Features
My memories of Peretz Shul
 By KINZEY POSEN It was a late Friday afternoon at Peretz Shul in 1964 or so. A good friend of mine at the time whose Yiddish name was Moishe said, “That’s it! I’m not coming back to school on Monday, I’m out of here!” Ok, as an 11 year old, he might have said it in a slightly different way. It was the first day of school in September and we were just about to go home. “Sure you are Moishe, I’m sure you’ll be back on Monday,” I told him.
By KINZEY POSEN It was a late Friday afternoon at Peretz Shul in 1964 or so. A good friend of mine at the time whose Yiddish name was Moishe said, “That’s it! I’m not coming back to school on Monday, I’m out of here!” Ok, as an 11 year old, he might have said it in a slightly different way. It was the first day of school in September and we were just about to go home. “Sure you are Moishe, I’m sure you’ll be back on Monday,” I told him.

Kinzey’s Grade 1 Peretz School class circa 1960
(Thanks to Sandy Shefrin for helping with identifying almost everyone; comments supplied by Kinzey)
Bottom Row crosslegged, left to right: Arthur Greenspan, unidentified, Matthew Levin (a.ka. Moishe in the story)
Second Row (l-r): Paula Wolfman, Rosa Scyzgiel, Shirley Starek, Myra Miller, Faye Golubchuk, Ruthie Rosenzweig,, Honey Leah Berman, Marcie Fleisher
Third Row (l-r): Diane McKay, Lucy Baumel, Janice Goldberg, Howard Kaplan, Sandy Shefrin, Heather Wallace, Pammy Zimmer (Kinzey’s wife, Shayla Fink’s first cousin, a beautiful person (alev hasholem)
Top row (l-r): Sidney Lieber, Martin (Kinzey) Posen, Sheldon Weidman, Harvey Zahn, Harvey Koffman (my first cousin) , Sidney Shoib, Morris Glimcher, Shawn Zell, Miss (Claire) Nelko (who is now Claire Breslaw)
Come Monday, true to his word, my friend did not come back. He had entered an alternate dimension it seemed; he was finished with Peretz Shul! Unheard of! Impossible! How did he do it? Moishe’s act of sedition was a reaction to the Yiddish teacher we had been blessed with that year and he was done. All of us in the class were in awe and Moishe, no worse for wear, having left the school, went on to become a respected ambassador for Canada’s Foreign Service.
A little while back, Bernie asked me to write about Peretz Shul from a different perspective: My own, as a student. I have often wondered why this institution. for those of us who went there, lives so large in our memories. Full disclosure: My grandmother Katya Posen Z’l, nee Gurarie, was one of the founders of Peretz Shul and a lifelong member of the Muter Farein – the women’s organization that helped establish the kindergarten and supported the school.
My father, Abe Posen, attended the school as did his sister, my aunt, Goldie Zuidema Z”l. My dad often told me stories of how various teachers at Peretz used to rent one of the rooms in their house on Burrows. To put it mildly, our family was steeped in Peretzness.
My era began in 1957 when I attended nursery school and then, kindergarten. To this day, I can still smell the matches when our teacher lit the Shabbat candles on Friday and we laid out our little mats to have a nap on. Being a socialist school for the most part, you would think Shabbat would not have been part of the school experience, but I have so many great reminiscences of those two years from making little coloured paper rings several metres long, to receiving the right colour star if we behaved. I loved getting those silver and gold ones alongside my name on the wall – wonderful, warm memories.
Our principal in those early days was Chaver Herstein – an imposing man with a wonderful head of hair and a bit of a temper. We called all our teachers by either “chaver” or “chaverteh” which, in this context, translated to “comrade”. We also called them Leher or Leheren – teacher in Yiddish. Our school was located at 601 Aikins, between Inkster and Polson Avenues. How do I remember the address? Early on as soon as we could write, we always wrote the address at the top of the left corner of the sheet of paper. Now, the building is a health community centre. Once we entered Grade One, our days were separated into half day Yiddish and half day English classes.
