cash flow before he would get paid.
Devlin: Nothing happened. There was no money there.
Me: It’s all part of a pattern Fred of you stringing people along with promises of a big payday and then, when they start asking “Where’s the money?”, you say there is no money there – right?
Devlin: That’s your belief. It’s not true.
Me: Have you ever put up money for a project?
Devlin: Many times. All the time.
Me: And can you substantiate that?
Devlin: Yeah. I can show you an airline project where I’m doing in Nigeria.
Me: Did you not offer Rick financial help with his publication?
Devlin: Never. No. Okay. I offered him a million dollars potentially to buy him out from 420 magazine and to have him run as CEO or in some position once we started 420 was a deadline (again – totally incoherent). I’m still willing to meet my commitments to him, but he slandered me and set up a group of people because he’s mentally ill. Has Asperger’s, I believe, or autism and rage management and A-D-H-D-.I disappeared in the hospital the next day without being able to tell anyone. I was in for five weeks. I couldn’t communicate. I had blinding brain injury, headaches, and vertigo. Couldn’t use my phone.
Me: How many times have you been in the hospital… committed for psychiatric reasons?
Devlin: Never. Never.
Me: Did you send a cease and desist letter to a psychiatrist?
Devlin: No.
Me: You didn’t’?
Devlin: Not that I recall.
Me: You didn’t have Bob Anderson send a cease and desist letter?
Devlin: Yes, I did.
Me: To a psychiatrist?
Devlin: Yes, I did. Okay.
Me; Why was that?
Devlin: I’m not gonna talk about it right now. Okay. Next time.
Me: So you were in the hospital for psychiatric visits.
Devlin: No. Okay.
Me: Did you meet a fellow named Jack in a psychiatric wing of a hospital?
Devlin: I went in to be undercover and I met him and he was my roommate.
Me: Did you tell him that you owned the hospital?
Devlin: Yes.
Me: Why?
Devlin: Because I do.
Me: That would be the Health Sciences Center?
Devlin: No, the Victoria Hospital.
Me: You own Victoria Hospital?
Devlin: . Through Internet means I control the hospital.
Me: Okay. This is all very interesting. You are actually confirming everything that has been told to me. Okay. I wanna talk about Charlie.
Did you offer to finance a charitable foundation for him in the Democratic Republic of the Congo?
Devlin: No.
Me: You never did?
Devlin: No.
Me: Even though he’s got letters, texts, and emails to show that you did.
Devlin: If he says so I’ve got the texts, I’ll have to read ’em.
Me: Have you been threatening Charlie?
Devlin: No.
Me: Have you not been telling him that you’re gonna ruin his life?
Devlin: Legally? Yes. For slandering me on Facebook, I’m gonna sue him to the grave.
Me: Did you tell him that you would take his farm? (I asked Charlie whether he ever had a farm. He said he didn’t.)
Devlin: Yeah.
Me: His pharmacy? (Again, Charlie was bewildered over the suggestion he had either a farm or a pharmacy which, he says, he’s never had. He said he did own a piece of land in his community – which he sold to finance the charitable foundation Devlin told him his …group of companies would finance.)
Devlin: I paid for his books, his computers, everything and the value that he has. And I said I would take it all.
Me: Why?
Devlin: Because he slandered me on Facebook after I put him through school partially, and I was a mentor to him. I spent hundreds of hours, which are documented. You can see. I’ll be happy to turn over all my emails and texts to you. Okay. He has not told you the truth.
Me; Alright, there are a whole slew of other people who I’ve talked to who told me that you would make promises to them. One of them was Dan Winthrop.
Devlin: I made no promises to Dan. I’m helping with a project with Israeli aircraft. Okay.
Me: And this has been going on for over 18 years?
Devlin: Correct.
Me: And you had a fellow in Las Vegas – Avi… I can’t remember his last name – who was going to facilitate your bringing over jets from Israel and convert them to some sort of use? Did Avi not try and set up a meeting between you and various officials, including Prime Minister Netanyahu?
