Features
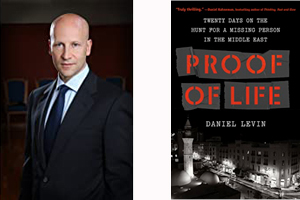
“Proof of Life” – New book about Syrian conflict tells spellbinding story of one man’s search for a young American who went missing in 2014
Review by BERNIE BELLAN The war in Syria which began in 2011 following upon earlier upheavals in the Arab world that were ignited by what became known as the Arab Spring has, by and large, vanished from the headlines of the world’s newspapers.
Once Russia intervened on the side of Bashar Al Assad in 2015, along with Iran and its Hezbollah acolytes, the tide was turned in favour of Assad. It is true that American troops, along with their various allies in Syria, were instrumental in ridding Syria of ISIS, but there were many more factions fighting the Assad regime than ISIS.
The complex world of what really amounted to inter-tribal warfare in Syria resulted in some of the most atrocious acts imaginable committed by all sides in the conflict, although when it came to the use of military hardware to massacre entire populations, Assad’s forces set new levels of barbarity in terms of the degree to which they were willing to gas, bomb, and murder innocent civilians throughout the conflict.
Within this nightmarish world, however, there were many individuals who not only did not suffer at all during the conflict – they actually thrived. Some were members of different militias who capitalized on capturing Western journalists and humanitarian workers in Syria, holding them for huge ransoms when they could.
We in the West were witness to the horrendous brutality that ISIS was capable of when it came to dealing with those captured Westerners – including their beheadings on a regular basis, but other groups were also willing to engage in equally savage treatment of innocent Westerners. In the cases of those other groups, however, the goal by and large was to trade Westerners for money.
Often captured journalists or humanitarian workers would be traded back and forth among groups. There were different reasons for the shuffling around of prisoners. For one, it made it almost impossible for anyone wanting to retrieve those prisoners to keep track of them. Secondly, at different times different groups placed different values on certain prisoners, depending on where they came from and with whom those groups were in a position to negotiate.
Into this hellish world stepped Daniel Levin, a Swiss-born Jew now living in the United States whose expertise is in negotiating with some of the world’s most unsavory characters. Levin is a lawyer by training and his legal negotiation skills were put to good use when he began working “with a European foundation and select individuals in Syria” in what became a project known as “Project Bistar”.
The purpose of Project Bistar, Levin explains in an incredibly fascinating new book (that is yet to be released for sale to the public) titled “Proof of Life”, was to mediate between the warring sides in the Syrian conflict, “in the hope of working quietly behind the scenes toward a negotiated settlement and, at a second stage, identifying young, next-generation individuals of the Alawite, Sunni, Druze, and Christian communities with leadership potential.”
Levin explains that, until 2015 when the Russians intervened on his side, Assad appeared amenable to a negotiated settlement, especially when rebel forces were inflicting terrible damage on his own forces.
With that as background information, in 2014 Levin found himself thrust into a situation totally unexpectedly in which his negotiating skills were put to a supreme test.
As a press release that was sent to me in January described it, “Daniel Levin was at his office one day when he got a call from an acquaintance with an urgent, cryptic request to meet in Paris. A young man had gone missing in Syria. No government, embassy, or intelligence agency would help. Could he? So begins a suspenseful, shocking, and at times brutal true story of one man’s search to find a missing person in Syria over eighteen tense days.”
Thus begins “Proof of Life: The Undercover Search for a Missing Person in Syria, where Arms, Drugs, and People Are for Sale“.
This lengthy preamble to my review of the book was necessary to provide some context for what the book is all about. Since the story that Levin tells – and the events which he describes are all true – although he has changed the names of most of the characters in order to protect the identities of individuals whose lives might be in danger, even years after the events which he describes.
Reading “Proof of Life” is like reading any well-written, fast paced thriller – except in this case, knowing that what you are reading really did happen will often leave you feeling physically ill when you realize the depths to which humans are capable of sinking to the present day. And I’m not just talking about the depravities of various armed groups around the world, many of which are Islamic it must be said (whether in the Middle East, Africa, the Philippines or any other of a number of areas in which offshoots of Al Qaeda or ISIS still hold sway).