Grade One for me – and I am sure for my classmates, was a truly seminal experience. Pushed out of the warm bosom of kindergarten, Grade One meant getting down to serious work. Reading, see Dick run, see Jane run, see Dick and Jane run, writing, singing and my own personal challenge………arithmetic. Our Yiddish teacher, Miss Nelko, was the most beautiful woman who genuinely cared about her students. We loved her and she laid the groundwork for us learning Yiddish and how to be little menches and menchettes. Many years later, Shayla and I received a call about playing a wedding for an older couple. They came over to our house one evening and as we planned the event, it occurred to me that I knew who this woman was: My beloved Miss Nelko, some 40 years later. What a reunion it was!
Our English teacher, on the other hand, had a different style of teaching that could be best described, as adversarial. I renamed her Tyrannosaurus Rex and the invisible scars are still with me. Her approach to learning arithmetic was to say the least, extremely challenging. I was one of those kids who learned math in a different way and in those days, kids such as myself fell through the cracks and we fell deeply. All I remember is after a short explanation of one plus one equals two, etc., we all had to stand up by the blackboard as T Rex wrote a problem on the board. We could not sit down unless we put our hands up and answered correctly. Guess who was often the last kid standing? Me, of course, and I eventually memorized it all so I could finally sit down.
Another time, T Rex distributed to each of us a sheet of paper for some writing project. She gave me what we called at the time “grade one” paper. It’s where the lines were printed with one bold line and two lighter lines and then another bold line. It also had big wood chips in it. I noticed that she was also giving out what we called “grade two” paper. These were all symmetrical bold lines and I wanted one. When she finished giving them out, she asked if everyone received one and me, being me, said, “I didn’t.” My six-year-old brain conveniently forgot that my desk was in the front row and I had scrunched up the grade one paper into a ball and cleverly thought she wouldn’t see it in the wood support for the desk.
As I put my hand up and told her I didn’t get one, she approached my desk in a threatening way, reached into the desk support and said, “What is this?” I was fully chastised, and T Rex bellowed, “You will only get grade one paper for the rest of the year.”
The reality was, in those days, especially in the context of a parochial school, you sometimes had people teaching who were not trained and did not have the skills to do the job. Not only that, more than a few were survivors of the Holocaust and we eventually learned that they experienced terrible horrors in the camps and ghettos.
That being said, I had several wonderful teachers, whose voices to this day still reverberate in my head and I often reflect about their ability to connect and elevate the students.
Mrs. Gold, Mrs. Brooks and Pascal Fishman were some of them. Chaver Fishman came to us from Buenos Aires and was one of our Yiddish teachers. He had a great capacity to see potential in students and encourage them. Another of our teachers, Mrs. Wallace, taught us English and her daughter was in our class for years. The family wasn’t Jewish, but Heather my classmate, spoke Yiddish like a pro. I remember one of our later Yiddish teachers, Mrs. Korman, taught us “Zol Nit Keynmol” the Warsaw Ghetto Song, and led us in a procession to St. John’s Park in the spring, while we sang that song and others.
The year at Peretz Schul was highlighted by two major events. The annual essay contest in Yiddish and English, and the graduation, which took place towards the end of June. For each of those occasions, the auditorium would be absolutely packed and very hot. As students, we often escaped outside to cool off in the lane and we could hear what was going on by the open side doors.
The cultural offerings at Peretz were in my opinion, outstanding. We were taught so many great songs, we acted in plays and we created art. Jewish holidays were celebrated with a Yiddishe taam (Yiddish flavour). Since my Hebrew name was Mordechai/Motel, I always got the part of Mordechai in the Purim play. The music component was delivered by Chaver Bronstein or Mr. Brownstone as he was known at Talmud Torah. His classes were always held in the auditorium, where he’d stand by his easel flipping the song sheets written in Yiddish and we’d follow the words as he used his pointer. Contrary to the Talmud Torah choir experience, he never gave us names or hit us. After he retired, Mrs. Udow took over and when I hoped to join the choir, she said, “Modechai, your voice is changing, perhaps another time.”