Devlin: Our deal was once I hired him and pay him a million dollars a year. Plus 3.33% of the funds he raises. He’s earning about 120, I believe, as the director of…(Avi actually works in an area that is too sensitive to Israel’s security to reveal.)
He was not happy. He expressed an interest in working for me, so I did my best to get him a position. I became ill and was unable to fulfill it. But I am planning on fulfilling it.
Me: Okay, one more story of promises unfulfilled.
Devlin: Not my fault. I was in the hospital, very ill.
Me: Alright. I wanna get back to Jonathan Solaway though, because since you deny that you have had any written agreements with him, I wanna show you the written agreements and then have you comment on them.
Devlin: I don’t want to do this. Getting tired. I’m sick. I do next session.
Me: You’re getting tired now?
Devlin: Yes. Very tired. But I will talk to you next interview about that.
At that point someone walked by our table and Devlin turned to him, saying: “Hi, how are you?… I’m good. How are you?… Good… Oh, you’re the delivery boy today. You do everything. A jack of all trades. . Things are going well. Yeah. How about you? I haven’t seen you in a while. Been away and it’s been a while… I’ve been here. You been here? Was able to sneak in. You enjoy it? I am. Yeah. It’s good. Yeah. Good. Brock Wright. Brock Wright. Can you get me his number? ’cause we’re fixing the healthcare system.” (From 2000 to 2017, Brock Wright served as Vice President and Chief Medical Officer for what was then the new Winnipeg Regional Health Authority and, for five years during that period, also served as the Chief Operating Officer at Health Sciences Centre.) The person Devlin was talking to said : “I will try to, yeah. . Next time I see him, I’ll, I’ll grab it for you.” (I chose to include this little snippet to illustrate how good Fred could be at posing as someone important – and turning on the charm.)
I resumed my questioning: “Okay. Alright. If you don’t want to see the material that I have…
Devlin: Not, not this time, I’m too tired to look it up.
Me: Okay. Well let’s go back to asking some some more questions about other people who I’ve spoken to. One of them was a lawyer by the name of Bob Anderson.
Devlin: He’s not a lawyer. He lost his license for, well he was a lawyer in Virginia. Go look him up on the internet. I hired him after he was slandered and I tried to take down the information on him. We’ve been friends for 20 years. They came to me and approached me in Bolivia to buy banks and he came to the Forks area hotel. We became best friends and he did free work for me for many years for my foundation. And that’s it.
Me: How did you get in touch with Rick? Was it through Jack?
Devlin: Okay.
Me: And you met Jack in a psychiatric ward?
Devlin: I met him in the hospital – okay.
Me: Well, he says it was a psychiatric ward.
Devlin: Whatever he says. I won’t argue.
Me: So you deny that you were a patient in the psychiatric ward.
Devlin: No, I was not a patient.
Me: No, you were checking out the system ’cause you were the owner of the hospital. Do you know how ridiculous that sounds?
Devlin: You can do what you want with it. I’m telling you.
Me: You say you own Victoria Hospital?
Devlin: No, through options on the hospital with the Manitoba government.
Me: Oh really? Okay. You think that if I were to print this conversation now that this is going to make you look somehow as a bonafide, legitimate businessman?
Devlin: Not the way you are putting it. I’m just going to answer.
Me: I’m just asking you the questions and you’re giving me the answers… and I’m doing it on the record.
Devlin: I’m giving you a courtesy before I sue your ass for a hundred million dollars.
Me: Is that right? On what grounds?
Devlin: Defamation. You didn’t approach me to ever get my side of the story. You went with a group of people – Rick, who’s a crazy man, and he stirred up all these people, dug up every single person I knew because I was too open with them and slandered me and made up stories and approached you. I don’t know the total chain of events, but I will shortly.
Me: Okay, but you say that even though there are documents with your signature on them, especially the ones signed between you and and Jonathan Soloway, they’re not legitimate documents. Is that what you’re saying?
