Features
Fredelle Bruser Maynard’s centenary and remembering “Raisins and Almonds”
 By IRENA KARSHENBAUM While out walking recently, I came across a copy of “Confederacy of Dunces” by John Kennedy Toole in one of those free little libraries. Now the book doesn’t fit into my criteria of rare, lost or out-of-print works that I am usually on the hunt for, but knowing that this is one of the great American classics of the 20th century, which I had not yet read, I started reading it on the spot while thinking, can people see me from their front windows and think I’m like rummaging through their garbage?
By IRENA KARSHENBAUM While out walking recently, I came across a copy of “Confederacy of Dunces” by John Kennedy Toole in one of those free little libraries. Now the book doesn’t fit into my criteria of rare, lost or out-of-print works that I am usually on the hunt for, but knowing that this is one of the great American classics of the 20th century, which I had not yet read, I started reading it on the spot while thinking, can people see me from their front windows and think I’m like rummaging through their garbage?
I quieted the noise in my head, and concentrated on the lively story of the publisher, Walker Percy, recounting how he first came across the work; the mother of the author who turned out to be dead, started calling him incessantly, and in an attempt to push her off, Percy asked why he should read the book, only to be told that it was a “great novel.” (Many readers know how this story ends, the book won the Pulitzer Prize eleven years after the author’s suicide, thanks to Percy publishing the work.)
My search-for-publisher story is the exact opposite. For years, my mother knew I was writing a book and was after me to read it. Finally, I acquiesced and emailed her the manuscript. A few weeks later, my mother called and told me she nearly vomited when she got to the part where the main character masturbates (can I use this word in a PG-rated community newspaper?) and then asked me if I seriously thought someone would publish my book.
So, if I were to run a garden hose from the exhaust pipe into my car, while securing myself tightly inside (I have no inclination to do so), I know for a fact my mother will never make a nuisance of herself with some publisher. What I am trying to say here, is that every writer needs a champion. Just one. Toole had Walker Percy, and his mother. That’s two, hence the Pulitzer Prize. Franz Kafka had Max Brod. Anne Frank and Julia Child had Judith Jones. (Anne Frank also had her father.) I don’t have one, not even my mother. Now, Dear Reader, please don’t think my mother is some horrible person. She makes me blintzes and borscht and sends me home with massive care packages. It’s just that she couldn’t get past the masturbation scene, which she may be right about because when it comes to literary fiction, Sex. Does. Not. Sell.
Writers need champions not only to get published, but also not to get forgotten, as so many good books suffer this fate. My tale continues.
On another recent walk I was rummaging through a different free little library that was full of Catholic titles. I zeroed in on “Christ Stopped at Eboli” with a sketch of a cross as the backdrop for a crucified figure. I wasn’t about to take this book home with me. But then it was as if time had stopped. My breathing seized. Pudgy cupids fluttered in front of my eyes playing their little harps as my eyes rested on the name of the author — Carlo Levi. I pulled out my phone and googled the name. Italian. Jewish. Doctor. Painter. Author. Detained during the 1930s for his anti-Fascist activities in an impoverished Italian town, the memoir recounts this time. Fits my criteria: rare, lost and/or out-of-print, not to mention, fascinating time and place. I placed the book snuggly under my arm pit, looked around for any judging eyes and slunk away like some satisfied thief with her precious plunder.
I won’t be retelling the story of “Christ at Eboli” here because I’ve only just started reading it — it is good, so far — but I’ve brought the work to your attention so go find a copy and read it!
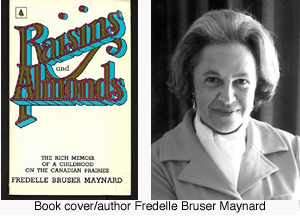
I’ve flown to Tasmania and back to make my convoluted points and have to get to the story I promised Bernie, “Raisins and Almonds,” a memoir by Fredelle Bruser Maynard. This book is not exactly forgotten because one thing I know about Winnipegers is that they are very cultured people and are faithful followers of their great literary tradition. The book is a quiet masterpiece that deservers to be remembered, celebrated and introduced to younger readers.