Some of the most notorious characters in “Proof of Life” are not at all involved in actual fighting; instead they are the parasites who see opportunities in conflict situations to make vast sums of money supplying such commodities as drugs and women to the fighters.
It was within this dangerous and completely shadowy world that Levin found himself when he was asked to help obtain information about a young American by the name of Paul Blocher who had somehow entered into Syria sometime in 2014 – and disappeared.
As Levin describes it, he was contacted by an old friend who asked him for a favour, which was to use his various and very useful contacts throughout the region to do what he could to find out what happened to Blocher.
What follow sin the book is a complex series of encounters with some fascinating characters, most of whom are Arabs of varying nationalities, in locations including Ankara, Beirut, Washington, Amman, and Dubai, as Levin pursues a trail replete with scattered bits of information that bring him ever closer to the one character who he is certain can reveal what actually happened to Paul Blocher.
Throughout reading this book I couldn’t help thinking that Levin, who doesn’t at all hide his Jewish identity, was quite fearless in his willingness to seek out individuals whose reputations would leave just about anyone else terrified to even go anywhere near them, let alone try and arrange to meet them.
Given that he had been tasked with an assignment that very few individuals in the world would be capable of performing, as you read the very careful preparations he continually put in place prior to his meeting any of these dangerous individuals, although Levin doesn’t describe to any extent how he developed his unique expertise in negotiation and subterfuge, you can only marvel at the thinking he displayed at all times in planning his course of action.
At a certain point in the book though, the name of a drug known as “captagon” began to take on a prominent role in the story. I had to digress from reading “Proof of Life” to acquaint myself with just what Captagon is.
Captagon is a powerful amphetamine that is most popular in the Middle East, where it is both the recreational drug of choice in such countries as Saudi Arabia and the drug that was used by all sides during the Syrian conflict that, in the words of a BBC correspondent describing how Captagon is used in Syria,“gives people a euphoric feeling that they can take on the world and are relatively indomitable. [It] suppresses appetite and gives you a very long burst of energy, something like 18 to 24 hours.”
“Amphetamine use by fighters is commonplace, but I wondered if the specific properties of Captagon made it the perfect war drug.
“ ‘That depends on what your values are in the war,’ “ according to Max Kravits, a researcher who has spent years studying the use of Captagon in the Syrian conflict.
“ It is incredibly deteriorating and debilitating and it makes fighters take risks they otherwise wouldn’t take. But if your goal is simply to take said hill regardless of the human cost, it certainly seems to be doing the job.’ “
As Levin pursued his quest to find out what happened to Paul Blocher, he was led ever closer to the one man who, it is had become apparent from a variety of sources, would be able to tell Levin what happened to Blocher.
That man’s name was “Anas” and if you ever wanted to conjure up a more insidious villain you would be hard put to find anyone more absolutely evil than Anas. When Levin finally saw Anas for the first time – and he made sure that he was carefully hidden so that Anas did not see him, he was blown away by Anas’s physical appearance: A massive six foot five, so muscular that he said Anas’s wrist was as big as Levin’s thigh. (It turns out that Anas was a steroid junkie, which both explained his enormous physique and the almost constant bouts of rage to which he was prone.)
And, although you can’t help but fear for Levin as he entered into the proverbial lion’s den, knowing that this is a true account, the overriding question as he describes his eventual face to face encounter with Anas, was how was he going to pry information out of someone who, it turns out, was actually capable of killing his own child to exact revenge on a wife who dared to leave him.
“Proof of Life” was just recently published (in 2021, as a matter of fact) and the copy I was sent was a review copy. But, as I was reading this incredibly fascinating book (and I know I use that phrase all too often in describing books that I love), I kept thinking to myself: All right, we know that Israel is engaged in an ongoing war of sorts with Iran in Syria, as Iran uses Syria as its base for arming Hezbollah, and that threatens to turn into a major all–out war with Hezbollah, but what of the actual conflict in Syria itself between Assad and all those factions that were fighting his regime? Has it all quieted down or are we just not hearing about it any more?
