Features
New thriller by Israeli-Canadian Herschy Katz combines love of hockey with intrigue behind the Iron Curtain in 1972
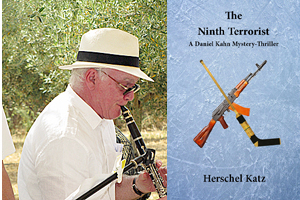
By BERNIE BELLAN In 2019 I wrote a review of a book titled “The Clarinetist”. It had been sent to me by an expatriate Canadian who had moved to Israel in 1984 by the name of Herschel Katz.
As I noted in that review, the book was quite good for a first-time author. In it we were introduced to a young Montreal high school student by the name of Danny Kahn who ends up enmeshed in an intriguing situation having to do with the Montreal father of his girlfriend.
The father, it turns out, is tied in with some very shady characters and, one thing leading to another, Danny becomes involved in some hair-raising adventures that take him from Montreal to New York, and then Israel.
Katz had become a writer, he noted on the book jacket, because “Several years ago, the author worked as a part time book reviewer, then decided to try writing his own story.”
Now, two years later, Katz has come up with another mystery novel, again featuring Daniel Khan (who, I guess, has graduated from being called “Danny”). By this time Daniel has progressed to becoming a 22-year old medical student at McGill, also a writer for the McGill student newspaper. The book is titled “The Ninth Terrorist” and, after reading it, I sent Katz a note saying he had the makings of another Daniel Silva, who is one of the world’s most popular mystery writers and who has also created a recurrent hero by the name of Gabriel Allon.
As good as “The Clarinetist” was for a first-time effort, “The Ninth Terrorist” shows terrific improvement on Katz’s part in terms of plot structuring and dialogue. The book actually blends three different plots into one overarching story, which has to do with nefarious activities involving East Bloc bad guys in the 1970s – when the Soviet Union was still very much a Communist dictatorship and closely aligned with Palestinian terrorist organizations .
The story begins with the legendary “Summit Series” between Canada and the USSR in 1972, in which a team composed of Canada’s best professional hockey players from the NHL faced off against the powerful Soviet team in an eight-game series.
I had forgotten though, that at the same time as that series was being played, the Munich Olympics were also being staged and, anyone who was around then will no doubt recall how horrified we all were at the tragic murder of 11 Israeli athletes by members of the terrorist group known as “Black September”.
Into that backdrop of high drama Katz inserts Daniel Khan, who continues to display the ability as a clever agent that he first demonstrated in “The Clarinetist”. This time, however, Daniel is enmeshed in a series of events in which he has to play multiple roles, all the time fully aware that one slip-up could lead to his arrest and imprisonment in the Soviet Union.
Katz is clearly a great hockey fan and his depictions of the action during games are quite vivid. You don’t have to be a sports fan at all in order to enjoy the book though, as hockey merely serves as the excuse for Daniel to be able to go to the Soviet Union as a reporter. Still, setting so much of the action in venues that would resonate with Canadian sports fans makes “The Ninth Terrorist” all the more appealing.
I would note, too, that in my review of “The Clarinetist” I was somewhat critical of the dialogue in that book, writing that Katz could have used help in creating some more authentic sounding conversations between characters. This time around, the dialogue is much improved and sparkles with often very clever exchanges.
Turning Khan into a reporter is an especially credible device, as reporters have often served as agents for various intelligence services. The fact that Khan is a Canadian Jewish reporter who can easily substantiate his wanting to go to the Soviet Union (and who also speaks German, it turns out) certainly adds plausibility to his becoming an agent for not just one intelligence agency, but several, all of which are aware just how useful he can be to them.
One aspect of “The Ninth Terrorist”, however, that seems drawn straight out of the 1960s “Mission Impossible” television series (and later, the movies as well), is the use of facial disguises. Having a number of different characters put on masks that are so lifelike they can get you through any number of checkpoints is something that still remains a largely fictitious plot device – even at a time when 3D print technology has certainly made it more feasible.
Still, the ruse that Daniel Khan must employ in going back to the Soviet Union a second time – four months after the first Canada-Soviet series, certainly adds to the complexity – and intrigue of what is already a terrific spy novel. In fact, not only must he adopt a disguise at various times, he has to help others disguise themselves. At times it all becomes a little dizzying trying to remember just who it is that not only Daniel is pretending to be, but others as well.