Originally published in 1972, it was one of the first Jewish memoirs to be published by a major publisher, Doubleday Canada Limited, and received wide-spread acclaim. Today, it is sadly out-of-print. I got my copy, luckily, when the Jewish Historical Society of Southern Alberta was purging its library — Fredelle Bruser Maynard belongs to Saskatchewan, to Manitoba, she is not “ours” they said — and knowing my interests post-publication of “Remembering a forgotten book, Winnipeg Stories” (in this newspaper), triumphantly handed me the fragile copy.
Through a series of short stories, “Raisins and Almonds” recounts the author’s life growing up in the 1920s and ‘30s in Saskatchewan and Manitoba. The memoir doesn’t pull at the heartstrings; it rips out the heart.
In a Jewish Christmas, Bruser Maynard writes about what it was like to be the only Jewish child in a small Saskatchewan town, in Birch Hills, during the Christmas season, “Christmas, when I was young, was the season of bitterness.” The story is painful to read not because little Fredelle is not like the other children and can’t have a Christmas tree or Christmas presents or is even cruelly taunted in the playground for having “killed Christ.” All of these experiences are hard and traumatic for a child to endure. What is so painful about this story is the vulnerability of the parents who at their core feel inferior as Jews and who will do anything — even have their child, “the town’s most accomplished elocutionist,” recite a Christmas poem at the yearly Christmas concert — for a scrap of Gentile acceptance. Of course, the Brusers are not the first Jews in history to hide or compromise their identity; Jewish pride or confidence is probably more of a historic rarity that flourishes when we have the good fortune to live in a Jewish golden age.
In The Silk Umbrella, the author describes her father’s loneliness and alienation being the only Jewish man living in one prairie town after another, “He had no friends but us. Would it have been different in the city, in a Jewish community? I don’t know. But certainly, marooned on the prairies, an island of Jewishness in a barbarian sea, he never formed ties beyond the limits of his business life….. He talked crops with farmers, theology with the local minister, household matters with women. But he would no more have thought of accompanying a farmer to the beer parlor than, years before, he could have joined a Cossack on a gallop across the steppes.”
Born in 1922, in Foam Lake, Saskatchewan, to Boris and Rona Bruser, Fredelle describes her childhood as growing up in a family “where women mattered” and as a result was able to pursue degrees from the University of Manitoba, University of Toronto and obtained a Ph.D. in English Literature from Radcliffe College (Harvard University). She married her former professor, Max Maynard, “the son of a Protestant clergyman,” which she wrote about in The Silk Umbrella. The interfaith marriage irrevocably damaged her relationship with her father, “Always a demonstrative man, my father embraced me very seldom after I married. In this new reserve, there was no hint of reproach. I remained his own dear child. Whatever had gone wrong, the fault must be his. If he had given me a proper Jewish education….”
The couple had two daughters, Rona Maynard and Joyce Maynard, both of whom followed their mother in her literary path. Joyce Maynard, as a teenager, briefly lived with J.D. Salinger, who was more than 30 years her senior, and wrote about the time in, “At Home in the World: A Memoir.”
My PaperJacks edition of “Raisins and Almonds,” that originally sold for $1.95, includes a number of review quotes, one being from Margaret Laurence, “Fredelle Bruser Maynard… communicates the sadness at the core of laughter… Her memoirs are so authentically prairie, Depression prairie, but they reach out far beyond any place or time.”
“Raisins and Almonds” remains as true now as when crisp copies lined book store shelves 50 years ago when it was first published. If only this beautiful book would be re-released today.
Irena Karshenbaum writes in Calgary irenakarshenbaum.com .
Features
A Jewish farmer broke ground on a synagogue in an Illinois cornfield. His neighbors showed up to help.