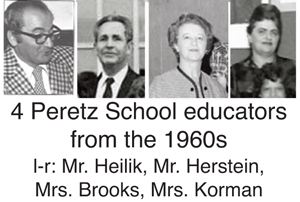
After the principal Chaver Herstein retired, Mr. Heilik who was previously at the Calgary Peretz Shul became our new principal. He was an interesting man and because of my ‘occasional’ naughty behaviour, I got to know him a little better than most students. He was an artist. His medium was oil painting and I remember, on one occasion, we were taken out of our class and brought to the auditorium. When we arrived, we saw that all four walls had been covered with his paintings. There were dozens of them. It was a full-blown exhibition of his work.
I bring this up because I became the class artist at Peretz and my teachers often ‘commissioned’ me to draw and colour huge murals in the hallway of the school. This gave me the opportunity to get out of class. Chaver Heilik would always come out of his office to check out my work. My artistry was far below his level, but he was always encouraging and interested in what I was doing.
In my day, we all graduated from Grade Seven and you had the choice of continuing in what was called Mittel Shul. These classes were held after 4 o’clock, after you finished English school. No one in my class went to Mittel Shul and we felt sorry for those who did as they arrived at four, just as we were leaving.
For me, and I’m sure others, the experience of attending Peretz Shul, wasn’t truly appreciated until after we graduated. The real world out there wasn’t as warm and friendly as it was at 601 Aikins. I do know that the school gave me the education that my Baba and other founders were hoping to achieve: an ability to speak Yiddish, a love for the language, Jewish history known as Yiddishe geshicteh and above all, an appreciation for the Jewish people and our incredibly rich journey. I also had my Peretz Shul family, the 12 or so students in my class that I spent 35 hours a week with for nine years. We all take something different away from the experience, but I can guarantee you, many of us, including my friend Moishe the ambassador, will always carry Peretz Shul memories with us for the rest of our lives.
Post script: Ed. note: It didn’t take me too long to figure out who the “Moishe” was to whom Kinzey refers in his article. I was actually friends myself with “Moishe”, although I knew him better as Matthew Levin.
Ed. note: It didn’t take me too long to figure out who the “Moishe” was to whom Kinzey refers in his article. I was actually friends myself with “Moishe”, although I knew him better as Matthew Levin.
Matthew was always very independent-minded – even as a kid. That being said, he went on to an illustrious career in Canada’s diplomatic service. Among other posts he held, he was Canada’s Ambassador to Columbia, Cuba, and most recently Spain.
It was while he was Ambassador to Cuba that Matthew, along with his wife, Rosealba, played an instrumental role in helping Cuban Jews emigrate to Israel (since Israel and Cuba did not have diplomatic relations).
When I read Kinzey’s story I decided to send it to Matthew – before I outed him as the “Moishe” in the story. Matthew was pleasantly surprised to see that Kinzey mentioned him in a story and even further that he referred to him as “Moishe”.
In my email to Matthew I mentioned that the last time I had attempted to contact him was when Stephen Harper was Prime Minister and Matthew was Canada’s Ambassador to Cuba. At the time, some low level functionaries in what is known as Global Affairs Canada interceded and said that I would not be able to communicate directly with Matthew. Instead, I was told, I could submit any questions that I had to Global Affairs, they would vet them (no doubt looking for anything that might potentially embarrass the government, such as asking about Matthew’s boyhood years in Winnipeg).
So, when I reached out to Matthew – again, this time after reading Kinzey’s piece, I said that I didn’t know whether he would even receive my email since I suspected “apparatchiks” in the government would see it first – and probably attempt to prevent me from communicating with him directly – again.
I was surprised then, to receive a very warm response from Matthew – in which he explained that he is no longer under the supervision of government “apparatchiks”.
Here’s what Matthew Levin wrote to me, in part:
Wonderful to hear from you! I’m so glad you made the effort to reach out.
I finished my posting to Spain a couple of months ago and am now back in Ottawa and transitioning to retirement. So no more apparatchiks.
First of all, I hope you’re well and coping successfully with these strange times.