Into this already fairly complicated plot Katz inserts a quite clever subplot having to do with someone who purportedly assisted the members of Black September when they went about kidnapping the 11 Israeli athletes in 1972. The individual, who is the “ninth terrorist” referred to in the title, turns out to be an extremely dangerous agent and Katz certainly makes this character come alive.
With action aplenty and very creative plotting, “The Ninth Terrorist” is an excellent thriller. When one considers that both “The Clarinetist” and “The Ninth Terrorist” have been self-published by Herschy Katz, one wonders how long it will be before he’s approached by a major publisher with a juicy offer to continue producing more in what could become a Daniel Khan series.
I asked Herschy how one could buy “The Ninth Terrorist”. (He had sent it to me as a pdf.) He replied that “My book is available directly from Pomeranz Booksellers in Jerusalem. www.Pomeranzbooks.com. My previous book, “The Clarinetist”, is also available through them.”
Both “The Clarinetist” and “The Ninth Terrorist” are now available on Amazon – Kindle for $9.99 CDN.
Then Herschy sent me another quite interesting tidbit of information after I told him that I was going to print an accompanying article, also about someone who entered into some subterfuge in the Soviet Union (in his case, smuggling tallisim and sidurim), during a hockey tournament. (See my story about Sherry Bassin on the opposite page.)
After I wrote Herschy about Sherry Bassin’s escapade, he sent me this note:
Dear Bernie,
A personal note about me you may want to add to your book review. My late father, Boris Katz, z”l, escaped Stalin in 1924 and came to Montreal as a young man. He and his nephew founded a business making men’s clothes, which became quite successful. During the 1950s, 60s and 70s, he would send packages of clothes to his family back in the USSR. Knowing how the Russian customs inspectors would steal the contents, he would pack extra jeans and put some American dollars inside the box, which, of course, were stolen. However, inside the cuffs and collars of the clothes that weren’t stolen, he sewed large amounts of cash, which his family ended up getting.
This tidbit I incorporated into my story, “The Ninth Terrorist”.
Herschy
I enjoy helping to publicize Jewish writers (in particular, writers from Israel) whose works might not otherwise receive much publicity because they’re self-published. In Herschy Katz’s case, providing a boost to a former Canadian who made aliyah 37 years ago, but who’s also remained a huge hockey fan, should be ample reason for some readers to want to proceed to buy “The Ninth Terrorist”. Herschy even sets some of the action in Winnipeg – in case you needed any more cajoling!
Features
Cheap Weed In Canada: A Smart Shopper’s Guide

Since legalisation, cannabis has settled into Canadian life as an ordinary, regulated purchase. And like groceries or gas, the price can vary a surprising amount from one shop to the next once you start comparing.
For a lot of buyers, that has turned the focus to value. Affordable options like cheap weed prove a lower price and a tested, quality product can go together. This guide explains how to shop smart in Canada without cutting corners.
Why Has Affordable Cannabis Become So Popular?
Because the novelty has worn off, and buyers now shop like they do for anything else. In the early days, people paid whatever the new legal stores asked. That has changed.
A few things drove that shift:
- A maturing market, with more retailers competing on price.
- Online sellers, whose lower overhead keeps costs down.
- Savvier buyers, who now compare rather than grab the first option.
- A wider range of formats and budget-friendly bulk sizes.
The result is a real focus on getting value for money. Crowdsourced figures put the early average near $6.85 a gram, and cannabis price data from Statistics Canada shows how legal and illegal prices have differed since 2018.
That gap is exactly why shopping around pays off. A careful buyer can pay noticeably less than a careless one for a comparable product. The sticker price is only where the comparison starts.
How Do Canadians Shop for Cheaper Weed?
With the same care they bring to any regular expense. A handful of habits make the biggest difference. These are the ones worth adopting:
- Compare the per-gram price. It is the only fair way to weigh two options.
- Buy larger formats. Bigger quantities almost always lower the unit cost.
- Skip premium markups. Plain flower beats pricey pre-rolls for value.
- Watch for sales. Online retailers run them often, especially on holidays.
- Match potency to the plan. A stronger product means you use less each time.
None of these involve settling for a worse product. They simply put your money to better use, the same way you would stretch your money on any other purchase. The cheapest sticker is rarely the best value, and the priciest is seldom worth it.
The same logic applies whether you shop in person or online in Canada. Read the label, weigh the cost per gram, and let the numbers guide you rather than the branding.
Is There a Catch With Low-Priced Cannabis?