Here’s the answer, as Daniel Levin writes in his postscript to “Proof of Life” (and again, it was just written in 2021):
“These days, conventional wisdom holds that the conflict in Syria has been decided. The war is over. Bashar al-Assad and his regime won with the help of Iran, Russia, and Hezbollah; the opposition, the Kurds, and ISIS were defeated. Sure, some nasty things did happen, but it’s time to move on and rebuild the country.
“Turns out, conventional wisdom is not particularly wise. This war is not over. The killings have not stopped. The chemical gassings, the cluster bombs, the executions, the torture, the human trafficking the annihilation of entire villages – they all continue. For millions of trapped Syrians, the nightmare never ends. A small group of privileged men connected to the regime through family or business have amassed unimaginable fortunes as they control the war economy, trading everything – food, medicine, fuel, heating, oil, drugs, weapons, prisoners, young girls – and looting the destroyed cities for scrap metal, copper, steel, and anything of value. Like in all war, the only ones left are a few extremely rich individuals and many extremely poor people. Everyone in between has been wiped out. Yes, the war economy is alive and well, and this war will last as long as that remains the case.”
The insights that Levin offers throughout this book – and what I just quoted is but one example of the level of knowledge that he brings forth about of what is really going on in Syria – may differ from commonly accepted wisdom about what has happened in Syria of late. Yet, Levin’s profound understanding of the Middle East left me with only one conclusion about the Arab world: It is a cruel jungle, often surrounded by a façade of material wealth that only disguises the fact that it is thoroughly tribal in nature – and an extremely dangerous world in which to set foot.
Lucky for the Israelis who are now establishing connections throughout much of the region – they know what they’re getting into. They’ve been operating in what is probably the most dangerous neighbourhood in the world for a very long time. I’m sure that Israel has a lot of Daniel Levins around who know how to negotiate their way through the metaphorical landmines into which Israel is now stepping.
“Proof of Life” is set to be released to the public in May 2021.
Features
Securing Your Account on PHBingo Login (GameZone)

The rising popularity of online casino platforms like GameZone has attracted many players eager to indulge in their favorite bingo games. As the number of users grows, so does the need for account security. Protecting personal data, playing progress, and account wallets has become vital due to the increase in online threats. Learning effective security techniques for PHBingo Login (GameZone) is essential for players, ensuring both safety and uninterrupted gameplay.
GameZone, a platform that features traditional and modern bingo games, stores sensitive information about user details, progress, and financial data. Without proper precautions, accounts may fall victim to unauthorized access, leading to loss of control, misuse of credentials, and exposure to significant risks. Following preventative measures will allow players to enjoy their favorite games worry-free.
Risks of Unauthorized Access in Online Bingo Play
Players using GameZone or similar platforms need to consider the potential consequences of compromised accounts. The inability to access an account, unauthorized transactions, and losing virtual credits are common issues resulting from poor security. Personal data, such as email addresses or payment information, is also at risk once hackers gain access.
While online casino platforms offer built-in security mechanisms, users carry the responsibility of implementing their own account protection solutions. Taking proactive steps, such as using strong passwords and enabling additional security layers, greatly reduces exposure to risks.
Steps to Secure Your PHBingo Account
1. Set a Strong, Unique Password
Having an easily guessed password, like “123456” or a birthdate, leaves accounts highly vulnerable. Strong passwords are critical for better security and protecting login details.
Strong password elements to consider:
- A combination of uppercase and lowercase letters
- Numbers and symbols
- A length of at least 8–12 characters
Using different passwords for each account ensures that other platforms won’t be compromised if one is hacked. Players should create passwords that are unique and hard to decipher.
2. Enable Two-Factor Authentication (2FA)
Two-factor authentication (2FA) provides an additional security layer on GameZone online platforms. When enabled, it requires a secondary verification code sent to a user’s mobile phone to complete the login process.
Benefits of using 2FA:
- Prevents unauthorized access, even if passwords are exposed
- Adds extra verification for every login attempt
This security feature is highly beneficial for players frequently engaging in multiplayer bingo games or downloading game applications. Gamers reduce unauthorized access risks significantly by implementing 2FA.