Your lovely message brings back all sorts of very fond memories. It’s a long time since anyone called me Moishe (often shortened to Moish back then). I never saw most of my Peretz Shul classmates after I left the school, as Kinzey recalls, at the start of Grade 5 (a long story). Kinzey was one of the very few I did see occasionally, including a few times when he was playing with Finjan. But most of the others I completely lost touch with. Now I sometimes wonder what has become of many of them. It’s really heartwarming to think that Kinzey (Martin at the time and I believe he was Mordechai in Yiddish, or maybe Mendel) remembered me as he was writing this story. Since you and I and our group of friends never called each other by our Yiddish names I’m surprised, but delighted, that you thought of me when you saw this reference to a Moishe.
Thanks so much for sending along Kinzey’s story. I’m sending you this reply before having read it, because I didn’t want to delay getting back to you, but I’ll certainly read it with great interest and undoubtedly pleasure. I really feel honoured and delighted to be included. If you’re in touch with Kinzey, please thank him and give him a big hug – virtual of course for now – from me.
Features
Cheap Weed In Canada: A Smart Shopper’s Guide

Since legalisation, cannabis has settled into Canadian life as an ordinary, regulated purchase. And like groceries or gas, the price can vary a surprising amount from one shop to the next once you start comparing.
For a lot of buyers, that has turned the focus to value. Affordable options like cheap weed prove a lower price and a tested, quality product can go together. This guide explains how to shop smart in Canada without cutting corners.
Why Has Affordable Cannabis Become So Popular?
Because the novelty has worn off, and buyers now shop like they do for anything else. In the early days, people paid whatever the new legal stores asked. That has changed.
A few things drove that shift:
- A maturing market, with more retailers competing on price.
- Online sellers, whose lower overhead keeps costs down.
- Savvier buyers, who now compare rather than grab the first option.
- A wider range of formats and budget-friendly bulk sizes.
The result is a real focus on getting value for money. Crowdsourced figures put the early average near $6.85 a gram, and cannabis price data from Statistics Canada shows how legal and illegal prices have differed since 2018.
That gap is exactly why shopping around pays off. A careful buyer can pay noticeably less than a careless one for a comparable product. The sticker price is only where the comparison starts.
How Do Canadians Shop for Cheaper Weed?
With the same care they bring to any regular expense. A handful of habits make the biggest difference. These are the ones worth adopting:
- Compare the per-gram price. It is the only fair way to weigh two options.
- Buy larger formats. Bigger quantities almost always lower the unit cost.
- Skip premium markups. Plain flower beats pricey pre-rolls for value.
- Watch for sales. Online retailers run them often, especially on holidays.
- Match potency to the plan. A stronger product means you use less each time.
None of these involve settling for a worse product. They simply put your money to better use, the same way you would stretch your money on any other purchase. The cheapest sticker is rarely the best value, and the priciest is seldom worth it.
The same logic applies whether you shop in person or online in Canada. Read the label, weigh the cost per gram, and let the numbers guide you rather than the branding.
Is There a Catch With Low-Priced Cannabis?
Not in the legal market, which is the part newcomers miss. In Canada, every legal product is tested and labelled to the same standard, whatever it costs.
That means a budget option from a licensed seller has cleared the same checks as a premium one. It is screened for contaminants, and its potency is verified. Price reflects branding, packaging, and store margins far more than basic safety.
The genuine differences are in the finer points. Premium flower might offer a better aroma or a richer flavour, and some formats simply cost more to make. For everyday use, though, a well-priced choice usually performs just fine.
The real catch is buying outside the legal system. Health Canada’s overview of the Cannabis Act is a sensible read on what legal really means. Buying legal protects you, not buying expensive.
What Makes a Cheap Purchase a Smart One?
A couple of quick checks, mostly. A real bargain holds up to a second look, while a false one does not. The table below shows what to weigh.
| Check | Why It Matters |
| Is the seller licensed? | Only legal retailers guarantee tested product |
| What is the per-gram cost? | The headline price can hide a weak deal |
| Is potency on the label? | Higher strength can stretch your money |
| Are there bulk or sale deals? | These usually beat single-unit pricing |
| What does delivery cost? | Shipping can erase an online saving |
Any shaky answer there is a reason to pause. A licensed seller with clear pricing and labelling is the safe choice, while a suspiciously cheap unlicensed source is not. The legal age applies regardless, at 18 or 19 depending on the province.