By Benyamin Cohen May 8, 2026 “This story was originally published in the Forward. Click here to get the Forward’s free email newsletters delivered to your inbox.”
Benyamin has been reporting for more than a year on the improbable story of Nik Jakobs. Catch up here and here, and stay tuned for a forthcoming piece about a trip they took to the Netherlands to visit the towns where the Jakobs family survived the Holocaust. Yesterday was an important moment in Jakobs’ overall journey, and we wanted to share it with you.
STERLING, ILLINOIS — On Wednesday, Nik Jakobs was planting corn. On Thursday, the 41-year-old Illinois cattle farmer stood in a two-acre cornfield preparing to plant something else: a synagogue.
Around 75 people gathered on the edge of the field this week in Sterling, Illinois, a two-hour drive west of Chicago, where Jakobs and his family broke ground on a new home for Temple Sholom, the small congregation that has anchored Jewish life here for more than a century, and where his family has prayed since the 1950s.
The planned 4,000-square-foot building will also house a Holocaust museum inspired by the story of Jakobs’ grandparents, Edith and Norbert, who survived the war after Christian families in the Netherlands hid them in their homes for years. Jakobs described the future museum as a place devoted not only to Jewish history, but to teaching the dangers of hatred and division. “If you have the choice to be right or kind,” he said, repeating advice from his grandmother, “choose kind.”
A 60-foot blue ribbon — chosen by Jakobs’ wife, Katie, to match the color of the Israeli flag — stretched across the future building site. His four daughters held it alongside his parents, brothers and friends. Then they lifted oversized gold scissors and cut the ribbon as pastors, farmers, city officials and members of neighboring churches applauded.
The synagogue rising from this Illinois cornfield will house pieces of the past.
A nearby storage area holds Jewish objects Jakobs rescued from shuttered synagogues across the country: stained-glass windows, Torah arks, rabbi’s chairs, memorial plaques and wooden tablets engraved with the tribes of Israel. Many came from Temple B’nai Israel, a 113-year-old synagogue that closed down in 2025. It served generations of Jews in McKeesport, Pennsylvania, now a ghost town since the steel mills closed. Its remaining congregants donated sacred objects to Jakobs so their story could live on rather than disappear.
The day before the groundbreaking, the Jakobs family began opening some of the crates for the first time since they were packed away nearly a year ago. Nik’s father, Dave Jakobs, pried open one box with a hammer and crowbar while Nik loosened screws with an electric drill, the family gathered around like archaeologists opening a tomb.
Inside was a stained-glass window with images of a tallit and shofar bursting in jewel tones of blue, yellow and red. Jakobs’ mother, Margo, lifted Annie, the youngest of Nik’s daughters, so the 4-year-old could peer inside. The bright red glass matched the bow in her hair.
Nearby sat the massive wooden ark salvaged from Pennsylvania, topped with twin Lions of Judah whose carved paws once overlooked generations of worshippers.
Faith on the farmland
Temple Sholom — founded in 1910 — was once the center of Jewish life in Sterling, a town of 14,500 surrounded by flat farmland and tall grain silos. Its Jewish community once included a pharmacist, the manager of Kline’s department store and the owner of a local McDonald’s franchise.
Over time, membership dwindled. The roof sagged. The pews emptied.
Last year, the congregation sold its aging building and relocated High Holiday services to a tent on the Jakobs’ farm, where prayers mingled with the smell of manure and cattle lowing nearby.
At a moment when many small-town synagogues are closing, Temple Sholom is doing something increasingly rare: building a bigger new sanctuary from scratch. The synagogue will sit prominently along one of Sterling’s main roads — a highly visible expression of Jewish life in a region where Jews are few.
Thursday’s groundbreaking took place on the National Day of Prayer, the annual observance formalized under President Ronald Reagan, who grew up a few miles away in Dixon, Illinois. Earlier that morning, attendees gathered inside New Life Lutheran Church for a breakfast sponsored by Temple Sholom.