3. Avoid Logging in Over Public Wi-Fi
Connecting to GameZone through public Wi-Fi networks puts users at risk. Public or unsecured networks allow cybercriminals to intercept data on the network, including login credentials.
Safer alternatives include:
- Using private and secure network connections at home.
- Avoiding logins from shared or public devices.
- Relying on mobile data for safer gameplay while traveling or away from home.
These preventive measures ensure a secure experience, wherever the player may be.
4. Update Devices and Apps Regularly
Neglected updates on devices or casino platforms expose users to software vulnerabilities. Regular updates deliver patches and fixes to enhance protection against hackers.
Best practices for keeping systems updated:
- Install updates for operating systems and browsers at regular intervals.
- Download GameZone apps and updates officially from trusted sources.
- Avoid using third-party versions of GameZone applications.
Updated devices and applications offer smoother and more secure sessions, ensuring that accounts remain safeguarded.
5. Log Out After Playing Sessions
Failing to log out from GameZone accounts increases the risk of unauthorized access, especially on shared or public devices. Ensuring account disconnection after gameplay is a simple yet effective habit.
Steps to improve logout practices:
- Avoid saving login details when using shared devices.
- Clear cache and browsing data after accessing accounts.
- Make it a point to log out systematically after every session.
Regularly logging out minimizes the chances of account breaches and maintains better security for PHBingo accounts.
6. Beware of Phishing Scams
Phishing scams involve fake emails or messages impersonating official GameZone communications to trick players into revealing login information. These scams often include links to malicious websites posing as the platform’s login page.
Signs of phishing schemes include:
- Emails claiming “urgent account issues” requiring immediate action
- Links to web pages that request sensitive login credentials
- Emails sent from domains that look unofficial or are oddly spelled
Players should always enter their credentials through the official GameZone login page rather than clicking on suspicious links to avoid falling victim to such scams.
7. Monitor Account Activity Regularly
Checking account activity makes it easier to detect and resolve suspicious behavior or unauthorized logins. Reviewing recent account use helps players pinpoint breaches quickly.
Effective steps to manage account activity:
- Change passwords immediately if irregular activity appears.
- Reach out to GameZone support for assistance with securing compromised accounts.
- Monitor recent logins and transactions for unrecognized activities.
Tracking account patterns ensures issues are addressed early, making it easier to control risks.
8. Use Secure Payment and Transaction Methods
Online bingo often involves linking accounts with payment methods. Securing financial data ensures that sensitive information isn’t exploited or mishandled.
Practical payment security tips include:
- Using verified and reputable payment gateways.
- Avoiding unauthorized transactions or sharing of payment details.
- Double-checking URLs to ensure the payment page is official and secure.
Secure payment methods enhance the overall user experience while providing peace of mind for frequent players.
9. Avoid Sharing Account Credentials
Sharing login information with others, even with close friends, increases the risk of unauthorized access or account misuse. Keeping accounts private ensures better control over personal playing progress.
Reasons to avoid sharing login details:
- Reduces the possibility of accidental account misuse.
- Preserves account integrity and progress.
- Prevents unknown individuals from accessing personal information.
Limiting account sharing eliminates these risks and ensures safety for all users.
10. Focus on Responsible Practices Alongside Security
Combining security precautions with responsible practices allows for a safe and balanced experience. GameZone promotes responsible practices by offering reminders and restrictions that prevent excessive gameplay.
By maintaining both security and healthy habits, players can enjoy a fun, worry-free environment.
Enhancing GameZone Experiences Through Security

Secure play for PHBingo accounts begins with adopting strong cybersecurity habits. Simple measures like using complex passwords, enabling two-factor authentication, and avoiding suspicious links create a robust system of protection. Regular account monitoring and updates further help reduce risks associated with online threats.
By reinforcing security steps, users gain confidence in their platforms, ensuring they can focus on enjoying PHBingo and other offerings worry-free.