Treat cannabis like any other considered purchase. Compare, check the details, and let value rather than habit lead the decision. That is how modest savings add up across a whole year.
Before You Buy
- Cannabis prices vary widely by retailer, format, and store overhead.
- Comparing the per-gram cost is the fairest way to judge value.
- All legal Canadian cannabis is tested, so cheaper is not unsafe.
- Bulk buys, sales, and plain formats keep spending down.
- Always buy from a licensed source, and factor in delivery fees.

Photo by Jakub Zerdzicki on Pexels
Alt text: A shopper comparing prices online at home
Smart Savings, No Compromise
Buying affordable cannabis in Canada is not about chasing the lowest number you can find. It is about understanding what shapes the price and shopping with a little intention. Stick to licensed, tested products, compare the real cost per gram, and lean on bulk deals and online pricing. Do that, and an affordable choice stays a smart one, purchase after purchase.
Frequently Asked Questions
Is Cheap Weed Safe to Buy In Canada?
Yes, provided it comes from a licensed retailer. All legal cannabis in Canada is tested for contaminants and labelled for potency, regardless of price. A lower cost usually reflects branding and overhead rather than weaker safety, so a budget option from a legal seller is still a safe one.
How Do I Find the Best Cannabis Deals?
Compare the per-gram price, buy larger formats, and watch for sales from online retailers. Checking potency against price helps too, since a stronger product can mean you use less. The key is shopping deliberately instead of defaulting to the same brand or store each time.
Why Is Cannabis Cheaper Online?
Online sellers usually carry lower overhead than physical stores, and they run sales and bulk deals more often. That lets them price competitively while still selling tested, legal product. Just remember to factor in shipping, which can offset the saving on a small order.
Does Paying More Mean Better Cannabis?
Not necessarily. Price reflects branding, format, and store margins as much as quality, and all legal product meets the same testing standards. Premium options may offer a better aroma or appearance, but a well-priced choice often works just as well day to day.
Features
Author and lifelong nurse Tilda Shalof’s new book a guide not only for young nurses but one that will appeal to a wider readership

By MYRON LOVE Tilda Shalof’s most recent book – “The Handover – a Nurse’s Last Shift” was, in the words of its author, “written for the general public, to understand nursing. Nursing is everyone’s concern, not just nurses. The general public has a stake in the matter,” she observes.
I can guarantee that there are plenty of stories and anecdotes that the author shares from her own experiences that will also be of interest to a wider readership. I certainly enjoyed the book.
The title – “The Handover,” she explains, is the regular exchange between nurses going off their shift and the nurses beginning the next shift, during which the outgoing nurses pass on all relevant information about the patients under their care to the incoming nurses. A recurring thread throughout the book – of close to 400 pages – is the retiring Shalof’s interaction with three student nurses whom she had recently befriended through one of her many speaking engagements. In particular, Shalof gives co-writing credit to one Lisa Mochrie – a nurse who the author acted as mentor to during Mochrie’s last period as a student and continuing through her early nursing career.
There is a tendency for many people to take for granted people I would describe as working in a service capacity such as nursing. One of the reasons that Shalof points out in her book for our ongoing nursing shortages is that young men and women are more likely to be encouraged to pursue a medical career (to be a doctor) than a nurse. This, she points out, despite the fact that hospitals can function without doctors – but not without nurses.
Some other factors, she notes, are the ever increasing demands of documentation – which detract from patient care – and regulations, which have taken much of the satisfaction out of the profession.
In an interview with this writer, she observes that Jewish nurses are few and far between because nursing is not a profession that most Jewish families encourage. (I can only name a handful of Jewish nurses that I have known or have come across.)