“I was so happy to see bagels, lox and cream cheese,” said Rev. James Keenan, a Catholic priest originally from Brooklyn. “It reminded me of home.”
Inside the church sanctuary, a large wooden cross glowed amber and blue above the dais while two giant screens displayed the National Day of Prayer logo. Jakobs, wearing cowboy boots, jeans and a powder-blue blazer, addressed the crowd.
“Tolerance is not weakness,” he said. “It is strength.”
The new synagogue will sit beside New Life Lutheran Church on land sold to Temple Sholom by farmer Dan Koster, 71, who has known the Jakobs family for three generations.
“We need more religious presence in the community,” Koster said.
For Drew Williams, New Life’s 38-year-old lead pastor, the synagogue and museum represent more than neighboring buildings. His church already hosts food-packing drives, summer meal programs and community events. He imagines future partnerships with Temple Sholom.
“I don’t think there’s any community that is immune to hate,” Williams said. “That just means it’s on us” to be on the other side “spreading peace.”
Sterling Mayor Diana Merdian, who is 41 and grew up in town with Jakobs, said the project reflects a broader desire among younger generations to preserve local history and identity. “If we don’t carry those stories, we lose them,” she said. “Once you lose that, you can’t get it back.”
During the ceremony in the cornfield, Temple Sholom’s longtime cantor, Lori Schwaber, asked those gathered to remember the congregation’s founding members and recite the Mourner’s Kaddish together. Jews and Christians stood side by side in the prairie wind as Hebrew prayers drifted across the open farmland.
Lester Weinstine, a 90-year-old congregant who was the first bar mitzvah at Temple Sholom when the shul was still housed out of a Pepsi bottling plant, looked out across the field in disbelief. “I never thought I would see this,” he said.
For Jakobs, the synagogue project has become inseparable from the lessons his grandparents’ survival taught him. “You sometimes feel on an island as a Jew, especially in rural America,” he said. “But this community — that’s not what I’ve experienced here.”
If construction stays on schedule, the synagogue will open in fall 2027. Its first major service will not be a dedication ceremony, but the bat mitzvah of Jakobs’ oldest daughter, Taylor.
Members of the Pennsylvania congregation are planning a bus trip to Illinois for the occasion, after donating many of their sacred objects to help build Jakob’s synagogue. Their former rabbi has offered to officiate.
“If a farmer can build a synagogue in a cornfield,” Jakobs said, “anybody can do it anywhere.”
Benyamin Cohen is a senior writer at the Forward and host of our morning briefing, Forwarding the News. He is the author of two books, My Jesus Year and The Einstein Effect.
This story was originally published on the Forward.
Features
Ancient Torah Lessons Students Can Still Use Today In Class
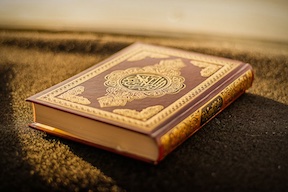
Texts don’t survive through age alone; they survive because each generation finds something new and intriguing in them. One such text is the Torah. Students will find it useful in classes ranging from religion to philosophy, literature, or cultural studies, but many of its teachings aren’t confined to the past either. Stories from the Torah touch upon topics like stress, conflict, leadership, confusion, errors, accountability, and meaning. It sounds remarkably contemporary.
A student approaching the study of Torah has several options: religious text, historical source, literary piece, and a basis for philosophical contemplation. They all provide opportunities to explore the text in unique ways. The student writing on ancient texts or ethics can use EssayPro, the company employs experts, including Paul S., a full-time writer, who could assist the student with structuring their research. But great essays on ancient texts require more than just the approach of a museum curator.
The goal is not to shoehorn ancient narratives into a modern form or to look for an easy life hack in every single passage. Rather, students need to think about what made those stories stand the test of time. What did they observe about people? What did they try to warn against? And last but not least, what virtues did they celebrate? As soon as students start asking such questions, the Torah appears much closer.