Devlin: They’re not. Jonathan knew very well that he was getting no salary till it was operational.
Me: Even though your signature’s on your document and promises…
Devlin: We tried to put together a document. It was null and void. Jonathan knew that – when was it made null and void immediately, within 10 minutes of it being signed.
Me: Why was that?
Devlin: Because Jonathan put in fake clauses saying that I owe him $250,000. But the other clause says he’s not gonna get paid till there’s generation of revenue. I have witnesses. Nikki Bello.
Me: Is that in the document?
Devlln: I believe so. I’d have to review it if.
Me: Jonathan is in big (financial) trouble and you deny that you told him to stop making payments on his debt?
Devlin: I said to him, these were my words: ‘If they’re not gonna come after you, it’s better to conserve your cash and not pay creditors.” I’ve had much experience with people who have worked for me with creditors.
Me: Did you not tell him that you were gonna take care of his debts?
Devlin: I did.
Me: You did?
Devlin: Yeah.
Me: Did you?
Devlin: Not yet. I got ill and I was unable to work, and now I’m happy to take care of his debts, but after he slandered me, I’m no longer willing to do it.
Me: Isn’t that a breach of contract then?
Devlin: There was no contract. It was friendly. It was a friendly promise to do my best to help him. Okay?
Me: But when I say there is a contract with your signature on it…
Devlin: I, I’d have to see it.
Me; Well, if I showed it to you, is it gonna make any difference?
Devlin: Could. It depends on what it says. I have to go through my documents and I’ll tell you next interview. (At that point Devlin said something incomprehensible, but then suggested that Jonathan doesn’t have a case that any lawyer would take on, saying “No one will take the case.”)
Me: There was a lawyer who was quite willing to take the case, but the problem is – you’re penniless – so there’s no point in suing you.
Let’s talk about your finances. How much money do you have?
Devlin: Look, that’s not your business, but I have a lot of money.
Me: Okay, you don’t think there’s a lawyer who’s quite willing to take the case (of a lawsuit against Devlin)?
Devlin: Go for it.
Me: But I asked the lawyer: Can Fred’s parents and his wife be included in a lawsuit?
Devlin: Yeah. And what did they say?
Me: He said, “no,” unless we can prove that somehow they were materially involved in all your affairs. By the way, how do you pay for all these meals at Hy’s and at the Fairmont?
Devlin: With my Interac card. Why?
Me: I’m just wondering who is supporting you? Is it your parents?
Devlin: Nobody supports me. No, no.
Me: It’s income from where? From the … group of companies, right?
Devlin: Correct.
Me: The …group of companies? And David Simkin is the CEO, right?
Devlin: Okay. I get my money from him.
Me: Would I ever be able to talk to David Simkin?
Devlin: No.
Me: Because he’s Mossad, correct?
Devlin: Right. And that’s not his real name. Ari Duran, my chief of Global Intelligence and Security based in Tel Aviv, who’s worked for me for over 20 years – he’s also Mossad. Everyone who works in my senior executives are Mossad or IDF.
Me: Are you accompanied by Mossad agents?
Devlin: Most of the time. I won’t answer that.
Me: Are you ever accompanied by Mossad agents?
Devlin: Correct.
Me: What does that mean?
Devlin: They guard my family in Winnipeg, in Cleveland – for 20 years.
Me: Do you live at …? (At that point I recited the address where Fred and his wife are presumed to live)?
Devlin: That’s our safe house. We have 1909 Wellington Crescent, and we’re moving to Number One Wellington in September.
Me: Did you live at 277 Wellington Crescent ever?
Devlin: Yes.
Me: All right. Who paid for the apartment?
Devlin: I did.
Me: You did? You paid how?
Devlin: My company paid for it.
Me: Okay. To be accurate, your house is owned by someone else entirely, with a mortgage on it, right?
Devlin: We have the option to buy it. His name is Michael (name omitted). Yeah. And his number is 3 3 3 3 3 3. (Of all the baffling things Devlin said during this conversation, that number was the weirdest. I have no idea what he meant by saying that.)