She spoke about how she became a nurse early in life to her aged and ailing parents – being the only daughter – (she has three older brothers) and the last of her siblings to leave home. In “The Handover”, she also makes frequent reference to fictional nurse Cherry Ames – the heroine of numerous books written between 1943 and 1968 – as inspiration for Shalof’s choice of career.
For the first 30 years as a nurse, Shalof worked in an intensive care ward at Toronto General Hospital. She subsequently worked for a short time at an HIV clinic and, later a hospital day clinic and a neurosurgery unit. She also spent several summers as a camp nurse at a Jewish camp while her kids were campers there.
“The Handover” is Shalof’s seventh book. Her first book, published in 2004, was “A Nurse’s Story,” chronicling her experiences over 30 years as an ICU nurse. Among her other books are:“Camp Nurse,” recounting anecdotes from her time working summers at her children’ summer camps, and “Opening My Heart” – an account of the profession from the point of view of a patient after she had open heart surgery.
Coincidently, she notes, she began her first book around the time of the SARS outbreak in Toronto in 2003. Shalof says she started writing her latest book at the height of the Covid lockdowns, which she references from time to time in the book. .
The approach Shalof has taken in writing “The Handover” – following a foreword and introduction – is literally an A to Z overview of everything there is to know about nursing – with each chapter focusing on one specific letter of the alphabet. Each chapter relates her thoughts and tells anecdotes from her own nursing experiences over 40 years in the profession, as well as her interactions with Lisa Mochrie and the other two student nurses as they transition from students to professionals.
In her conclusion, she observes that “nursing can be a path to making a difference – having an impact. It can be a front row seat at the theatre of life. Or it can be a job, a way to make a living and help support your family. “
Most importantly, she added, “make sure you try to have some fun. Do everything in your power to enjoy being a nurse”.
Although the now 67-yeear-old author is retired from the practice of nursing, she remains in demand as a speaker and advisor. She continues to get calls from throughout North America seeking her advice.“The Handover” is available from the University of Toronto Press.
Features
Michael Mitchell: His Labour of Love in Law

By GERRY POSNER The Mitchell name in Winnipeg has been around a long time and much of the the name recognition stems from the long connection of the family to a business known as Mitchell Fabrics, a mainstay on Main Street for many years. Established by Mendel Mitchell generations ago and not closed until 2017, many family members, including in-laws, worked there as managers, students and retirees. And yet, the family vocation was not limited to just the business, t it stretched out into the world of law, and more specifically the field of labour Law. One particular Mitchell reached the peak of all aspects of Labour Law. Three Mitchells: Leon, son Grant (a senior management side labour lawyer in Winnipeg), and daughter April Katz (an academic at the University of Victoria Law School), had stellar careers in that field. Yet another Mitchell, Michael, also achieved great acclaim as a labour lawyer. Michael, a product of the south end of Winnipeg, is the son of the late Harry and Gertrude (Sirluck) Mitchell, so he has some impressive genes going for him. But he has added to the story immeasurably.
Perhaps it all began for Michael Mitchell when he graduated from what was the first and only Grade 7 Hebrew school class at Herzlia Academy. He later was Regional Vice-President of AZA in his teenage years. After two years at Joseph Wolinsky Collegiate and two more at Grant Park High School, Mitchell went off to the University of Manitoba for his first year and then on to the University of Toronto, where he obtained a BA in Political Science. Then came law school, also at the University of Toronto, from where he graduated with an LLB in 1975. Along the way, he married the former Lynne Berman ( also from Winnipeg).That union produced three Mitchell daughters, two of whom are physicians – in psychiatry and neurology respectively, while the third is a pioneering pre-school educator. Michael and Lynne also have six grandchildren.
For a large part of his career as a lawyer, Michael Mitchell practiced law in Toronto as a senior partner in the firm of Sack Goldblatt Mitchell – from 1980 through 2014, having joined the firm in 1975 as a student. The firm was committed to the union side practice of Labour and Employment Law. Not so surprisingly, he had to appear at all levels of courts, also administrative tribunals.To his credit, his work and impressive track record was recognized by his peers as he was named a leading labour lawyer in Canadian Lexpert Directory and was frequently recommended in Best Lawyers in Canada. Between 1982- 2006, Mitchell was also the managing partner of the firm, which suggests to me an ability to manage people, not an insignificant skill. During his tenure as the managing partner, the law firm grew from just under ten lawyers to over fifty, with offices in both Toronto and Ottawa. His responsibilities were firm leadership, strategic decision making and financial management.