Features
Today’s Antizionism is Jew-Hatred

By HENRY SREBRNIK The Jewish world has grown darker. I’m not going to compare the anti-Jewish hate that has spread across this and other countries since October 7, 2023, to the Holocaust, but we know that Jewish life has become far more precarious. And so much of the hatred flies under the rubric of so-called “antizionism,” with people claiming that this isn’t “antisemitism.” But this is a false dichotomy. And we know it when we see it.
“Antizionism” is not about the now arcane historical debates that occurred mainly within Jewish communities from the 19th century through 1948, in which those who became Zionists sought to actualize the Jewish ties to biblical Israel and recreate a modern state. By “Zionists,” today’s enemies are not referring to supporters of the 19th century self-liberation movement of the Jewish people, whose goal was to establish a national home. They known little of this history. They’ve never heard of Theodor Herzl, Ahad Ha’am, Ber Borochov, Ze’ev Jabotinsky, or Chaim Weizmann.
As a derogatory slur, a pejorative, it simply means “Jew,” the way earlier words, now archaic, used to. Some call Jews “Zios.” They mean the Jewish people, who exist in opposition to everything good in the world, and who are figures of emblematic wickedness. In this they simply update what Nazis said a century ago. Hitler, too, was an “antizionist,” along with his racial antisemitism. It attacks Jews, here in Western countries like Canada – in the cities where they live, in the universities they attend, in the publishing houses where they send their manuscripts, and in the entertainment world where they act and sing.
Note that it calls itself antizionism, not anti-Israelism, so that the net can grab virtually every Jew who simply wants to see Israel not destroyed – and that’s the vast, vast majority. We Jews know what it means, regardless of what our enemies claim. Would anyone think that the term antisemitism means hatred of Semites?
Clearly a ludicrous idea; it was invented in the 19th century by a German Jew-hater, Wilhelm Marr, to make it sound more “racially scientific.” No one is fooled by that, of course, nor should they be by so-called “antizionism.” In its effects, it is for Jews a distinction with a negligible difference. It is meant to portray Jews as villains, and while it may fool some gullible people, it will deceive very, very few of us.
After all, as Michel Coren noted in “Roald Dahl’s Antisemitism Feels Painfully Familiar,” in the British magazine the Spectator March 16, “most Jewish people do in fact to varying degrees support Israel, partly because centuries of bigotry, violence, massacre, and attempted genocide have given them little alternative. They may oppose Israeli policy, may condemn the current government, may even want radical compromises, but there’s still support. And in the current climate of leftist and Islamist triumphalism, it’s all Zionism and none of it acceptable.”
Anti-Zionism is marked by three core “libels”: that “Zionists” are colonizers, guilty of apartheid, and committing genocide. (Actually, the only time we were settler-colonialists was when we conquered Canaan, but that was God’s doing!) Anti-Israel activists incorporate historical manifestations of anti-Jewish discrimination under the guise of anti-Zionist political activism, from the blood libel to Nazi-era tropes, mixed with contemporary academic theories. Anti-Zionism acts as a container for these historical tropes, blending them together with progressive talking points.
George Washington University professor Daniel Schwartz, in “Vocabulary Lesson,” Jewish Review of Books, Spring 2026, describes a pro-Palestinian demonstration in 2025 at his campus where a student held a placard with Israel at the center and spokes radiating outward to other evils: imperialism, white supremacy, even reproductive injustice. “This is not garden-variety political criticism of Israel policies or conduct. It invokes a symbolic architecture in which the Jewish state becomes the universal source of global suffering — a structure with deep resonance in antisemitic thought.”
Scholars argue that it is the third major iteration of discrimination against Jews. The first was anti-Judaism, based on religion, the second was antisemitism, focused on race, and the third, anti-Zionism, is a hatred of Jewish peoplehood.
“Anti-Zionism transforms the very meaning of Zionism,” contends Adam Louis-Klein. “The Jew is reconstructed through a new symbolic logic and a new repertoire of stereotypes.” Where antisemites invoked the pseudo-biological figure of “the Semite” to cast Jews as an Oriental race infiltrating the West, anti-Zionists invoke the authority of the social sciences to recode the Jew as the “Zionist,” a European colonizer destined to commit genocide of a non-European population.