Me: We did a search for the title on that house. It’s only valued at $439,000. But you say that’s a safe house?
Devlin: Correct.
Me: So, where is your primary residence?
Devlin: I won’t answer that – for security reasons.
Me: Oh, for security reasons. Do you know how ludicrous this all sounds?
Devlin: I don’t care. I’m sure it does, but it’s true.
Me: And do you think that if you sued me for defamation and I were to have this played in court that you wouldn’t be laughed out of court? Fred, are you under psychiatric care right now?
Devlin: No.
Me; Have you ever been under psychiatric care?
Devlin: I was once under psychiatric care, but for a fact that I have a sleep disorder and I couldn’t sleep, and they had to give me medication through psychiatry to make me sleep. I don’t sleep 24 hours a day. I have a rare sleep disorder. I never sleep and without the aid of medication, so that was the only time.
Me: Okay. So when I approached your mother years ago after I had met you and asked her: “What’s the story with …?” And she said, “… is not well, please go easy on him.,” what do you think she meant, Fred?
Devlin: I wasn’t well physically and she wanted you to leave me alone.
Me: Well, was it because you weren’t well physically or weren’t well psychologically?
Devlin: No, it was physically.
Me: Have you ever been hospitalized for a psychiatric disorder?
Devlin: I’m not gonna answer that. Alright. My health is out of court.
Me: Well, you just said that you don’t have any psychiatric disorder.
Devlin: I have letters from the Cleveland Clinic. Each year for my corporation, I have to get a healthcare letter. I have no… besides pneumonia. Now I’m in perfect physical and mental health. Okay. And I have letters from doctors in Cleveland and in Winnipeg. Okay.
Me: Who do you have working for you in Winnipeg?
Devlin: I won’t answer that…many people.
Me: Is (name omitted) one of the people?
Devlin: She did some free work for me, but I’m planning on hiring her as CEO of … Foundation, Winnipeg office.
Me: Did you ever pay her anything?
Devlin: Not yet.
Me: Why not?
Devlin: ’cause we had no agreements in place for me to pay her. She was volunteering for the foundation.
Me: Or is it not the case that you have no money and it’s all a delusion, Fred?
Devlin: Okay, Bernie, whatever you say, keep up with slander. You know what? This interview is over if you continue this line.
Me: Well, since you denied that you’ve had any agreement with Jonathan Soloway, that you had any agreement with Rick, that you had a plan to to bring jets from Israel over to Canada to convert them for some sort of…
Devlin: We are, uh, proceeding with that project.
Me: And this project has been ongoing for almost 18 or 20 years?
Devlin: No, no, three years. Just three years with Dan. Three or four years with Dan – who I offered a company. I offered him, I sent, he went to Israel on his own money. Yeah. And he didn’t expect anything to be offered. I wasn’t gonna go to Israel because I thought his ideas that he had for 20 years may not be solid. He went on his own way to meet Gli, who’s a tremendous person, director of … I believe I have her name.
Me: There’s a whole slew of people you’ve contacted over the years. According to what I was told by (name omitted), you’ve recently contacted the head of the Winnipeg, Airport Authority and the head of Centerport.
Devlin: Not recently, although I phoned Carly (Edmundson, the President and CEO of CentrePort) yesterday.
Me: The CEO of CenterPort? Okay, what was the nature of your communication with her and the head of the Winnipeg Airport Authority (Nick Hays)? You have plans, right? You have projects. What kind of project is it you want to develop?
Devlin: Next interview. I’ll be happy. Okay.
Me: They don’t know about your past history. Because when I told Carly in an email that you’re totally delusional, she responded that came as a surprise, but she said all that she did is introduce you to some other people.
That’s your style, isn’t it Fred? You network with people. You find people, you use them to contact other people.
Devlin: Correct.
Me: So, you admit that’s what you do?
Devlin: Oh, that works. Yes. Yeah.