Not in the legal market, which is the part newcomers miss. In Canada, every legal product is tested and labelled to the same standard, whatever it costs.
That means a budget option from a licensed seller has cleared the same checks as a premium one. It is screened for contaminants, and its potency is verified. Price reflects branding, packaging, and store margins far more than basic safety.
The genuine differences are in the finer points. Premium flower might offer a better aroma or a richer flavour, and some formats simply cost more to make. For everyday use, though, a well-priced choice usually performs just fine.
The real catch is buying outside the legal system. Health Canada’s overview of the Cannabis Act is a sensible read on what legal really means. Buying legal protects you, not buying expensive.
What Makes a Cheap Purchase a Smart One?
A couple of quick checks, mostly. A real bargain holds up to a second look, while a false one does not. The table below shows what to weigh.
| Check | Why It Matters |
| Is the seller licensed? | Only legal retailers guarantee tested product |
| What is the per-gram cost? | The headline price can hide a weak deal |
| Is potency on the label? | Higher strength can stretch your money |
| Are there bulk or sale deals? | These usually beat single-unit pricing |
| What does delivery cost? | Shipping can erase an online saving |
Any shaky answer there is a reason to pause. A licensed seller with clear pricing and labelling is the safe choice, while a suspiciously cheap unlicensed source is not. The legal age applies regardless, at 18 or 19 depending on the province.
Treat cannabis like any other considered purchase. Compare, check the details, and let value rather than habit lead the decision. That is how modest savings add up across a whole year.
Before You Buy
- Cannabis prices vary widely by retailer, format, and store overhead.
- Comparing the per-gram cost is the fairest way to judge value.
- All legal Canadian cannabis is tested, so cheaper is not unsafe.
- Bulk buys, sales, and plain formats keep spending down.
- Always buy from a licensed source, and factor in delivery fees.

Photo by Jakub Zerdzicki on Pexels
Alt text: A shopper comparing prices online at home
Smart Savings, No Compromise
Buying affordable cannabis in Canada is not about chasing the lowest number you can find. It is about understanding what shapes the price and shopping with a little intention. Stick to licensed, tested products, compare the real cost per gram, and lean on bulk deals and online pricing. Do that, and an affordable choice stays a smart one, purchase after purchase.
Frequently Asked Questions
Is Cheap Weed Safe to Buy In Canada?
Yes, provided it comes from a licensed retailer. All legal cannabis in Canada is tested for contaminants and labelled for potency, regardless of price. A lower cost usually reflects branding and overhead rather than weaker safety, so a budget option from a legal seller is still a safe one.
How Do I Find the Best Cannabis Deals?
Compare the per-gram price, buy larger formats, and watch for sales from online retailers. Checking potency against price helps too, since a stronger product can mean you use less. The key is shopping deliberately instead of defaulting to the same brand or store each time.
Why Is Cannabis Cheaper Online?
Online sellers usually carry lower overhead than physical stores, and they run sales and bulk deals more often. That lets them price competitively while still selling tested, legal product. Just remember to factor in shipping, which can offset the saving on a small order.
Does Paying More Mean Better Cannabis?
Not necessarily. Price reflects branding, format, and store margins as much as quality, and all legal product meets the same testing standards. Premium options may offer a better aroma or appearance, but a well-priced choice often works just as well day to day.
Features
Author and lifelong nurse Tilda Shalof’s new book a guide not only for young nurses but one that will appeal to a wider readership

By MYRON LOVE Tilda Shalof’s most recent book – “The Handover – a Nurse’s Last Shift” was, in the words of its author, “written for the general public, to understand nursing. Nursing is everyone’s concern, not just nurses. The general public has a stake in the matter,” she observes.
I can guarantee that there are plenty of stories and anecdotes that the author shares from her own experiences that will also be of interest to a wider readership. I certainly enjoyed the book.
The title – “The Handover,” she explains, is the regular exchange between nurses going off their shift and the nurses beginning the next shift, during which the outgoing nurses pass on all relevant information about the patients under their care to the incoming nurses. A recurring thread throughout the book – of close to 400 pages – is the retiring Shalof’s interaction with three student nurses whom she had recently befriended through one of her many speaking engagements. In particular, Shalof gives co-writing credit to one Lisa Mochrie – a nurse who the author acted as mentor to during Mochrie’s last period as a student and continuing through her early nursing career.