Ancient Texts Teach Students To Be Patient Readers
Modern students are trained to read quickly. Just skim through the article. Scan all the comments. Read the summary and move forward. It does not quite work with the Torah, though. Many of the passages are rather short but rich in conflict, repetition, silence, and subtle details. Sometimes a person’s name, a long journey, an order given, or even a family squabble means more than expected.
For this reason, it is a great practice for students to deal with, as education is mostly geared toward finishing chapters faster, submitting assignments sooner, and hitting deadlines regularly. However, profound reflection requires patience, and the Torah is the perfect tool.
This type of reading goes past religious education alone. Students who learn to pace themselves with Torah can carry this approach into their literature, legal, historical, philosophical, and even scientific readings. Details are crucial. Contexts are crucial. Silence is equally crucial to speech.
Questions Do Not Denigrate One’s Faith Or Cognition
One of the best lessons for students from the Torah is that sincere people pose serious questions. The texts are full of debates, disagreements, doubts, tests, and misunderstandings. The addressees do not understand the demands placed on them. They argue, they bargain, and sometimes make mistakes.
It is necessary for the reason that many students view good studying as a process of getting clear and immediate responses to questions. It is usually not the case. Learning can start from frustration and confusion, since such a passage can serve better than an easy one.
During lessons, students should not fear questioning why a character did something like that, what their motivation was, what the possible consequences of their actions were, how it was perceived at that time, or how other cultures interpret the passage. Asking questions neither denigrates the subject nor learning itself.
Responsibility Is Greater Than Personal Success
In contemporary educational circles, the discourse of success often revolves around the personal gain that follows from achievement. Earn good grades. Construct your résumé. Land scholarships. Map out your future career path. On numerous occasions, the Torah asks a much larger question: what are our obligations to one another?
Themes associated with the concepts of justice, community, caring for the weak, honesty, and responsibility recur regularly throughout the work. These recurring motifs serve to undermine the narrow understanding of education and suggest that knowledge informs conduct.
To students, this message could be particularly relevant, as they face a daily opportunity to exercise their responsibility as members of the academic community. Education is more than a competitive pursuit, and the values that are promoted by the Torah can manifest themselves in group projects, class discussions, peer interactions, and other facets of college life.
Leaders Need Humility
Many students picture great leaders as people with big voices and confidence, who seem to have power from birth. Torah portrays leaders in a more complex way. They are hesitant, flawed, fearful, impatient, and highly human. Greatness is not portrayed as an absolute quality; rather, it is viewed as an ordeal.
This makes for some valuable insight for all those students who believe they lack “leader type” personalities. Leaders are not necessarily extroverts or people who get along easily with everyone else. Sometimes they speak up against injustice; at other times, they own up to their mistakes. Most of the time, they take responsibility even if it is hard.
This is also a useful perspective for all those people who lead student organizations and groups and manage projects for them. Being in charge doesn’t mean one can afford arrogance. A leader needs to know how to listen and learn, and leadership entails responsibility rather than power.
Memory Allows For Self-Understanding By Humans
There is a reason why the Torah speaks of memories time and again: remembering journeys, vows, commandments, failures, oppression, and liberation. This is not a form of nostalgia. Memories create identity. Memories tell people about their origin and things they cannot forget.
Students can take a lesson from it. In a world where everything keeps changing, memories may appear too slow or impractical. However, memories are useful to a student because they help one understand one’s place within a larger scheme of things. One learns about oneself through family history, national narrative, religious traditions, personal experience of migration, community experience, and culture.
It does not imply that students should blindly follow anything and everything handed down by others. Students should know where they stand and where they come from. Otherwise, they cannot make proper decisions in the present.
Features
Cricket in Israel: where it came from, why it’s barely visible, and who plays it today

Cricket made its way to Israeli soil back in the British Mandate period, and later got a boost from waves of immigration from India, South Africa, and the United Kingdom. Despite such a long history, it barely registers in the mainstream: it never found a place on TV, and the rules remain a mystery even to many sports journalists. Today, cricket grounds are used mostly by immigrants and a handful of local enthusiasts, for whom the game has become something far more than just a pastime.