Me: Okay, so you network with people and then you find what their particular area of expertise is. You have some background in aviation, so that gives you…
Devlin: And real estate… and financial markets.
Me: Yeah. Okay. So that gives you the semblance of having some experience.
Devlin: I have deep experience.
Me: Then you lull people into thinking that you’re actually credible – right?
Devlin: Oh my god, that’s slander.
Me: But isn’t that how you operate?
Devlin: No, I don’t.
Me: No? What do you do?
Devlin: Not at all.
Me: What do you do then? How do you network with people?
Devlin: I try to find people I can help and do Tikkun Olam with, at every level. Tikkun Global. Yeah. And every person I touch, I try to help.
Me: Okay. What charitable foundations have you ever financed?
Devlin: In Africa, we financed USAID, Save the Children, World Vision… many.
Me: And you have proof for all that? That’s what Charlie told me that you told him when you suckered him into believing you.
Devlin: I suckered him? Yes. What a joke.
Me: Do you know the guy is suicidal? Do you know that I sent him money?
Devlin: How much money did you send him?
Me: I sent him 600 Canadian dollars,but he still owes a lot more. (I later sent Charlie another $800. I still keep in regular touch with him. Charlie still finds it difficult to believe that Fred Devlin was a total fraudster.)
Devlin: Good for you. I paid him more.
Me: You haven’t paid him a cent.
Devlin: I put him through school for $650.
Me: Oh you did, did you?
Devlin: Yes.
Me: And what kind of school was that?
Devlin: His certificate’s in business. (After I had this conversation with Fred I contacted Charlie to ask him whether Fred had ever given him money for anything. He sent me a screenshot of a text from Fred that was sent in 2023 in which Fred asks the director of a school Charlie was attending to give him an extension on paying his tuition, saying that he will “receive the necessary funds to pay for his school after I return from Israel on my peace mission in early December. I need to be in Winnipeg to direct these funds to him.” Of course, there never way any payment of any sort, according to Charlie.)
Me: But you’ve been sending him threatening messages.
Devlin: Because he threatened me on Facebook.
Me: What did he say on Facebook?
Devlin: He started writing all about me and saying I was a liar and I was… he slandered me. (I’m sure that Devlin was referring to the article I had posted on my website in February which contained that very detailed email outlining the litany of Fred’s broken promises. Somehow he had it confused with Facebook.)
Me: But that wasn’t Charlie who wrote that email.
Devlin: Who wrote it?
Me: You don’t know?
Devlin: I’ll find out.
Me: You think Charlie was capable of having written that email? (Charlie’s native tongue is French, and although his English is quite good, it didn’t take me long to realize that he couldn’t have written that January 16 email. I quicky deduced that it was Rick, who is capable of writing very well.)
Devlin: No. Was it Rick?
Me: That’s right. So why don’t you sue Rick?
Devlin: I am.
Me: You are? Where?
Devlin: I have a lawyer in Florida. I have lawyers in Toronto who can operate in Florida.
(And then I asked him about a lawyer in Winnipeg who’s his cousin – and is the lawyer who threatened to sue me for defamation. I asked Fred whether that person has ever acted for him? He said he has – for many of his over 3,300 companies.)
Me: Can you name one of those companies?
Devlin: Yes. Worldview Capital.
Me: Which is what?
Devlin: Which is what the airport is. Worldview Capital owns the world’s only financial model that works, generates between 250003300000.0% for annum. Yeah. It’s worth $1.15 trillion. I’m going to be making a deal with their candidate. (Again, totally incoherent)
Me: And (Fred’s cousin) acted for you in this, correct?
Devlin: Right.
Me: So if I ask (cousin’s name – omitted here) that, do you think he’ll substantiate that?
Devlin: He’ll tell you what I asked him. He won’t talk to you, he’s not talking to you.
Me: Oh, is that right?
Devlin: I’ve done this on my own – against my lawyer’s advice.
Me: Does (your cousin) know that you’re here, that you’re meeting with me?