“Erasing Jewish indigeneity and severing Jewish belonging to the land of Israel, anti-Zionism transforms the race polluter of antisemitism into the white settler of anti-Zionism,” he asserts in his March 24, 2026 Free Press article “Yes, Anti-Zionism Is Discrimination.”
For this reason, he writes, it’s imperative that organizations and institutions committed to protecting Jews and fighting the scourge of Jew-hatred start condemning—clearly and without apology—antisemitism and antizionism. This goes to the moral core of the matter: the right of Jews to a homeland versus the bigotry of those who deny them that right.
After the Holocaust, explicit Jew-hatred became unfashionable in polite society, but the impulse never disappeared. The workaround was simple: separate Zionism from Judaism in name, then recycle every old anti-Jewish trope and pin it on “the Zionists.”
Henry Srebrnik is a professor of political science at the University of Prince Edward Island.
Features
Artificial Intelligence, Sports Data, and What It Means for Community Values

Explore how artificial intelligence in sports data reflects broader societal changes, raising questions about ethics, transparency, and community values in a digital world.
Artificial intelligence is becoming an increasingly visible part of modern life, shaping how information is analyzed and decisions are made. While often discussed in fields such as healthcare, finance, and education, sports analytics provides a particularly clear example of how these systems function in real time. For many readers, the relevance of this topic goes beyond sports itself and speaks to broader questions about technology and community values.
Within Jewish communities, where education, critical thinking, and ethical responsibility have long been central principles, the rise of AI invites meaningful discussion. Understanding how automated systems operate is not only a technical issue but also a cultural and intellectual one. In global digital environments, references to platforms such as 1xbet Republic of Ireland often appear in discussions about real-time data processing, illustrating how widely these technologies are applied.
From Human Judgment to Algorithmic Thinking
Traditionally, interpreting sports performance required human observation and experience. Analysts would review statistics, assess player form, and make informed judgments based on knowledge built over time. While this method remains valuable, it is now being supplemented by artificial intelligence.
AI systems can process large volumes of data instantly, identifying patterns and trends that might otherwise go unnoticed. This shift reflects a broader movement toward algorithmic thinking—where decisions are increasingly informed by data rather than intuition alone.
For communities that place a strong emphasis on learning and inquiry, this raises important questions. How should data be interpreted? What role should human judgment continue to play? And how do we ensure that reliance on technology does not replace thoughtful analysis?
What AI Systems Analyze
Modern AI models draw on a wide range of data inputs to generate insights. In the context of sports, this includes:
- real-time performance data
- historical comparisons
- individual player metrics
- behavioural patterns
- external conditions
The ability to integrate these variables allows AI to produce highly detailed assessments. However, it also creates a layer of complexity that is not always easy to understand.
This challenge is particularly relevant in educational settings. As younger generations become more familiar with technology, there is a growing need to teach not only how to use these systems, but also how to question and evaluate them.
Ethics, Transparency, and Responsibility
The increasing role of AI naturally leads to ethical considerations. In Jewish thought, concepts such as responsibility, fairness, and accountability are deeply rooted and widely discussed. These ideas are highly relevant when considering how automated systems are designed and used.
One of the key concerns surrounding AI is transparency. When decisions are made by complex algorithms, it can be difficult to understand the reasoning behind them. This raises questions about trust and oversight.
Ensuring that AI systems are used responsibly requires a balance between innovation and ethical awareness. Community dialogue plays an essential role in this process, helping to define how technology should align with shared values.
A Community Conversation About the Future
The use of artificial intelligence in sports analytics may seem like a narrow topic, but it reflects a much larger transformation. Across many areas of life, data-driven systems are becoming the norm, influencing how information is processed and decisions are made.
For Jewish communities, this moment presents an opportunity for reflection and engagement. By approaching technology with curiosity, critical thinking, and a strong ethical framework, it is possible to better understand both its potential and its limitations.
Ultimately, the conversation about AI is not just about technology. It is about how communities adapt, preserve their values, and shape the future in a rapidly changing world.