There is a tendency for many people to take for granted people I would describe as working in a service capacity such as nursing. One of the reasons that Shalof points out in her book for our ongoing nursing shortages is that young men and women are more likely to be encouraged to pursue a medical career (to be a doctor) than a nurse. This, she points out, despite the fact that hospitals can function without doctors – but not without nurses.
Some other factors, she notes, are the ever increasing demands of documentation – which detract from patient care – and regulations, which have taken much of the satisfaction out of the profession.
In an interview with this writer, she observes that Jewish nurses are few and far between because nursing is not a profession that most Jewish families encourage. (I can only name a handful of Jewish nurses that I have known or have come across.)
She spoke about how she became a nurse early in life to her aged and ailing parents – being the only daughter – (she has three older brothers) and the last of her siblings to leave home. In “The Handover”, she also makes frequent reference to fictional nurse Cherry Ames – the heroine of numerous books written between 1943 and 1968 – as inspiration for Shalof’s choice of career.
For the first 30 years as a nurse, Shalof worked in an intensive care ward at Toronto General Hospital. She subsequently worked for a short time at an HIV clinic and, later a hospital day clinic and a neurosurgery unit. She also spent several summers as a camp nurse at a Jewish camp while her kids were campers there.
“The Handover” is Shalof’s seventh book. Her first book, published in 2004, was “A Nurse’s Story,” chronicling her experiences over 30 years as an ICU nurse. Among her other books are:“Camp Nurse,” recounting anecdotes from her time working summers at her children’ summer camps, and “Opening My Heart” – an account of the profession from the point of view of a patient after she had open heart surgery.
Coincidently, she notes, she began her first book around the time of the SARS outbreak in Toronto in 2003. Shalof says she started writing her latest book at the height of the Covid lockdowns, which she references from time to time in the book. .
The approach Shalof has taken in writing “The Handover” – following a foreword and introduction – is literally an A to Z overview of everything there is to know about nursing – with each chapter focusing on one specific letter of the alphabet. Each chapter relates her thoughts and tells anecdotes from her own nursing experiences over 40 years in the profession, as well as her interactions with Lisa Mochrie and the other two student nurses as they transition from students to professionals.
In her conclusion, she observes that “nursing can be a path to making a difference – having an impact. It can be a front row seat at the theatre of life. Or it can be a job, a way to make a living and help support your family. “
Most importantly, she added, “make sure you try to have some fun. Do everything in your power to enjoy being a nurse”.
Although the now 67-yeear-old author is retired from the practice of nursing, she remains in demand as a speaker and advisor. She continues to get calls from throughout North America seeking her advice.“The Handover” is available from the University of Toronto Press.
Features
Michael Mitchell: His Labour of Love in Law

By GERRY POSNER The Mitchell name in Winnipeg has been around a long time and much of the the name recognition stems from the long connection of the family to a business known as Mitchell Fabrics, a mainstay on Main Street for many years. Established by Mendel Mitchell generations ago and not closed until 2017, many family members, including in-laws, worked there as managers, students and retirees. And yet, the family vocation was not limited to just the business, t it stretched out into the world of law, and more specifically the field of labour Law. One particular Mitchell reached the peak of all aspects of Labour Law. Three Mitchells: Leon, son Grant (a senior management side labour lawyer in Winnipeg), and daughter April Katz (an academic at the University of Victoria Law School), had stellar careers in that field. Yet another Mitchell, Michael, also achieved great acclaim as a labour lawyer. Michael, a product of the south end of Winnipeg, is the son of the late Harry and Gertrude (Sirluck) Mitchell, so he has some impressive genes going for him. But he has added to the story immeasurably.
Perhaps it all began for Michael Mitchell when he graduated from what was the first and only Grade 7 Hebrew school class at Herzlia Academy. He later was Regional Vice-President of AZA in his teenage years. After two years at Joseph Wolinsky Collegiate and two more at Grant Park High School, Mitchell went off to the University of Manitoba for his first year and then on to the University of Toronto, where he obtained a BA in Political Science. Then came law school, also at the University of Toronto, from where he graduated with an LLB in 1975. Along the way, he married the former Lynne Berman ( also from Winnipeg).That union produced three Mitchell daughters, two of whom are physicians – in psychiatry and neurology respectively, while the third is a pioneering pre-school educator. Michael and Lynne also have six grandchildren.