Devlin: No.
Me: What would he say if he knew you were meeting with me?
Devline: He’d be pissed off.
Me: Yeah. What about your wife? Does she know? Pissed off, right? She knows that I’ve contacted you though – right?
Devlin: Yeah.
Me: Has she taken the phone away from you when various people have called you?
Devlin: No. No.
Me: Okay. What’s your wife’s role in all this?
Devlin: My wife has no role in all this. She facilitates, she works for another company.
Me: Has she sat in on meetings?
Devlin: No, she did not.
Me: Well, according to someone who asked me not to name them, she has.
Devlin: I’d have to look it up.
Me: Yeah, please do. I’ve spoken to…(and then, Devlin interrupted me.)
Devlin: I don’t care who you’ve spoken to, you’re not getting good information.
Me: Okay, do you want the real truth? I’d love for this to go to court. I’d want it to go to court because maybe that could put a stop to you. That’s why, when people ask me why I got so involved in this story, I say to them it’s because I’m trying to stop you from hurting other people – because you’ve hurt a lot of people, okay?
Devlin: If you say so and you’re not aware of what you’re doing…You make an excellent argument based on the fallacy of your assumptions, Bernie.
Me: I don’t know where to take this. You’re substantiating everything that’s been told me about you so far.
Devlin: I need more interviews. I’ll be happy to talk to you about everything but this, this should not go into an article.
Me: Would you be surprised to know that I’m writing a story about you?
Devlin: No, but we’re gonna co-publish that story with the truth.
Me: Oh, really? Do you think I’m gonna give you final edit on the story?
Devlin: No, I don’t expect it.
Me: I’m not even gonna let you see it. I’m gonna let the people who are mentioned in it see it before I try to publish it.
Devlin: Try it and see what happens to you.
Me: Well, I’ve already got one publisher who’s quite interested.
Devlin: I’m sure It’s a very interesting story.
Me: It’s been fascinating trying to flesh it out.
Devlin: How about if it’s true, Bernie? Did you ever contemplate everything I told you is true? Has that ever gone through your mind? And then think about what you’ve done.
Me: You mean the story that you’re telling? Is the story true in whole or in part?
Devlin: No, it’s true in whole.
Me: Every part of the story, every single part? Every part about you owning over 3,300 companies? Are you a trillionaire or a billionaire?
Devlin: I’m a trillionaire.
Me: You’re a trillionaire.
Devlin: Over and over.
Me: Are you richer than Elon Musk?
Devlin: Much richer than Elon.
Me: Okay. Then why do you dress like this?
Devlin: Like what?
Me: I mean you’re presentable, but it’s not what I’d expect from a trillionaire.
Devlin: I care about my parents. I…
Me: If you’re a trillionaire, where are the bodyguards? I can’t imagine a trillionaire not being surrounded by bodyguards
Devlin: They’re here. You don’t see them, but they’re here.
Me: I don’t see them. Are they Mossad?
Devlin: Yeah, they’re Mossad. We don’t want to have (his wife), for instance worry about bodyguards for my family. So it’s invisible. I don’t even know where they are.
Me: You don’t even know where they are?
Devlin: I can find out quickly by just tapping a button on my phone. That’s the truth. Okay. Now if I tell you what I’m worth, would that be helpful?
Me: Yeah, sure. Go ahead.
Devlin: $9.33 trillion.
Me: 9.33 trillion? How do you think that sounds?
Devlin: Do you think that when I have world…., but I know every up and down in stocks, commodities, currencies, commodities. I just trade. Automatically outta Luxembourg and I trade on my desk in my office and make millions of dollars.
Me: Fred, how do you think your parents would react if I were to send them a transcript of this conversation?
Devlin: They’d be very upset.
Me: Why?
Devlin: Because they don’t know everything about my business.
Me: Do they know that you have $9.33 trillion?
Devlin: No. You know, I’m very wealthy.