But, what a career Mitchell has had. For starters, aside from his time as a practicing lawyer in the field of labour law, he has, since his leaving the practice, just changed hats. From 2015 to 2018, he was part time Vice-Chair of the Ontario Labour Relations Board and, from 2018 as of this moment, he has become full time Vice-Chair at the same Ontario Labour Relations Board. Needless to say that, over the course of his administrative work since 2015, Mitchell has been at the centre of some significant decisions and, if you are interested, I can direct you to the selected substantive decisions in which Mitchell has been involved.
Moreover, Mitchell has worked and continues to work in the area of mediation and arbitration of both labour and indeed civil law. This is a large area, to put it mildly. For starters, there is the entire field of grievance arbitration. To be involved in cases of this kind, your name has to be put up by one of the parties and often agreed to by the other party. That means you have credibility with both of the protagonists. Mitchell clearly has that kind of reputation and draws support from both sides of the aisles – as it is referred to in some circles. He has been an arbitrator/ referee in many cases, including the famous 1986-1990 Class Action settlement related to individuals who had contracted Hepatitis C. Further, he has conducted numerous civil mediations related to employment, contracts and human rights matters. Mitchell also mediates and arbitrates collective bargaining disputes.
One of Mitchell’s’ main achievements was that he was invited between 2015-2017 to be a Special Advisor (with capital letters, no less) to the Ontario Minister of Labour with regard to the Changing Workplace Review. This was a landmark review of the Ontario Employment Standards Act and the Labour Relations Act where he, together with Justice John Murray, recommended many legislative changes to protect workers from the negative impacts of precarious employment. The best part of his work was that many of th recommendations were actually adopted. Other recommendations remain for future governments across the country to consider.
If you really want to delve into the Michael Mitchell career, you should know that, over the span of his career there are many publications that he has authored. The main one is his textbook on the Ontario Labour Relations Board, which he co-authored with his early mentor, Jeffrey Sack, and which remains the leading authority on the Ontario Board.
Mitchell comes by his passion for labour law honestly. His uncle, Leon Mitchell, was an iconic force on the union side in his practice of law in Winnipeg and was the inspiration for Michael to enter law to become a labour lawyer in the first place. In fact, it was Leon who introduced Michael to a man in Toronto who recommended Michael to connect with an up and coming labour lawyer in Toronto named Jeffrey Sack K.C. That connection resulted in the Sack Goldblatt Mitchell law firm. As well, Michael was well known to Sid Green during the early years of Sid’s law career, also his early days as a Cabinet Minister in the Schreyer NDP government. Sid was a person who exerted a significant influence on Michael.
With all that on his plate, Mitchell found time to be the president of the Darchei Noam Synagogue in Toronto between 2004-2008. He has also been the president of the Jewish Reconstructionist Federation of North America. During his term, he led the merger negotiations which ultimately resulted in the current structure of that movement ,which is now referred to as Reconstructing Judaism. Its singular aspect is that it consists of a single organization combining congregations plus a Rabbinical School. That was enough to get Mitchell an invitation to attend one of President Obama’s Chanukah parties at the White House during the Obama term. As well, to this day, Mtchell sits as a Director of the New Israel Fund of Canada.
Mitchell has his feet still planted in Winnipeg. His two sisters live there, as well as Lynne’s sister. In fact, he just visited Winnipeg for his sister Ruth Ann’s and Paula’s 85th and 80th birthdays respectively. And to keep up to date, Michael and Lynne Mitchell have long had a subscription to the Jewish Post.
In short, at just under 80, Michael Mitchell is moving like he is eighteen. The longevity of his career may soon rival the longevity of the family business, Mitchell Fabrics.