For a large part of his career as a lawyer, Michael Mitchell practiced law in Toronto as a senior partner in the firm of Sack Goldblatt Mitchell – from 1980 through 2014, having joined the firm in 1975 as a student. The firm was committed to the union side practice of Labour and Employment Law. Not so surprisingly, he had to appear at all levels of courts, also administrative tribunals.To his credit, his work and impressive track record was recognized by his peers as he was named a leading labour lawyer in Canadian Lexpert Directory and was frequently recommended in Best Lawyers in Canada. Between 1982- 2006, Mitchell was also the managing partner of the firm, which suggests to me an ability to manage people, not an insignificant skill. During his tenure as the managing partner, the law firm grew from just under ten lawyers to over fifty, with offices in both Toronto and Ottawa. His responsibilities were firm leadership, strategic decision making and financial management.
But, what a career Mitchell has had. For starters, aside from his time as a practicing lawyer in the field of labour law, he has, since his leaving the practice, just changed hats. From 2015 to 2018, he was part time Vice-Chair of the Ontario Labour Relations Board and, from 2018 as of this moment, he has become full time Vice-Chair at the same Ontario Labour Relations Board. Needless to say that, over the course of his administrative work since 2015, Mitchell has been at the centre of some significant decisions and, if you are interested, I can direct you to the selected substantive decisions in which Mitchell has been involved.
Moreover, Mitchell has worked and continues to work in the area of mediation and arbitration of both labour and indeed civil law. This is a large area, to put it mildly. For starters, there is the entire field of grievance arbitration. To be involved in cases of this kind, your name has to be put up by one of the parties and often agreed to by the other party. That means you have credibility with both of the protagonists. Mitchell clearly has that kind of reputation and draws support from both sides of the aisles – as it is referred to in some circles. He has been an arbitrator/ referee in many cases, including the famous 1986-1990 Class Action settlement related to individuals who had contracted Hepatitis C. Further, he has conducted numerous civil mediations related to employment, contracts and human rights matters. Mitchell also mediates and arbitrates collective bargaining disputes.
One of Mitchell’s’ main achievements was that he was invited between 2015-2017 to be a Special Advisor (with capital letters, no less) to the Ontario Minister of Labour with regard to the Changing Workplace Review. This was a landmark review of the Ontario Employment Standards Act and the Labour Relations Act where he, together with Justice John Murray, recommended many legislative changes to protect workers from the negative impacts of precarious employment. The best part of his work was that many of th recommendations were actually adopted. Other recommendations remain for future governments across the country to consider.
If you really want to delve into the Michael Mitchell career, you should know that, over the span of his career there are many publications that he has authored. The main one is his textbook on the Ontario Labour Relations Board, which he co-authored with his early mentor, Jeffrey Sack, and which remains the leading authority on the Ontario Board.
Mitchell comes by his passion for labour law honestly. His uncle, Leon Mitchell, was an iconic force on the union side in his practice of law in Winnipeg and was the inspiration for Michael to enter law to become a labour lawyer in the first place. In fact, it was Leon who introduced Michael to a man in Toronto who recommended Michael to connect with an up and coming labour lawyer in Toronto named Jeffrey Sack K.C. That connection resulted in the Sack Goldblatt Mitchell law firm. As well, Michael was well known to Sid Green during the early years of Sid’s law career, also his early days as a Cabinet Minister in the Schreyer NDP government. Sid was a person who exerted a significant influence on Michael.
With all that on his plate, Mitchell found time to be the president of the Darchei Noam Synagogue in Toronto between 2004-2008. He has also been the president of the Jewish Reconstructionist Federation of North America. During his term, he led the merger negotiations which ultimately resulted in the current structure of that movement ,which is now referred to as Reconstructing Judaism. Its singular aspect is that it consists of a single organization combining congregations plus a Rabbinical School. That was enough to get Mitchell an invitation to attend one of President Obama’s Chanukah parties at the White House during the Obama term. As well, to this day, Mtchell sits as a Director of the New Israel Fund of Canada.
Mitchell has his feet still planted in Winnipeg. His two sisters live there, as well as Lynne’s sister. In fact, he just visited Winnipeg for his sister Ruth Ann’s and Paula’s 85th and 80th birthdays respectively. And to keep up to date, Michael and Lynne Mitchell have long had a subscription to the Jewish Post.
In short, at just under 80, Michael Mitchell is moving like he is eighteen. The longevity of his career may soon rival the longevity of the family business, Mitchell Fabrics.