(I then asked Devlin about a cottage that he’s told people he owns, but I don’t want to get too specific about the name of the lake for the same reason I didn’t give Devlin’s actual address. Even though anyone who knows the real person I’ve been calling Fred Devlin in this story would recognize him from everything I’ve written about him, I highly doubt that anyone who doesn’t know his family would know whom I’ve been writing about – but if I were to reveal his actual address and where the family cottage is, it would be much easier to establish what Devlin’s real name is.)
Me: What kind of car do you drive?
Devlin: I drive a Porsche GT, three BMW convertibles. They’re not in Winnipeg right now because of the potholes. I store them in Florida and Cleveland. I have 17 cars that I collect for investments.
Me: I see. And where did you tell me you’re flying to this weekend?
Devlin: I expected I’m to fly to Toronto to meet with Irvin Shane, one of my lawyers. Then I’m flying to Cleveland to spend about a month with my family going over our legal strategy to undo everybody. And then, we’re suing, unless you convince me that you’re an honest reporter.
Me: Oh. Do you think I’m afraid of a threat of a lawsuit from you, Fred? If I were to play this in court…
Devlin: Um, you know what, Bernie…
Me: I’m surprised that you haven’t been committed to an institution.
Devlin: Um, I don’t know. I don’t know exactly the legalities of that anymore. Bernie. Bernie, be careful. Why you, you’re walking on thin ice…slandering me… try to go after my mental health.
Me: We’ll see what happens. But you go after Rick’s mental health.
Devlin: He’s self-admittedly mentally ill.
Me: No, Rick admits that he’s got some problems.
Devlin: Mm-hmm. how about anger?
Me: Yeah, he admits that.
Devlin: Why didn’t he call me when I was in the hospital to see where I am instead of gathering up all these people against me?
Me: What were you doing in the hospital?
Devlin: I had a concussion from a brain injury.
Me: And when was this?
Devlin: Uh, seven weeks ago maybe. Yeah.
Me: You were just in the hospital? You had a concussion from a brain injury?
Devlin: Correct. Do you wanna see the picture of my head?
Me: Where did you fall?
Devlin: I was in the bathroom. It was dark. We normally have lights that light up. Motion detectors. I lost my orientation. Lost my balance and fell on my head. On the bed board. (But he had just stated that he fell in the bathroom.) Yeah. Cussed myself. Knocked myself out.
Me: Alright. But even while you were in a hospital – with a brain injury, you maintained contact with various people, right?
Devlin: No. No.
Me: You didn’t phone people from the hospital?
Devlin: Not many. My phone was taken away.
Me: Who took it away?
Devlin: The doctor.
Me: Why?
Devlin: He didn’t want me making calls. He wanted me to rest.
Me: Which hospital were you in most recently?
Devlin: Victoria.
Me: And which ward were you in?
Devlin: I’m not gonna talk to you about my hospitalization ’cause you’re gonna twist it and write he’s got psychiatric problems.
Me: Isn’t it the case that were in the psychiatric ward of Victoria Hospital recently?
Devlin: I, I’m not gonna answer that. Do you have evidence that I was?
Me: I don’t, I’m just asking.
Devlin: Okay. Do I sound crazy, Bernie?
Me: Oh, you want me to answer that? Sure. You sound totally crazy, Fred. And I feel sorry for you, I feel deeply sorry for you, but what happened is just that you harm so many people.
Devlin: I never harmed anybody. No.
Me: What about Charlie?
Devlin: Never harmed.
Me: He’s suicidal.
Devlin: That’s not my fault. No, no, no.
Me: So you didn’t promise to fund his charitable foundation and he went out and spent money on his own?
Devlin: No. Never to start feeding (children). That’s not true.
Me: Poor African children, based on your promises to him?
Devlin: No, no, no. He asked me if I would send some money. ’cause he wants to feed the hungry. He brings porridge to them. Okay. To the hungry people.
Me: So did you send him money?
Devlin: No. No. Okay.
Me: Why not?