The British trace and the first matches on Israeli soil
The history of cricket in the region goes back to the days when the British flag flew over Palestine. Officers and officials of the Mandate administration brought with them not only bureaucratic traditions, but also the habit of gathering on trimmed lawns with a bat and a red ball. For the local population, used to passionate football and fast-paced basketball, it looked utterly foreign: hours-long matches, strict white outfits, tea breaks.
The “exotic” sport was slow to take root. When the Mandate ended and the new state shifted to completely different priorities, cricket quietly slipped to the margins of the sports scene, surviving only in the memory of a few.
Waves of immigration that brought cricket back all over again
The game was given a second life by immigrants from countries where cricket was an everyday thing. People from India, South Africa, and England, as they settled in Israel, looked for familiar ways to spend their free time and quickly found one another. For them, a weekend match meant not so much sport as a way to unwind and speak their native language.
However, even within these communities, cricket never became a mass pastime. It remained an activity for a narrow circle, like home cooking—made for special occasions, not put on a restaurant menu.
Why cricket didn’t break into the Israeli mainstream
There are several reasons the game remains invisible, and each one on its own would already be enough:
- Competition with football, basketball, and extreme sports, which take viewers’ attention and sponsorship budgets.
- The near-total absence of cricket on TV and in major sports media.
- The complexity of the rules for newcomers: many Israelis still don’t see the difference between cricket and baseball.
- A cultural unfamiliarity with spending half a day on the field for a single match, watching tactical nuances from a blanket on the grass.
Taken together, this creates a situation where even the rare bits of cricket news slip past in people’s feeds unnoticed.
Who takes the field today
The core of the community is made up of students and IT specialists from India, engineers who arrived on work visas, and immigrants from South Africa and the United Kingdom. They’re joined by a small group of locals who discovered cricket while studying or traveling abroad.
For many of them, the ground turns into a space for cultural memory: Hindi and English can be heard, whole families come along, and children run around the field while their parents discuss the finer points of the last delivery. There are no roaring fan sections here, but everyone knows everyone, and the sense of belonging turns out to be stronger than in the stands at any stadium.
Where and how matches happen without a major league
A typical place to play: a park on the edge of town, a rented pitch, hand-marked lines. Organizers combine the roles of coaches, umpires, and commentators. Matches are put together on weekends, and the whole thing feels more like a club scene than a professional structure.
Everyday hassles have become part of the folklore: soccer players take over the field, the ball disappears into the bushes, someone among the key players can’t get away from work. Every attempt to organize a full match feels like tilting at windmills.
Cricket’s prospects: the barriers are stronger than the hype
You can count specialized fields across the country on one hand, government funding is minimal, and media attention goes to sports that are more spectacular and easier to understand.
Even so, things have started to move. Israel’s national team periodically plays in international tournaments, and every win becomes a small celebration for the community. Youth sections have begun to appear within communities—more like after-school clubs for now—and enthusiasts are experimenting with shorter formats to lower the barrier to entry for newcomers.
Does growth in betting activity point to cricket’s popularity?
An indirect indicator of interest in cricket in any country has long been activity in the online betting segment. Industry iGaming portals regularly publish regional statistics, and we reviewed data from several major bookmakers: 1xBet, PinUp, Melbet. On the website, in a review of the 1xBet cricket betting app, we learned that the number of downloads from Israel is still small, but a slight uptick is still being recorded. This matches the overall picture: the cricket community in the country is growing slowly but steadily, and the betting-platform figures only confirm a trend that enthusiasts can see on the ground, in person.
Cricket in Israel is unlikely to turn into a mass sport in the foreseeable future, but it continues to live on thanks to a resilient community of immigrants and local fans who keep the game going despite the circumstances and make it visible at least within its own small, if modest, world.