Devlin: Because I wasn’t involved at the time. I was planning on sending money…
Me: But you funded USAID and… which other charities? But you couldn’t send him a couple of thousand dollars. Why not?
Devlin: Was planning on it, but I, I got sick
Me: Did you ever pay Bob Anderson for any of the work he did?
Devlin: He never – I don’t owe him.
Me: Isn’t it true that either your father or your wife paid him?
Devlin: No.
Me: Or maybe one of your brothers?
Devlin: No.
Me: Gave him a thousand dollars. That’s what he says.
Devlin: Could be.
Me: Because he said you kept refusing to pay him.
Devlin: Bullshit. He’s in the deepest of troubles.
Me: The confidentiality agreement thats you had him prepare, you had loads of people sign confidentiality agreements that Bob Anderson prepared, didn’t you?
Devlin: He didn’t.
Me: He prepared almost 15 non-disclosure agreements for people to sign. Why would you have people sign non-disclosure agreements? ‘
Devlin: Cause I don’t want to be gossiped about.
Me: Or is it the case you didn’t want other people to know about what you were doing?
Devlin: No.
Me: Because if other people knew about the nonsense you were spouting, absolutely they would’ve cut you off at the knees.
Devlin: Absolutely not. No. That was not my motive. No.
Me: So, when you approached Jonathan Soloway because he was an old childhood friend and you told him that you could help him by setting up this real estate investment trust and you sent him contracts, what was your motivation?
Devlin: I didn’t send Jonathan contracts. No, I believe he sent them to me. (On that point Devlin was correct. I checked with Jonathan and he did say that he had the contracts prepared and sent to Devlin, adding that Devlin was incapable of producing the type of sophisticated agreements that Jonathan sent to him, but which show Devlin’s signature on them nonetheless.)
Me: Regardless, you signed the contract, but you say you didn’t sign the contract.
Devlin: Bernie. I didn’t say I didn’t sign it. I said, Jeff’s agreement that he sent me was bullshit.
Me: Okay, well, do I sound like I’m cross-examining you – because that’s what would happen if you went into court, Fred.
Devlin: I have zero problem. I’ve been in court many times.
Me: Would you be surprised to hear that different people are trying to initiate a police investigation of you now?
Devlin: There’s a police investigation of Rick…for threatening our lives, my mother’s and my life.
Me: Is that right? Where is that police investigation?
Devlin: Rick twisted it to say I threatened him. What a joke.
Me: Would you be surprised to know that there was a file opened on you by York Regional Police in Ontario and it was sent to Winnipeg ?
Devlin: No. I don’t care. No.
Me: Do you care that there might be a police investigation of you?
Devlin: Doesn’t bother me.
Me: Doesn’t bother you at at all?
Devlin: No, I’ll be happy to speak to the police… and give them evidence.
Me: I’m not sure where it’s at. I just know that there was a file opened on you.
Devlin: I’m not going nowhere, but if it does go further, I’ll be happy to talk to the police.
Me: Okay, I think this is enough, Fred.
Devlin: Um, are, are we gonna have another session? If you want,, I’d like the full truth to come out and then you can decide what to publish. I don’t feel you’ve given me justice.
April 26, 2026 This concludes my writing about Fred Devlin and his delusional cons. I was still receiving phone calls from Fred, however, asking when we could meet again – until I blocked him. And then I received a phone call from the man I’ve called Jack, who met Fred in the psych ward at Victoria Hospital. He was also totally incoherent, so I’ve blocked him too. I expect though that this story will still be ongoing. The man I’ve called Fred Devlin will likely continue to make contact with many more unsuspecting people and try to persuade them that he has a huge amount of money which he is willing to use to invest in various projects.
Further, I rather doubt any police force will proceed with an investigation. I’m sure whatever file ended up at Winnipeg Police Service has long been buried. But, since I decided to post these stories to my website – and I can reopen the story at any time, there may be more chapters to write.
If you’ve been reading these stories – either in whole or in part, you might like to know that I will compile them into one large pdf and make it accessible on this website at some point.